The Greedy Sponge threat actor has targeted Mexican organizations since 2021 using a heavily modified AllaKore RAT and additional malware like SystemBC for financial fraud. Recent campaigns employ advanced techniques such as server-side geofencing and custom data exfiltration methods to evade detection and steal banking credentials. #GreedySponge #AllaKore #SystemBC
Keypoints
- Greedy Sponge is a financially motivated threat actor active since early 2021 targeting Mexican organizations across multiple industries.
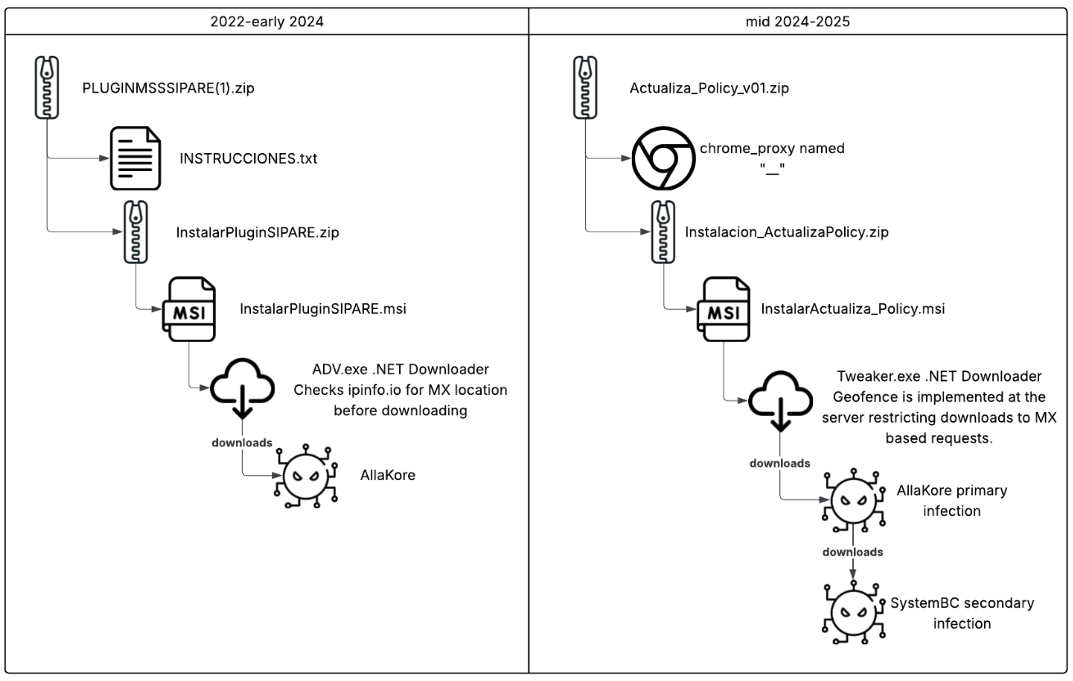
- The group uses custom packaged MSI installers delivering a modified AllaKore RAT capable of stealing banking credentials and authentication tokens.
- SystemBC, a multi-platform malware proxy tool, is deployed as a secondary infection to download and execute additional payloads.
- Recent campaigns moved geofencing from client-side .NET loaders to server-side checks to restrict payload delivery to Mexican IPs, enhancing stealth.
- Phishing and drive-by downloads are the primary attack vectors, often using zipped files containing legitimate proxies and trojanized installers with Spanish naming to lure victims.
- The threat actor maintains persistent infrastructure hosted on Hostwinds in Texas and domains registered outside the USA to limit law enforcement reach.
- They employ user account control bypass (using CMSTP) and PowerShell scripts to evade detection and maintain persistence on infected systems.
MITRE Techniques
- [T1591.001] Gather Victim Org Information: Determine Physical Location – Use of geofencing restricts malware execution to systems physically located in Mexico (“Attacker restricts the malware execution to systems physically located in Mexico”).
- [T1027.015] Obfuscated Files or Information: Compression – Delivery via zip files containing AllaKore RAT (“Zip files are delivered containing Greedy Sponge’s custom AllaKore RAT”).
