Cybercriminals are exploiting the popularity of cryptocurrency by distributing fake Android mining apps through phishing sites impersonating banks like Axis Bank, embedding XMRig to covertly mine Monero on victim devices. This malware operates stealthily by activating mining only when devices are locked, causing high CPU usage, device overheating, and potential hardware damage. #XMRig #AxisBank #Cryptojacking
Keypoints
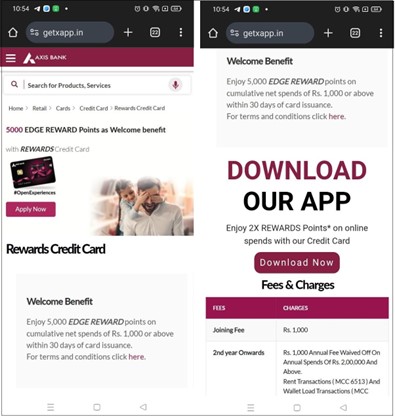
- A phishing website (getxapp[.]in) impersonates Axis Bank and hosts a fake Android app named “Axis Card” that performs hidden cryptocurrency mining using XMRig.
- The malicious app deceives users with a fake update screen but runs a Monero miner covertly in the background, starting mining only when the device is locked and stopping when unlocked.
- The malware downloads an encrypted payload (.so files) from hardcoded URLs including GitHub and decrypts it to execute the XMRig miner.
- The malicious mining app requests permissions such as INTERNET and REQUEST_INSTALL_PACKAGES to facilitate payload download and maintain persistence without explicit user consent.
- Continuous mining results in excessive CPU and memory consumption, significant battery drain, overheating, and potential permanent hardware damage.
- The malware connects to Monero mining pools at pool.uasecurity.org and pool-proxy.uasecurity.org to send mined coins to a specific Monero wallet.
- Affected users are advised to download apps only from trusted sources and use reputable mobile security solutions like Quick Heal Mobile Security for protection.
MITRE Techniques
- [T1204 ] User Execution – The malware relies on users downloading and executing the fake app from phishing sites or social media.
- [T1547 ] Boot or Logon Autostart Execution – The app likely uses the android.intent.action.BOOT_COMPLETED broadcast to maintain persistence after reboot.
- [T1059 ] Command and Scripting Interpreter – The app executes native code (d-miner) to run the XMRig miner using command-line arguments.
- [T1041 ] Exfiltration Over C2 Channel – The malware uploads the mining process’s stdout output (report.txt) to a remote server for analysis.
- [T1119 ] Automated Collection – The malware monitors device states such as battery, lock status every 5 seconds to automate mining execution.
- [T1105 ] Ingress Tool Transfer – The malware downloads encrypted .so payload files from remote hosts including GitHub and Cloudflare Pages.
Indicators of Compromise
- [URL ] Phishing and payload delivery – getxapp[.]in, accessor.pages[.]dev, uasecurity[.]org, github[.]com/backend-url-provider/access/raw/refs/heads/main/
- [Domain ] Mining pool endpoints – pool.uasecurity[.]org, pool-proxy.uasecurity[.]org
- [File Hashes/Names ] Miner payload files – libmine-arm32.so, libmine-arm64.so, and the decrypted executable d-miner
- [Wallet Address ] Monero wallet used for mining profits – 44DhRjPJrQeNDqomajQjBvdD39UiQvoeh67ABYSWMZWEWKCB3Tzhvtw2jB9KC3UARF1gsBuhvEoNEd2qSDz76BYEPYNuPKD