North Korean threat actors involved in the Contagious Interview operation have expanded their software supply chain attacks by deploying a new malware loader named XORIndex in the npm ecosystem, alongside the ongoing HexEval Loader campaign. These loaders deliver multi-stage malware including BeaverTail and InvisibleFerret backdoors, targeting developers and cryptocurrency holders with sophisticated obfuscation and data exfiltration techniques. #XORIndex #HexEvalLoader #ContagiousInterview #BeaverTail #InvisibleFerret
Keypoints
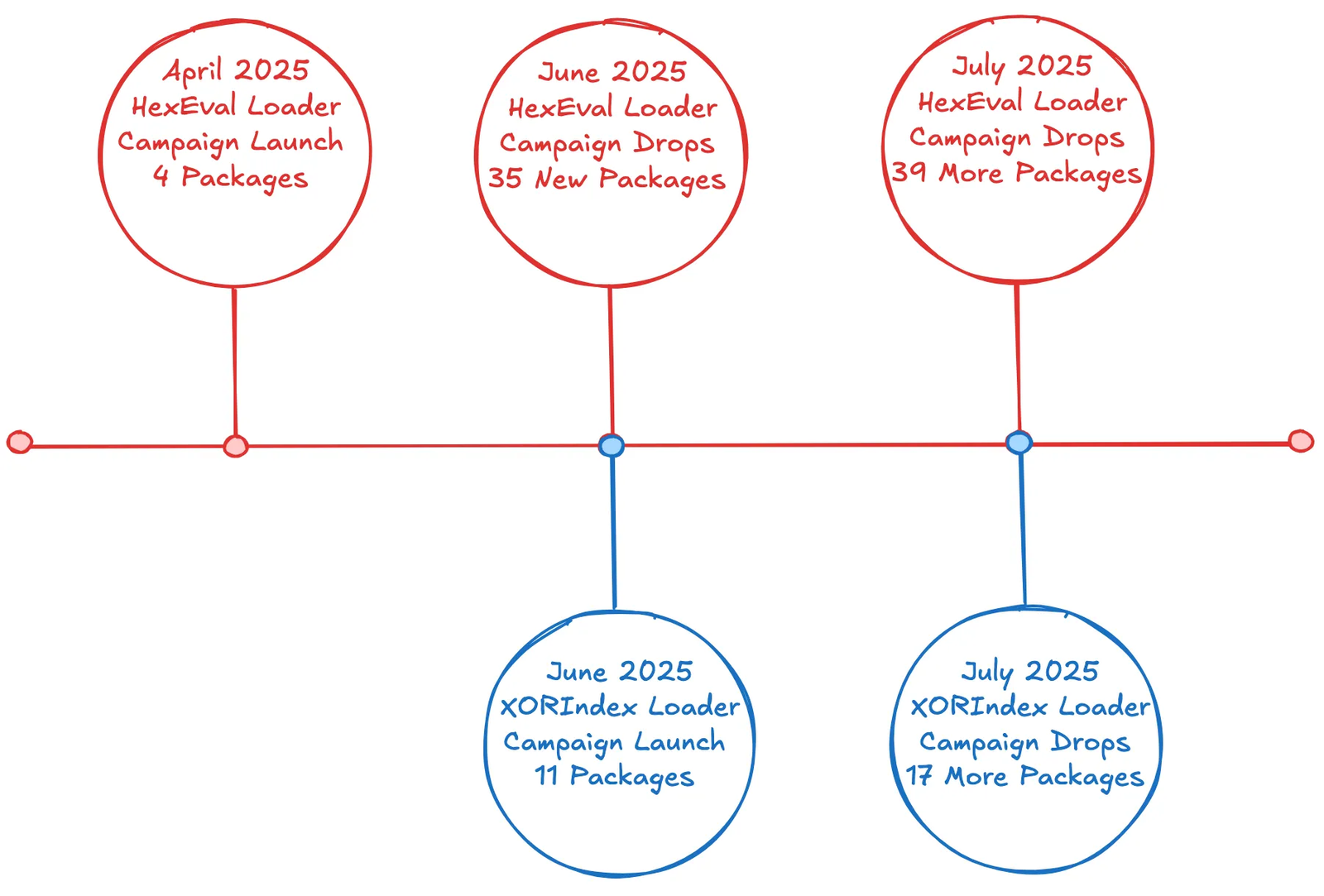
- The Socket Threat Research Team identified 67 malicious npm packages linked to North Korean threat actors deploying the XORIndex Loader, downloaded more than 17,000 times, with 27 packages still live on the npm registry.
- The XORIndex Loader uses XOR-based string obfuscation, collects extensive host telemetry, and executes arbitrary JavaScript payloads to deliver second-stage BeaverTail malware.
