Threat actors are exploiting SVG files to deliver obfuscated JavaScript that redirects victims to attacker-controlled sites with Base64-encoded tracking. This technique bypasses traditional detection by embedding malicious scripts in image files delivered via spoofed emails. #SVGSmuggling #JavaScriptRedirect #PhishingCampaign
Category: Threat Research

Google Threat Intelligence Group (GTIG) identified UNC6148 leveraging stolen credentials and deploying a persistent backdoor called OVERSTEP on SonicWall SMA 100 series appliances. The campaign involves sophisticated rootkit techniques for persistence and data exfiltration, posing risks of data theft and possible ransomware attacks. #UNC6148 #OVERSTEP #SonicWallSMA

NailaoLocker is a ransomware variant targeting Microsoft Windows that uses AES-256-CBC encryption combined with hard-coded SM2 cryptographic keys, including a rare built-in decryption function. Despite its embedded SM2 private key being non-functional in tests, the ransomware’s decryption logic works correctly with valid keys, suggesting it may be an internal test build. #NailaoLocker #SM2 #AES256CBC
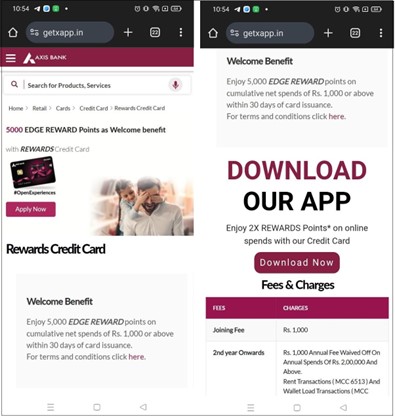
Cybercriminals are exploiting the popularity of cryptocurrency by distributing fake Android mining apps through phishing sites impersonating banks like Axis Bank, embedding XMRig to covertly mine Monero on victim devices. This malware operates stealthily by activating mining only when devices are locked, causing high CPU usage, device overheating, and potential hardware damage. #XMRig #AxisBank #Cryptojacking

Attackers exploited a compromised WordPress site by injecting malicious Google Tag Manager (GTM) scripts directly into the database, causing user redirection to a spam domain. This technique avoids file-based detection and has infected over 200 websites, demonstrating how trusted services like GTM can be abused for malicious purposes. #GoogleTagManager #WordPressInjection #spelletjes.nl
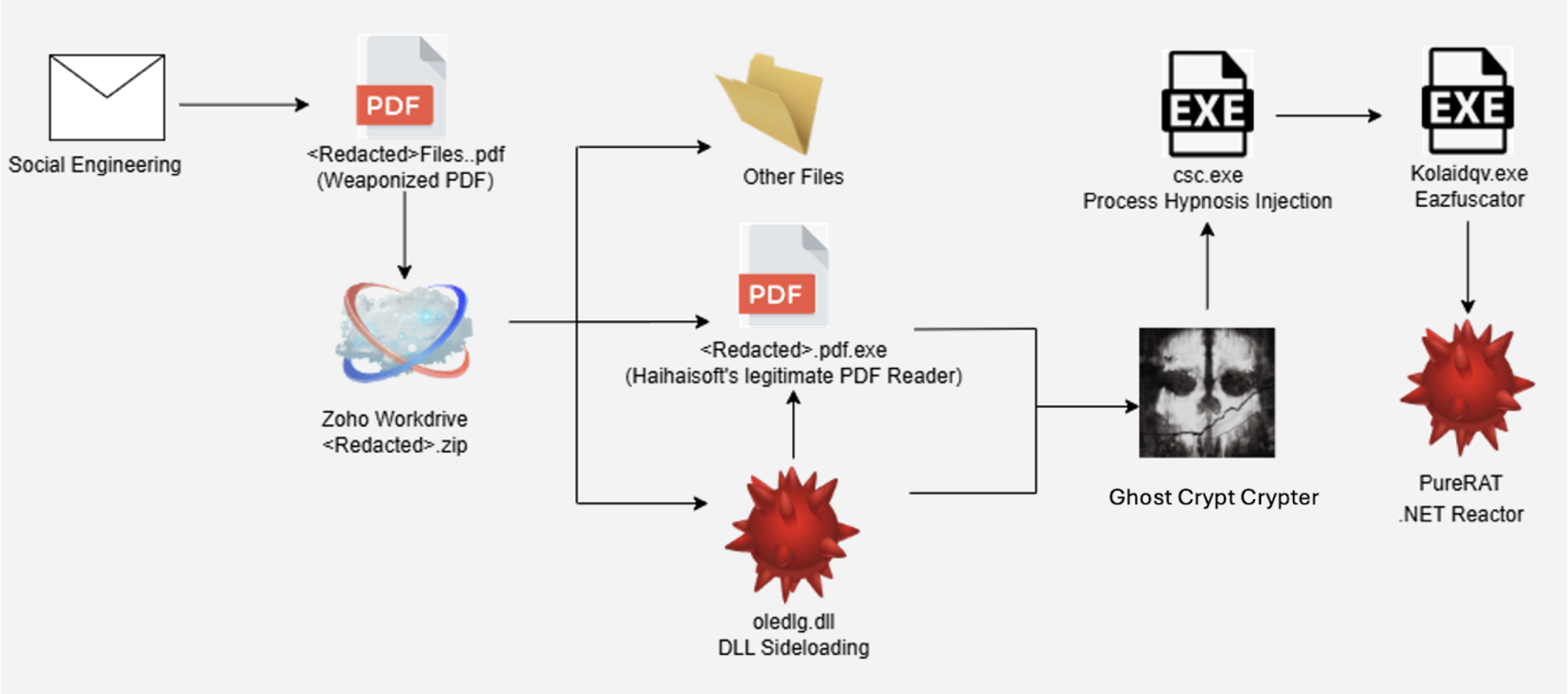
In May 2025, eSentire’s Threat Response Unit detected a sophisticated attack targeting a U.S. accounting firm using the Ghost Crypt crypter to deliver PureRAT malware via a social engineering phishing tactic. The malware employed advanced obfuscation, process injection, and targeted cryptocurrency-related browser extensions and applications to maintain persistence and gather sensitive data. #PureRAT #GhostCrypt #eSentireTRU

