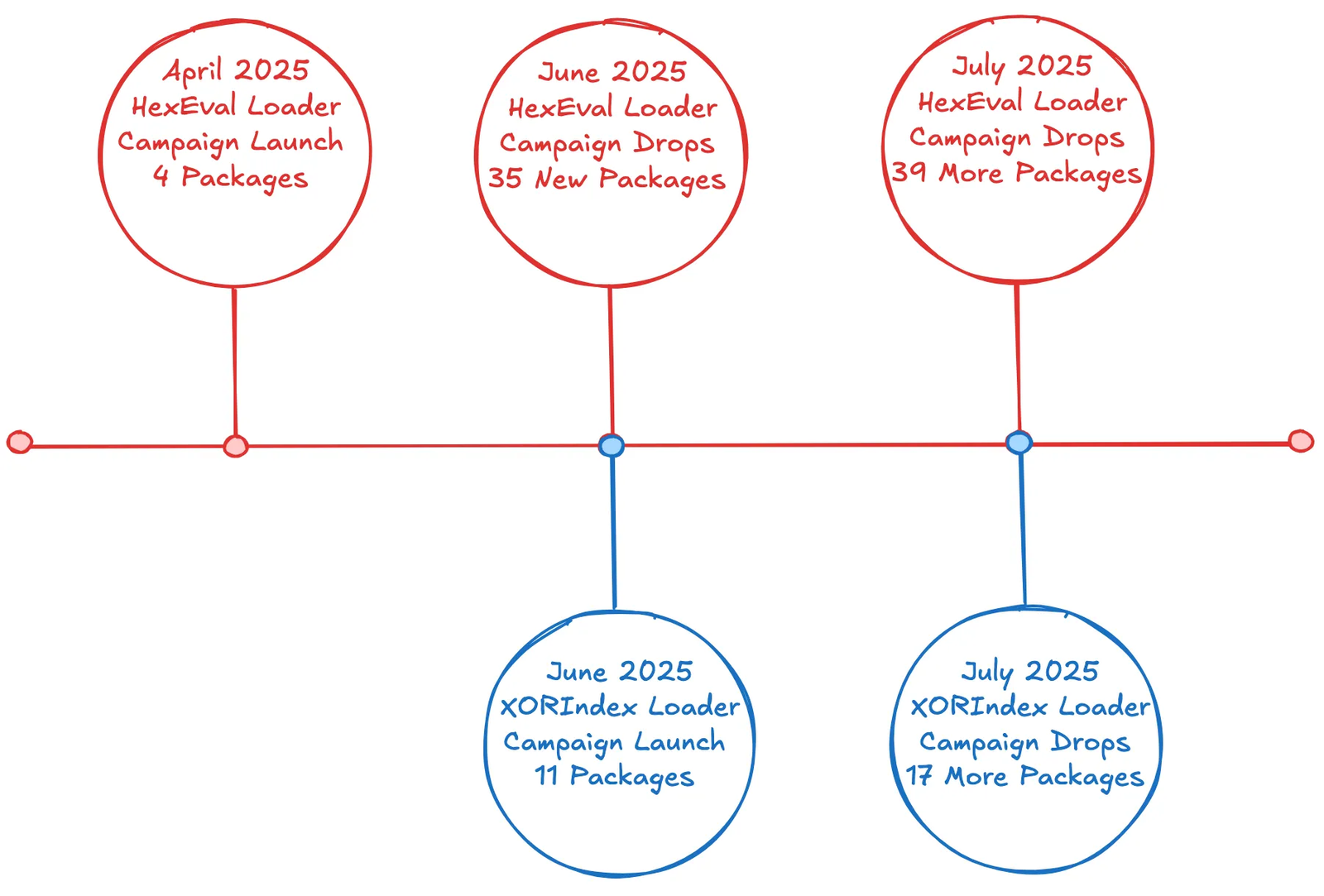
North Korean threat actors involved in the Contagious Interview operation have expanded their software supply chain attacks by deploying a new malware loader named XORIndex in the npm ecosystem, alongside the ongoing HexEval Loader campaign. These loaders deliver multi-stage malware including BeaverTail and InvisibleFerret backdoors, targeting developers and cryptocurrency holders with sophisticated obfuscation and data exfiltration techniques. #XORIndex #HexEvalLoader #ContagiousInterview #BeaverTail #InvisibleFerret
Category: Threat Research
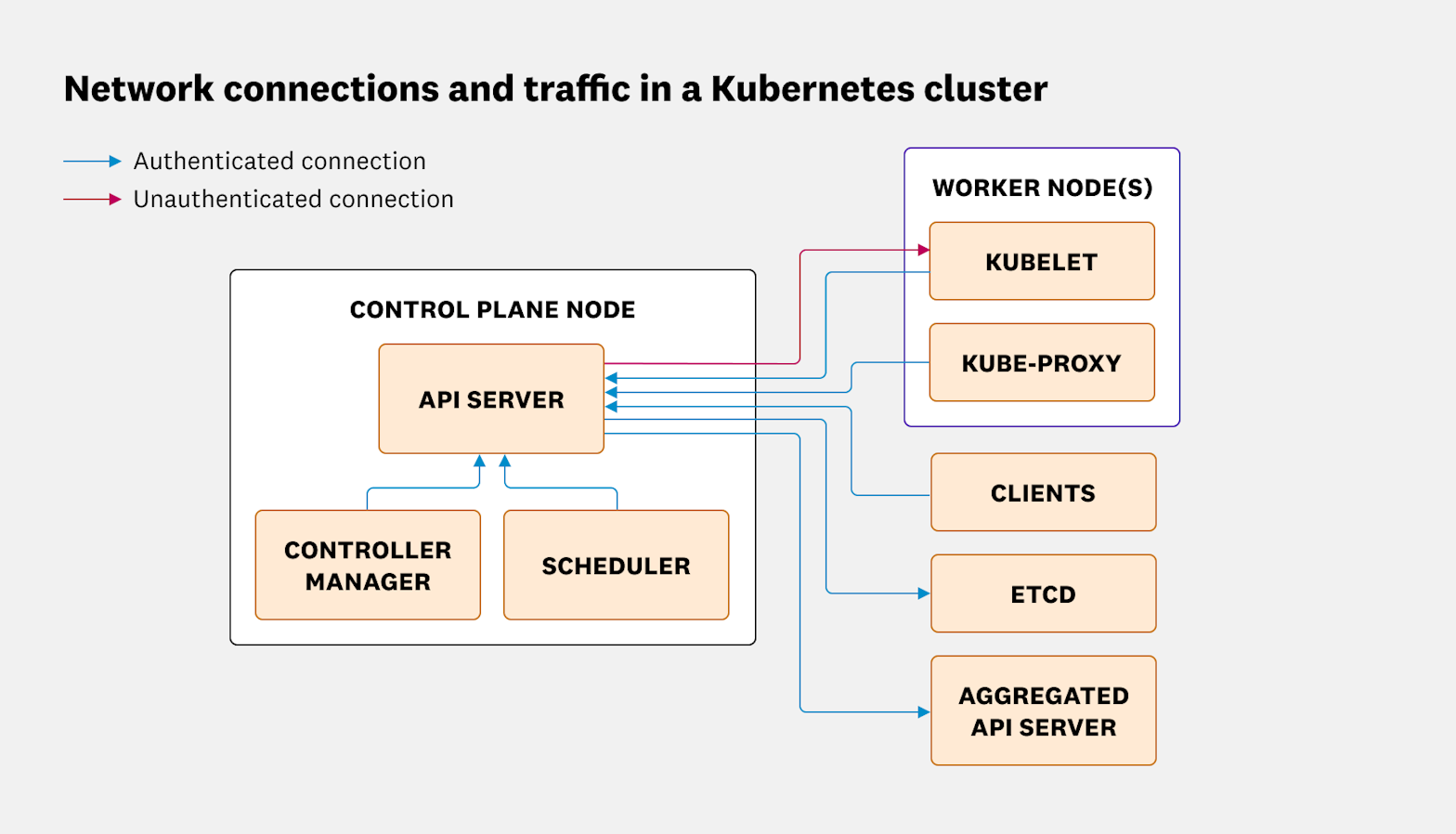
Kubernetes uses Public Key Infrastructure (PKI) to authenticate and encrypt communications between system components, involving multiple certificate authorities (CAs) for enhanced security. Protecting private key files and minimizing client certificate use are critical, as Kubernetes currently lacks certificate revocation mechanisms. #KubernetesPKI #kubeadm #etcd #CertificateAuthority