- [T1218.007] System Binary Proxy Execution: Msiexec – Trojanized MSI files used to download custom AllaKore RAT (“A MSI file has been trojanized to download Greedy Sponge’s custom AllaKore RAT”).
- [T1204.002] User Execution: Malicious File – Execution gained by victims opening malicious files in zipped archives (“Greedy Sponge has gained execution through victims opening malicious files embedded in zip file”).
- [T1105] Ingress Tool Transfer – Download of custom AllaKore RAT (“Attacker downloads Greedy Sponge’s custom AllaKore RAT”).
- [T1059.005] Command and Scripting Interpreter: PowerShell – PowerShell script deployed for cleanup after RAT installation (“InstalarActualiza_Policy.msi deploys a PowerShell script for cleanup of the %appdata% directory”).
- [T1070.004] Indicator Removal: File Deletion – PowerShell script cleans up deployment directories to evade detection (“InstalarActualiza_Policy.msi deploys a PowerShell script to clean up the %appdata% directory used for downloading and deploying the RAT”).
- [T1132.001] Data Encoding: Standard Encoding – Base64 encoding used in .NET downloader requests (” .NET downloader has encoded requests with Base64″).
- [T1071.001] Application Layer Protocol: Web Protocols – Communication over HTTPS to download malware (“Attacker communicates over HTTPs to download the RAT”).
- [T1140] Deobfuscate/Decode Files or Information – Decompression of metsus.zip into executable AllaKore RAT (“metsus.zip is decompressed into kgm.exe, which is the AllaKore RAT”).
- [T1056.001] Input Capture: Keylogging – AllaKore RAT can perform keylogging on victims (“AllaKore RAT has the capability to keylog”).
- [T1113] Screen Capture – AllaKore RAT can take screenshots (“AllaKore RAT has the capability to take screenshots”).
- [T1547.001] Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder – RAT maintains persistence via startup folder (“Allakore RAT maintains persistence in the system using the startup folder”).
- [T1041] Exfiltration Over C2 Channel – Collected data exfiltrated to C2 servers (“Attacker copies collected information back to the threat actor’s servers”).
- [T1555] Credentials from Password Stores – Theft of credentials and tokens from banking sites (“Attacker has collected information about authentication on target banking sites, and steals authentication artifacts such as credentials and tokens”).
- [T1548.002] Abuse Elevation Control Mechanism: Bypass User Account Control – User account control bypass using CMSTP (“Pnp.exe is a user account control (UAC) bypass utilizing CMSTP compiled off this repo, or a fork”).
- [T1218.003] System Binary Proxy Execution: CMSTP – Use of CMSTP executable to proxy execution of malicious code (“Pnp.exe uses CMSTP, compiled from this repo or a fork, to bypass UAC”).
Indicators of Compromise
- [File Hashes] AllaKore RAT samples – e.g., 20fe630a63dd1741ec4ade9fe05b2e7e57208f776d5e20bbf0a012fea96ad0c0, f76b456cf2af1382325c704bf70b5168d28d30da0f3d0a5207901277e01db395, and multiple others.
- [File Hashes] .NET downloader samples – e.g., 8bf0d693033a761843ae20c7e118c05f851230cb95058f836ffe2b51770f788a, a83f218d9dbb05c1808a71c75f3535551b67d41da6bb027ac0972597a1fc49fe.
- [File Hashes] MSI installers – e.g., e848a0f1900e2f0be9ed1ea8e947ae3bae14e78f3ff81c02d8e5a54353cdbac8, b9bb43b725a454e826ab64fdd6256af809c60119dab2876d081b3721d226c672.
- [Domains] Phishing and C2 infrastructure – glossovers[.]com, logisticasmata[.]com, inmobiliariaarte[.]com, pachisuave[.]com (SystemBC C2), manzisuape[.]com (AllaKore C2), trenipono[.]com (Delivery), masamadreartesanal[.]com (Delivery).
- [IP Addresses] – 254.133[.]54 (Hostwinds server hosting phishing sites), 142.11.199[.]35 (trenipono[.]com C2 infrastructure).
Read more: https://arcticwolf.com/resources/blog/greedy-sponge-targets-mexico-with-allakore-rat-and-systembc/