Adversaries distributed phishing emails with .zip polyglot attachments containing a PhantomRemote backdoor disguised as legitimate documents. The backdoor collects system information, communicates with a C2 server, and executes commands received via HTTP requests. #PhantomRemote #Phishing #C2Server

The Scanception campaign is an ongoing, sophisticated quishing attack using QR codes embedded in PDFs to bypass traditional security measures and harvest credentials through adversary-in-the-middle phishing pages. The campaign abuses trusted platforms for redirection and targets multiple global sectors, evading detection with advanced techniques. #Scanception #AdversaryInTheMiddle #QRPhishing

The Dark 101 ransomware, identified by FortiGuard Labs, encrypts user files while disabling recovery options and system tools to prevent remediation. It delivers ransom demands in Bitcoin using a dropped text file and evades detection by mimicking legitimate system processes. #Dark101 #FortiGuard #svchost.exe

Geopolitical tensions and infrastructural vulnerabilities are increasing risks to global submarine cable systems, crucial for internet and telecommunications connectivity. State-linked sabotage, particularly involving Russia and China, combined with limited repair capacity, raises the likelihood of prolonged outages in key regions. #SubmarineCables #Russia #China

A sophisticated backdoor named GhostContainer was discovered targeting Exchange servers in government and high-tech organizations in Asia, likely exploiting the CVE-2020-0688 vulnerability. This malware leverages multiple open-source projects, evades detection, and allows attackers full control over compromised Exchange infrastructure. #GhostContainer #CVE2020-0688

Multiple attacks targeting MSPs’ Atera RMM instances were observed, where threat actors deployed Cloudflare tunnels and successfully launched Akira ransomware on customer endpoints. Huntress SOC’s rapid response and log analysis were crucial in detecting and limiting these coordinated ransomware campaigns. #AteraRMM #AkiraRansomware #CloudflareTunnels
The SilverFox actor has conducted a large-scale, ongoing malware delivery campaign since June 2023, primarily targeting Chinese-speaking users with Windows-specific malware through fake applications and spoofed login pages. The actor’s operations have evolved to include anti-automation defenses and increased server distribution, with over 2,800 domains created and 266 active domains as of June 2025. #SilverFox #googeyxvot #yeepays #coinbaw