In June 2025, there was an increase in new ransomware samples compared to May, with data collected from AhnLab detections and ransomware group leak sites. The report includes statistics on ransomware samples, affected systems, and companies impacted by various ransomware groups globally, including Korea. #AhnLab #ATIP #DedicatedLeakSites…

Cyble’s latest report reveals a significant increase in exploit attempts, malware campaigns, and brute-force attacks targeting IoT devices and enterprise systems worldwide. Critical vulnerabilities across various devices and software remain actively exploited, highlighting the need for rigorous patching and comprehensive security measures. #Mirai #CoinMiner #WannaCry #CVE-2025-45985 #CVE-2025-30220

AI is enhancing both malware development and antivirus analysis, particularly improving de-obfuscation capabilities but still struggling with complex packing and newer frameworks like Flutter and Rust. Fortinet’s protections already cover the malware families mentioned, ensuring customer safety against these evolving threats. #LinuxLadvixE #LinuxPrometeiB #SpyLoan #FilecoderBRtr

Researchers have identified a new variant of the Interlock ransomware group’s remote access trojan (RAT) that uses PHP instead of JavaScript, expanding its delivery methods in widespread cyber campaigns. This PHP-based Interlock RAT leverages compromised websites with injected scripts and a resilient command and control infrastructure using trycloudflare.com URLs and fallback IPs. #InterlockRAT #KongTuke #FileFix
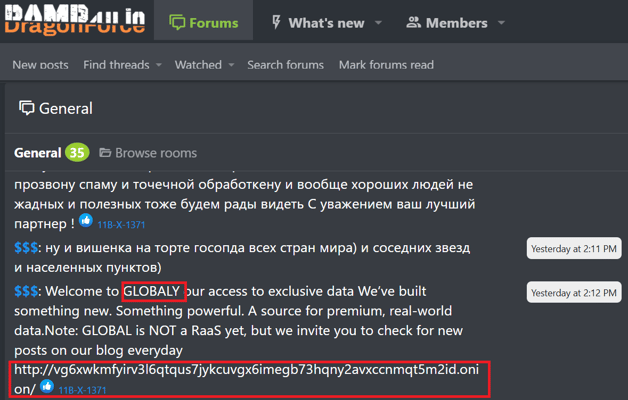
GLOBAL GROUP is a newly observed ransomware-as-a-service (RaaS) operation, likely a rebranding of the Black Lock RaaS, targeting multiple sectors across the US, Europe, Australia, and Brazil with advanced malware and AI-powered ransom negotiations. The group relies heavily on Initial Access Brokers to gain network entry and deploy ransomware rapidly, emphasizing high-value targets and seven-figure ransom demands. #GLOBALGROUP #BlackLock #Mamona #Ramp4u #InitialAccessBroker
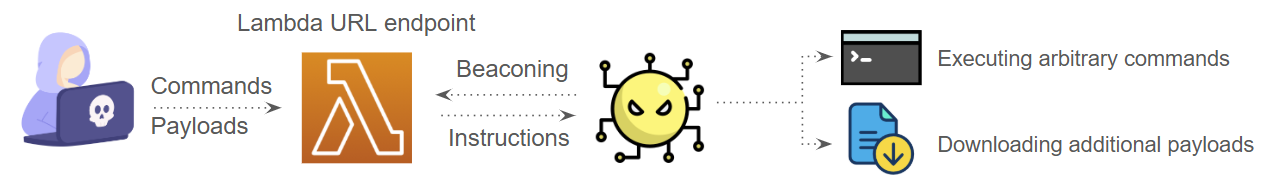
Since late 2024, the CL-STA-1020 threat group has targeted Southeast Asian government entities using a novel Windows backdoor named HazyBeacon that communicates via AWS Lambda URLs for command and control. The campaign highlights advanced techniques such as DLL sideloading and data exfiltration through legitimate cloud services like Google Drive and Dropbox….

