A malicious CHM file named deklaracja.chm was uploaded from Poland, initiating an infection chain that deploys a C++ downloader through obfuscated JavaScript and a CAB file payload. The downloader fetches an encrypted payload from rustyquill[.]top, associated with the FrostyNeighbor and UNC1151 threat actors, targeting Eastern European countries. #deklaracja_chm #FrostyNeighbor #UNC1151 #rustyquill_top
Keypoints
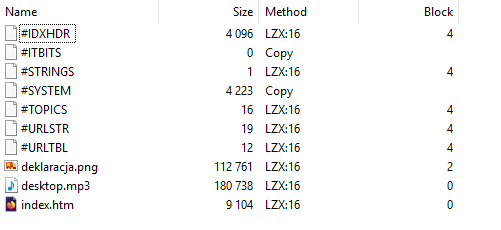
- The deklaracja.chm file is a Microsoft Compiled HTML Help file containing obfuscated JavaScript and malicious payloads hidden within standard CHM components.
- Execution of deklaracja.chm leads to the extraction and running of a downloader DLL named uNT32.dll, delivered via a CAB file disguised as an MP3.
- Obfuscated JavaScript in index.htm creates iframes, loads decoy images, and uses an ActiveX control to execute commands through native Windows processes like forfiles.exe and rundll32.exe.
- uNT32.dll downloader decrypts strings with XOR and uses WinHTTP APIs to download a payload from the domain rustyquill[.]top, referencing the Magnus Protocol podcast.
- The downloaded payload is validated for size before XOR decryption and saved as a DLL executed with an exported function; a scheduled task ensures persistence.
- rustyquill[.]top domain is linked to previous malicious CHM files attributed to FrostyNeighbor and UNC1151, threat actors with historical targeting in Poland and nearby countries.
- Multiple hashes for the components, including deklaracja.chm, index.htm, desktop.mp3, deklaracja.png, and associated ZIP files, have been identified to track the infrastructure and related files.
MITRE Techniques
- [T1127] Trusted Developer Utilities Proxy Execution – Use of forfiles.exe, a legitimate Windows utility, as a LOLbin to execute commands and evade detection (‘The use of this LOLbin is common in the indirect execution of commands’)
- [T1218] Signed Binary Proxy Execution – Execution of rundll32.exe to load and execute the malicious DLL payload (‘the DLL (uNT32.dll) is loaded via rundll32.exe, invoking an exported function with ordinal #1’)
- [T1059] Command and Scripting Interpreter – Use of obfuscated JavaScript within the CHM file to execute commands indirectly through ActiveX control and script functions (‘Obfuscated JS script in index.htm that starts the infection chain’)
- [T1543] Create or Modify System Process – Creation of a Scheduled Task to execute the downloaded DLL and maintain persistence (‘A Scheduled Task is created for the DLL execution using the TaskScheduler API’)
- [T1105] Ingress Tool Transfer – Downloader DLL uses WinHTTP APIs to fetch the payload from a remote server (‘The downloader uses the WinHTTP APIs to download and read payload delivered from the threat actor infrastructure’)
Indicators of Compromise
- [File Hash] deklaracja.chm – 0d3dbaa764acb2b87ae075aa2f5f924378991b39587b0c5e67a93b10db39ddd9
- [File Hash] index.htm – 156ad4975e834355b2140d3c8fe62798fe6883364b8af1a1713f8b76c7b33947
- [File Hash] desktop.mp3 – be5a40b5622d21b46cbc87fd6c3f8ebcb536ec8480491a651c1625ee03ae2c6fd
- [File Hash] deklaracja.png – f55e06a87e2a20989ddb76d9f2e3ebb303659ad306ba54e3ed7f8dcc4456d71b
- [Domain] rustyquill.top – domain hosting the malicious payload and linked to previous FrostyNeighbor infrastructure
- [File Hash] dowód_wpłaty.zip – 4d09fad2630ec33ab6bb45b85455c6a6ac7b52f8dae9b90736db4a5f00f72ea9
- [File Hash] dowod.chm – 0631696f484633f4aeb8f817af2a668806ab4dca70f006dc56fc9cd9dcda4dbe
Read more: https://dmpdump.github.io/posts/Belarus-nexus_Threat_Actor_Target_Poland/