A critical remote code execution vulnerability (CVE-2025-4660) affects Forescout SecureConnector on Windows, allowing attackers to redirect the agent to malicious servers and control endpoints remotely. The flaw arises from insecure default permissions on a named pipe, permitting unauthorized access. #CVE20254660 #ForescoutSecureConnector #CounterACT
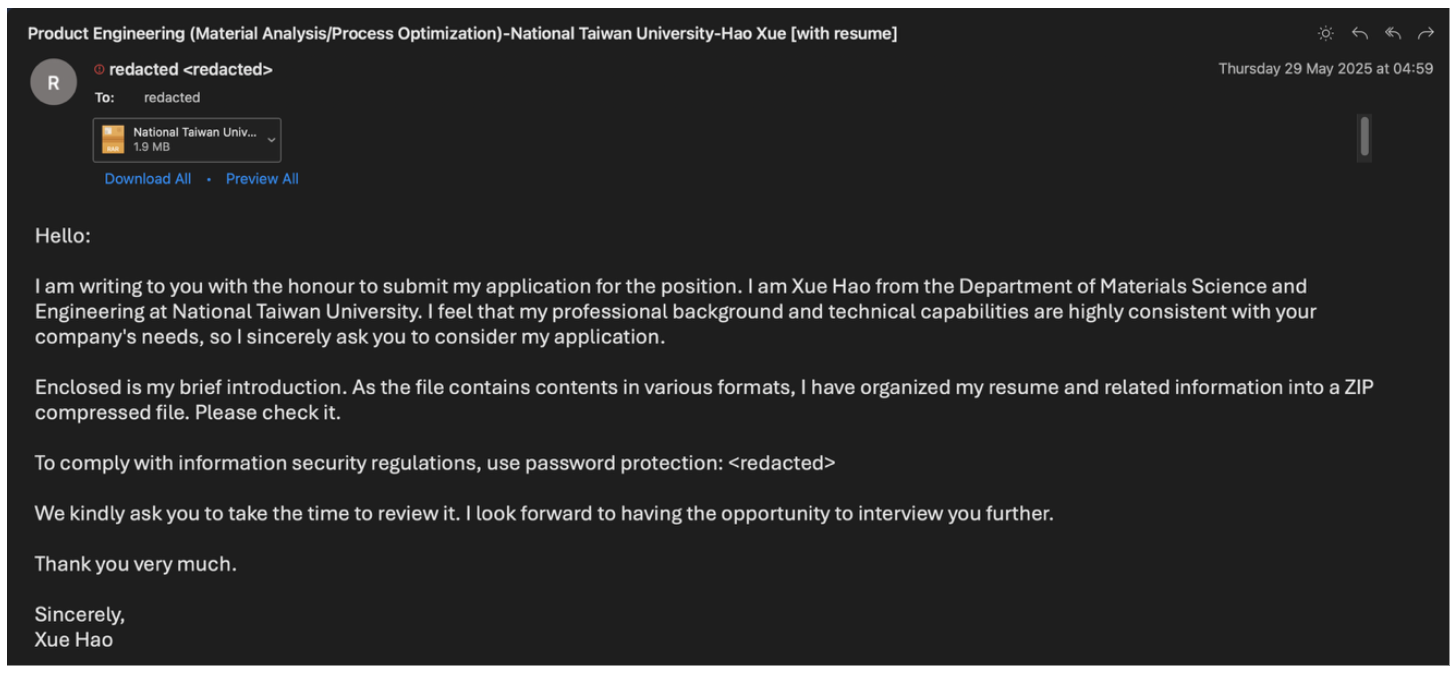
Between March and June 2025, multiple China-aligned threat actors conducted targeted phishing campaigns against Taiwan’s semiconductor industry, focusing on espionage and intelligence gathering. The campaigns employed custom malware like Voldemort and HealthKick, leveraging sophisticated delivery methods including DLL sideloading and adversary-in-the-middle phishing kits. #UNK_FistBump #UNK_DropPitch #Voldemort #HealthKick #TA415 #UNK_SparkyCarp…