Varonis Threat Labs discovered a phishing campaign exploiting Microsoft 365’s Direct Send feature to send spoofed internal emails without authentication. The attack has targeted over 70 mainly US-based organizations, using spoofed voicemail notifications with malicious PDF attachments to harvest credentials. #DirectSend #Microsoft365 #VaronisThreatLabs

The RedDirection campaign revealed a network of 18 malicious browser extensions across Chrome and Edge that infected over 2.3 million users by hijacking browsers while providing legitimate functionality. These extensions exploited trust signals such as verified badges and featured placements to silently deploy malware through updates and enable persistent surveillance and redirection attacks. #RedDirection #ColorPicker #BrowserHijacking

Huntress detected active exploitation of CVE-2025-47812, a null byte and Lua injection vulnerability in Wing FTP Server, on July 1, 2025. The exploit allows remote code execution at root/SYSTEM level, and attackers attempted various post-exploitation activities before being stopped by Microsoft Defender. #CVE202547812 #WingFTPServer #TrojanWin32CeproladA
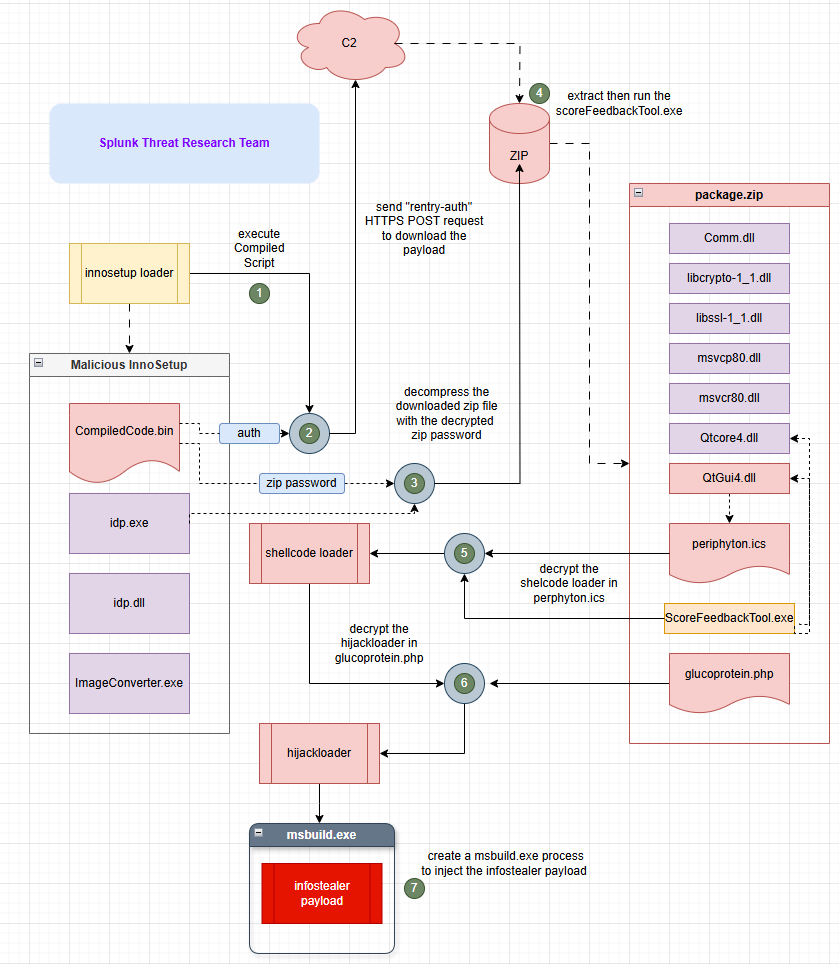
Cybercriminals are increasingly abusing legitimate Inno Setup installers by embedding malicious payloads using Pascal scripting to evade detection and deliver information-stealing malware such as RedLine Stealer. This campaign employs sophisticated evasion techniques including debugger checks, sandbox avoidance, DLL sideloading, and command obfuscation to persist on infected systems and steal sensitive data. #InnoSetup #HijackLoader #RedLineStealer
