The article investigates a campaign involving the H2Miner crypto-mining botnet and a newly discovered AI-generated ransomware variant called Lcrypt0rx, which targets Linux, Windows, and container environments. This combined threat delivers multiple malicious tools, including miners and stealers, resulting in data encryption, compute hijacking, and system defacement. #H2Miner #Lcrypt0rx #Kinsing #Xmrig #LummaStealer
Category: Threat Research

A recent phishing campaign exploited Booking.com’s official messaging system to send fraudulent messages and steal credit card details using cleverly disguised domains and multi-stage redirects. The investigation uncovered extensive infrastructure, including redirector and phishing content domains, alongside associated malware files and threat actor Telegram accounts. #BookingPhishing #BookingConfirmationID #TelegramOperators

Socket’s Threat Research Team discovered that multiple npm packages contain protestware targeting Russian-language users on Russian or Belarusian domains by disabling UI interactions and playing the Ukrainian national anthem. This protestware originated from the SweetAlert2 package and has unintentionally propagated across numerous other packages without disclosure. #SweetAlert2 #Protestware #SocketThreatResearchTeam
Fancy Bear (APT28) is a Russian cyberespionage group targeting governments, military, and high-value organizations globally, notably influencing elections and exploiting webmail vulnerabilities. Their recent campaigns focus on the Ukraine conflict, espionage against Western logistics, and leveraging malicious documents in Central Asia, using sophisticated malware and phishing techniques. #FancyBear #APT28 #CHERRYSPY #HATVIBE #CVE2023-43770

The article examines a stealthy variant of the Agent Tesla Remote Access Trojan, highlighting its advanced evasion techniques and data-stealing capabilities. It emphasizes the superiority of deep learning-based detection over traditional signature-based tools in identifying this threat early. #AgentTesla #DSXBrain
Research revealed that Microsoft first-party application service principals (SPs), specifically Office 365 Exchange Online’s SP, can be exploited for privilege escalation and persistence in hybrid Entra ID environments by abusing Domain.ReadWrite.All permissions. Attackers with Cloud Application Administrator or Application Administrator roles can add credentials to these SPs, add federated domains, and forge SAML tokens to impersonate any hybrid user, including Global Administrators. #Office365ExchangeOnline #ServicePrincipalHijacking
Researchers uncovered a Chinese mobile forensics application named Massistant used by law enforcement to extract data from confiscated devices, believed to be the successor to MFSocket. Massistant employs advanced techniques like Accessibility Services and connects via Android Debug Bridge over WiFi, posing risks to travelers’ mobile privacy. #Massistant #MFSocket #MeiyaPico
The Konfety Android malware uses advanced evasion techniques such as ZIP-level tampering, dynamic code loading, and stealth features to conduct large-scale ad fraud and distribute malicious payloads. It mimics legitimate apps by sharing package names and hides…
Matanbuchus 3.0 is a sophisticated malware loader used primarily on Windows systems to deliver secondary payloads and enable stealthy, persistent cyberattacks. It features advanced evasion techniques, WQL query support, in-memory execution, and impersonates legitimate applications to communicate with command-and-control servers. #Matanbuchus #Morphisec #EventLogBackupTask

