A phishing email impersonating npm targeted a package maintainer by linking to a typosquatted domain, npnjs.com, which hosted a cloned npm website to steal credentials. The email failed multiple authentication checks, was flagged as spam, and involved sophisticated tactics like tokenized URLs and legitimate support links to increase credibility. #npm #npnjs.com #typosquatting
Keypoints
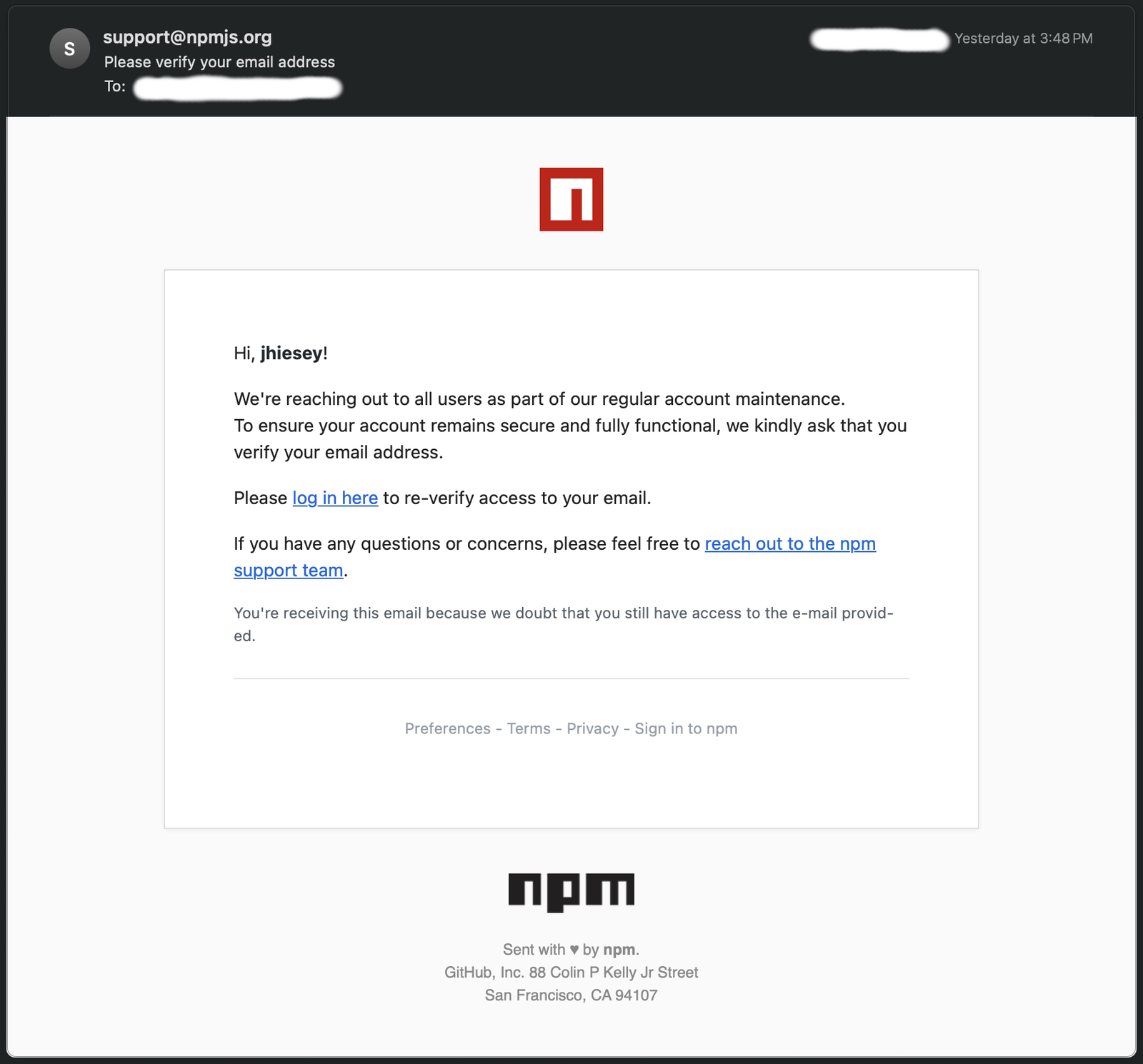
- A phishing email spoofed [email protected] and linked to npnjs.com, a typosquatted domain mimicking npm’s website to steal developer credentials.
- The phishing URL included tokens to track clicks and simulate authentic login sessions, targeting active maintainers with high impact.
- The email contained legitimate npmjs.com support links to increase its credibility and was delivered during off-hours to target victims more effectively.
- SPF, DKIM, and DMARC authentication checks failed, confirming the email was not from npm’s servers.
- Sender IP 45.9.148.108 is associated with malicious activity and hosted on a VPS commonly used for phishing campaigns.
- High-value targets like npm maintainers risk malicious code distribution if accounts are compromised.
- Security measures recommended include skeptical verification requests, using two-factor authentication, and rotating npm access tokens after suspicious activity.
MITRE Techniques
- [T1566] Phishing – Attackers sent a spoofed email impersonating npm with a link to a cloned website to steal credentials (“The phishing email urged the recipient to ‘log in here’ via a link…”).
- [T1078] Valid Accounts – Usage of tokenized URLs to track victim interactions and possibly simulate session authentication (“Attackers often use tokens to track who clicked the link or to pre-fill victim data on the phishing site.”).
- [T1586] Compromise Infrastructure – Hosting of phishing site on a VPS known for malicious campaigns (“The phishing email was sent via shosting-s0-n1.nicevps.net, a VPS host frequently used for malicious campaigns.”).
- [T1598] Phishing for Information – Employment of typosquatting domain npnjs.com to create a convincing fake login portal (“npnjs.com, a full copy or proxy of the npm website… aimed at stealing developer credentials.”).
Indicators of Compromise
- [Domain] Phishing domain impersonating npm site – npnjs.com
- [URL] Phishing login page URL – https://npnjs.com/login?token=
- [Email Address] Spoofed sender address – [email protected]
- [IP Address] Malicious sender IP with abuse reports – 45.9.148.108
- [Hostname] VPS hosting phishing email – shosting-s0-n1.nicevps.net
Read more: https://socket.dev/blog/npm-phishing-email-targets-developers-with-typosquatted-domain