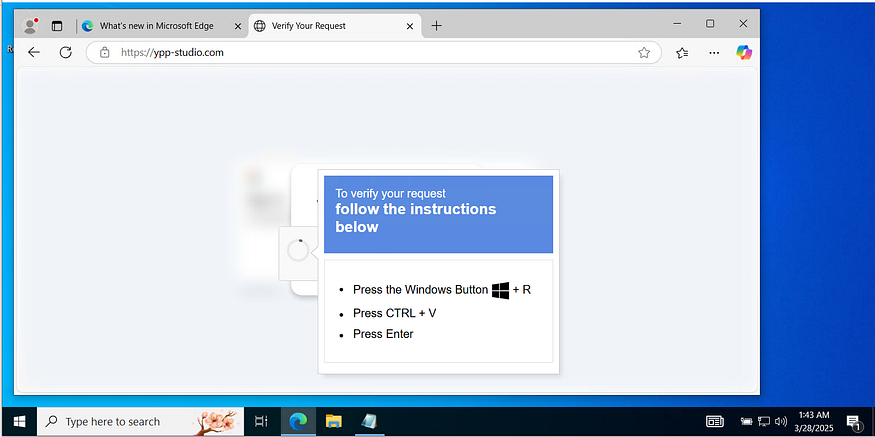
Rhadamanthys Stealer is a modular information-stealing malware distributed via phishing domains like hxxps://ypp-studio[.]com, employing fileless PowerShell execution to download and execute malicious payloads. The malware uses multiple anti-analysis and evasion techniques, targets a wide range of sensitive data, and communicates with hardcoded C2 servers using raw IP sockets. #Rhadamanthys #PowerShell #PTRFHDGS
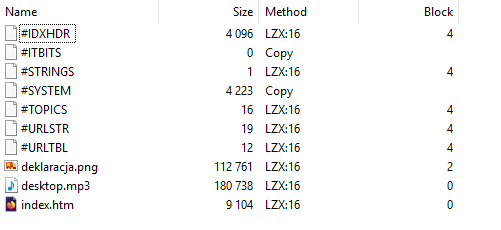
A malicious CHM file named deklaracja.chm was uploaded from Poland, initiating an infection chain that deploys a C++ downloader through obfuscated JavaScript and a CAB file payload. The downloader fetches an encrypted payload from rustyquill[.]top, associated with the FrostyNeighbor and UNC1151 threat actors, targeting Eastern European countries. #deklaracja_chm #FrostyNeighbor #UNC1151 #rustyquill_top

The Octalyn Forensic Toolkit is a C++ and Delphi-based credential stealer disguised as a forensic research tool, capable of extracting browser data, cryptocurrency wallets, and social media tokens, with data exfiltration conducted via Telegram. Its modular design, persistence mechanisms, and obfuscated payloads make it a significant threat when misused by malicious actors. #OctalynForensicToolkit #TelegramBuild.exe #CredentialStealer