Operation Frostbyte is an open-source cybersecurity training environment created by Varonis Threat Labs to simulate real-world attacks on Snowflake cloud data platforms. It combines an 8-bit video game theme with practical exercises to help security professionals understand and mitigate threats from misconfigurations in Snowflake. #OperationFrostbyte #Varonis #Snowflake…
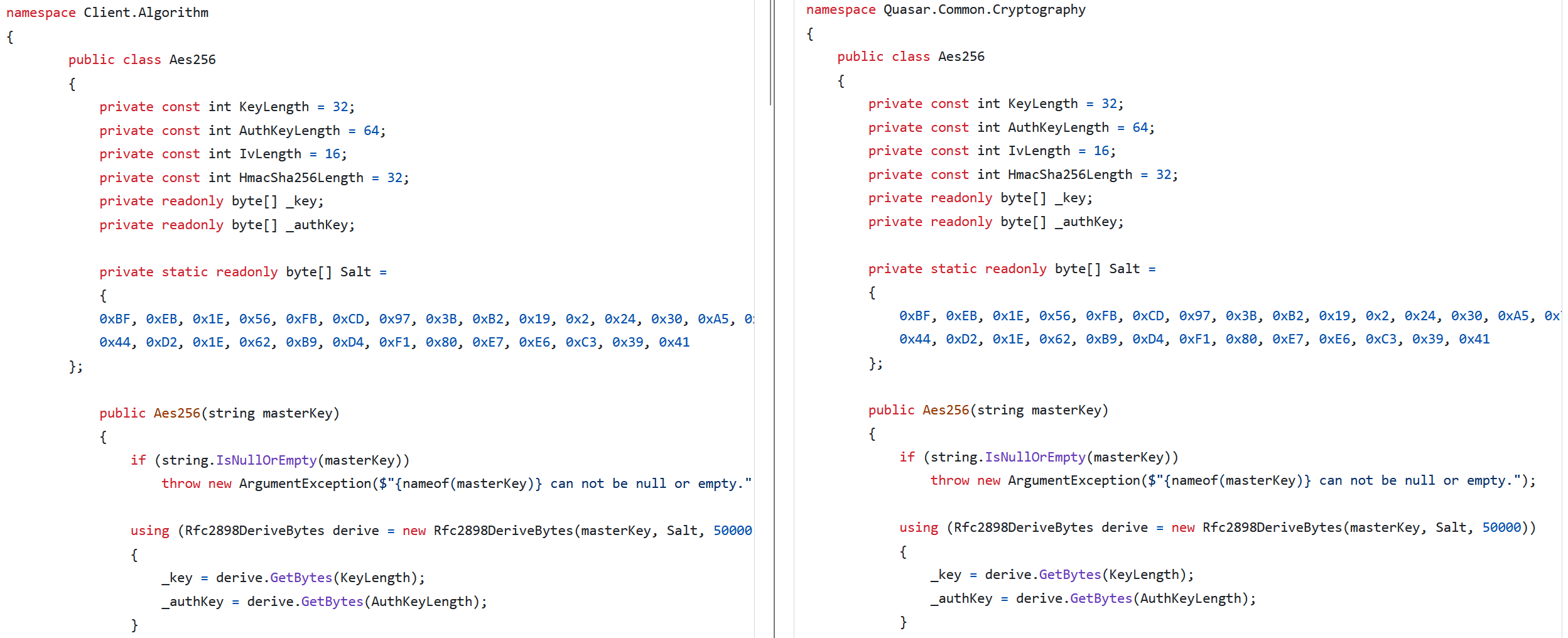
AsyncRAT, an open-source remote access trojan, has evolved through numerous forks, significantly impacting malware landscapes with variants like DcRat and VenomRAT. These forks extend functionality with unique plugins and advanced evasion techniques, highlighting the growing sophistication of open-source malware threats. #AsyncRAT #DcRat #VenomRAT #NonEuclidRAT #JasonRAT
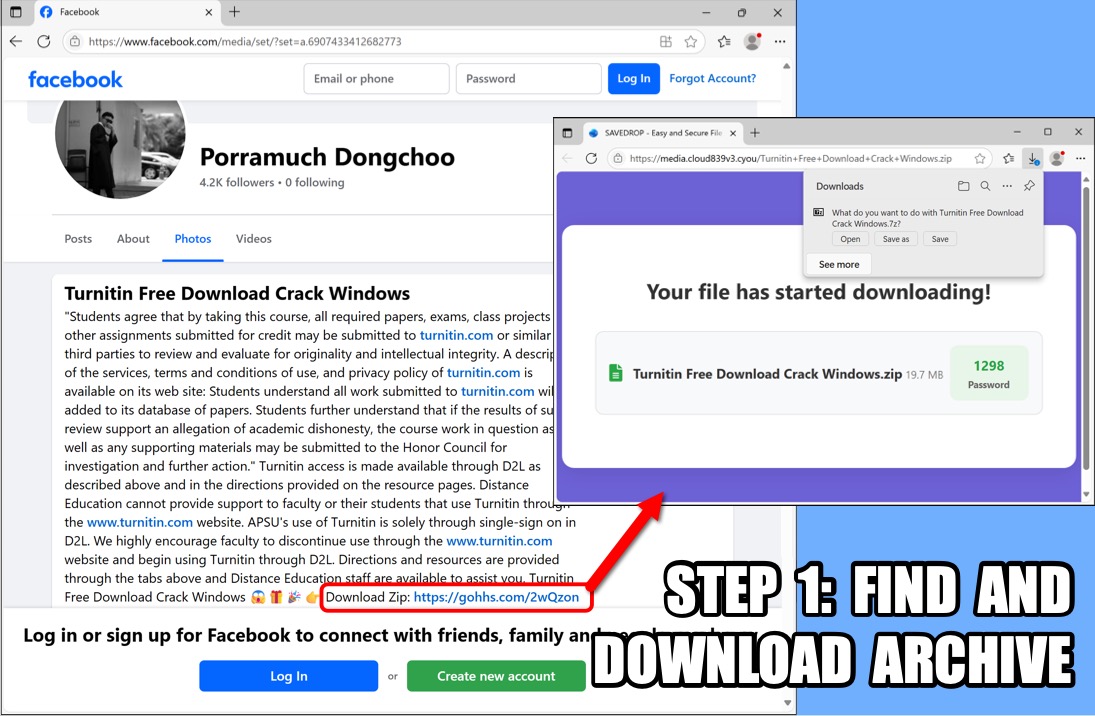
The article details the distribution of Lumma Stealer malware via cracked versions of popular software, followed by the deployment of Rsockstun malware for post-infection activities. It highlights infection methods, associated files, command and control traffic, and persistence mechanisms involving a pen test tool configured as malware. #LummaStealer #Rsockstun #TurnitinCrackMalware

The Cybereason Security Services report analyzes a sophisticated BlackSuit ransomware attack that utilized tools like Cobalt Strike, rclone, and Windows native processes for lateral movement, data exfiltration, and file encryption. The attack uniquely combined data deletion and partial encryption to speed execution and evade detection, posing a significant threat to targeted organizations. #BlackSuit #CobaltStrike #rclone

This report analyzes the distribution trends of Infostealer malware in June 2025, highlighting various disguises such as cracks and keygens, and the use of SEO poisoning for distribution. It also details emerging threats like the modified ACRStealer and novel infection methods involving installer screens and password-protected files. #ACRStealer #LummaC2 #DLLSideLoading #Infostealer…

McAfee’s Mobile Research Team uncovered an active Android malware campaign targeting Bengali-speaking expatriates by impersonating popular financial apps like TapTap Send and AlimaPay to steal personal and financial data. The campaign uses phishing sites and fake Facebook pages for distribution, with a publicly exposed C2 server storing stolen information accessible to…