- BeaverTail targets nearly 50 wallet and browser extension paths to steal cryptocurrency-related data, archives it, and exfiltrates it to a hardcoded HTTP endpoint, then fetches and executes the InvisibleFerret backdoor.
- The XORIndex Loader evolved through three prototype stages (postcss-preloader, js-log-print, dev-filterjs) before the current fully featured loader with multi-endpoint C2 rotation and host profiling.
- North Korean threat actors operate both the XORIndex and HexEval Loader campaigns in parallel, continuously rotating npm maintainer aliases and adapting evasion techniques.
- Command and Control (C2) infrastructure is hosted mainly on Vercel under the /api/ipcheck path, facilitating remote code execution and modular malware delivery.
- Security recommendations emphasize proactive supply chain defense, use of real-time scanning tools like Socket GitHub App and CLI, and heightened vigilance for developers and DevOps professionals.
MITRE Techniques
- [T1195.002] Supply Chain Compromise – Compromise of the npm software supply chain through malicious package uploads. (“…infiltrated the npm ecosystem with 67 malicious packages…”)
- [T1608.001] Stage Capabilities: Upload Malware – Deployment of multiple malicious npm packages containing loader malware.
- [T1204.002] User Execution: Malicious File – Execution of malicious JavaScript code via npm package installation post-install scripts.
- [T1059.007] Command and Scripting Interpreter: JavaScript – Use of eval() to execute threat actor-supplied JavaScript payloads after loading packages.
- [T1027.013] Obfuscated Files or Information: Encrypted/Encoded File – XOR-based string obfuscation and ASCII buffer encoding used in loader variants (‘…first use of string-level obfuscation (ASCII buffer decoded via TextDecoder)…’).
- [T1546.016] Event Triggered Execution: Installer Packages – Post-install hooks in npm packages to execute payloads.
- [T1005] Data from Local System – Collection of host telemetry including hostname, username, OS, IP, geolocation information.
- [T1082] System Information Discovery – Gathering system hostname, username, OS platform, and network details.
- [T1083] File and Directory Discovery – BeaverTail scanning for wallet directories and browser extension storage.
- [T1217] Browser Information Discovery – Enumeration of Chromium and Gecko browser profiles and extensions.
- [T1555.003] Credentials from Password Stores: Credentials from Web Browsers – Theft of browser extension storage and wallet credentials.
- [T1555.001] Credentials from Password Stores: Keychain – Collection of macOS keychain files.
- [T1041] Exfiltration Over C2 Channel – Data exfiltration of harvested files and telemetry via HTTP POST to hardcoded C2 endpoints.
- [T1105] Ingress Tool Transfer – Download of additional malware payloads such as InvisibleFerret via HTTP GET.
- [T1119] Automated Collection – Automated scanning and data archiving of wallet and browser files with adm-zip module.
- [T1657] Financial Theft – Targeting cryptocurrency wallets and keys for monetary gain.
Indicators of Compromise
- [Malicious npm Packages with XORIndex Loader] Malicious packages uploaded to npm, some still live: vite-meta-plugin, vite-postcss-tools, pretty-chalk, vite-usageit, ecom-config, and 22 more.
- [Malicious npm Packages with HexEval Loader] Additional malicious packages: nextjs-https-supertest, nextjs-package-purify, jsonslicer, node-mongo-orm, parsing-query, and others still live on npm.
- [npm Aliases] Accounts used for publishing: h96452582, devin-ta39, csilvagalaxy, alisson_dev, dmytryid, drgru, ahmadbahai, stefanofrick2, samuelhuggins, jgod19960520, monster1117, marilin, jasonharry1988, davidmoberly, vitalii0021, rory210 and others.
- [Email Addresses] Associated email addresses tying to npm accounts include h96452582@gmail[.]com, devin.s@gedu[.]demo[.]ta-39[.]com, csilvagalaxy87@gmail[.]com, souzaporto800@gmail[.]com, dmytroputko@gmail[.]com, drgru854@gmail[.]com, ahmadbahai07@gmail[.]com, stefanofrick2@gmail[.]com, samuelhuggins3@gmail[.]com, and multiple others.
- [Command and Control (C2) Endpoints] Infrastructure URLs used for data exfiltration and command execution: https://soc-log[.]vercel[.]app/api/ipcheck, https://1215[.]vercel[.]app/api/ipcheck, https://log-writter[.]vercel[.]app/api/ipcheck, https://process-log-update[.]vercel[.]app/api/ipcheck, https://api[.]npoint[.]io/1f901a22daea7694face, and http://144[.]217[.]86[.]88 (used for BeaverTail exfiltration and payload download).
Read more: https://socket.dev/blog/contagious-interview-campaign-escalates-67-malicious-npm-packages