Rhadamanthys Stealer is a modular information-stealing malware distributed via phishing domains like hxxps://ypp-studio[.]com, employing fileless PowerShell execution to download and execute malicious payloads. The malware uses multiple anti-analysis and evasion techniques, targets a wide range of sensitive data, and communicates with hardcoded C2 servers using raw IP sockets. #Rhadamanthys #PowerShell #PTRFHDGS
Keypoints
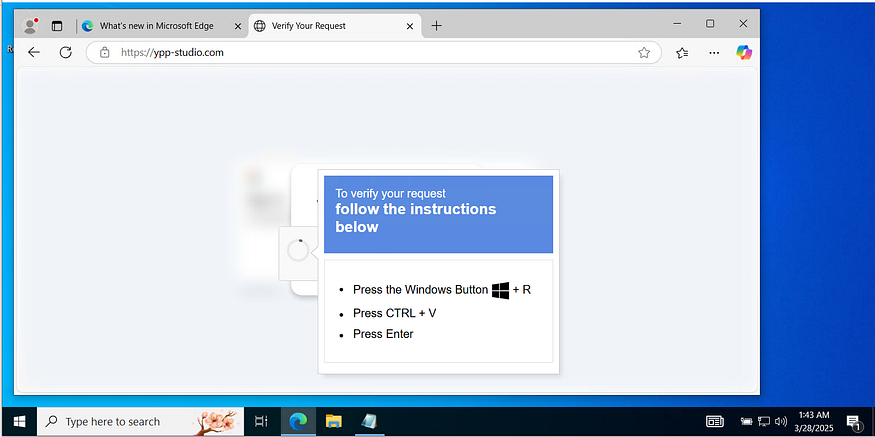
- Rhadamanthys Stealer is delivered through phishing domains such as hxxps://ypp-studio[.]com and uses fileless PowerShell commands to download payloads like PTRFHDGS.msi.
- The malware is highly modular, evolving since 2022, and sold as Malware-as-a-Service with advanced evasion and multilayer architecture.
- It uses multiple sophisticated anti-analysis techniques including anti-VM, anti-debugging, time-based side-channel detection, and a process blacklist to evade detection tools.
- The malware harvests extensive user and system data, including credentials, browser data, cryptocurrency wallets, FTP and email clients, 2FA tools, messaging apps, and gaming platforms.
- Rhadamanthys communicates directly with a hardcoded C2 IP (193.109.85.136) using TCP sockets to avoid DNS-based detection.
- The campaign uses social engineering tactics such as fake verification messages and disguising payloads behind CAPTCHA mechanisms for stealthy delivery.
- A Sigma detection rule has been developed to flag suspicious PowerShell execution and related behaviors linked to Rhadamanthys activity.
MITRE Techniques
- [T1059.001] PowerShell – Used to execute fileless attacks by downloading and running scripts in memory (“iex ((New-Object Net.WebClient).DownloadString($u))”).
- [T1562.001] Impair Defenses: Disable or Modify Tools – Employs multiple anti-debugging methods checking for breakpoint instructions (“checks for breakpoint instructions (INT 3 = 0xCC)”).
- [T1562.004] Impair Defenses: Impair Virtualization/Sandbox Evasion – Uses anti-VM checks gathering system information to detect virtual environments.
- [T1134.001] Access Token Manipulation: Token Impersonation/Theft – Uses process blacklist to detect and evade analysis/debugging tools (“compares active processes to a predefined list”).
- [T1113] Screen Capture – Captures screenshots and possibly sends them to C2 servers (“captures a dynamic screenshot of specified window region”).
- [T1071.001] Application Layer Protocol: Web Protocols – Uses raw TCP sockets and direct IP communication for C2 communications (“hardcoded C2 server IP address 193.109.85.136”).
- [T1574.001] Hijack Execution Flow: DLL Search Order Hijacking – Disguises payload as MSI installers to masquerade malware (“disguises itself as legitimate software such as MSI installers”).
Indicators of Compromise
- [Domain] Phishing delivery domain – hxxps://ypp-studio[.]com
- [URL] Malware payload download – http://62.60.226.74/PTRFHDGS.msi
- [File] Executable file triggered by download – rh_0.9.0.exe
- [IP Address] Command-and-Control server – 193.109.85.136
- [IP Address] Previous malware delivery server – 77.239.96.51