AkiraBot is a spamming framework that targets website chats and contact forms to promote low-quality SEO services, spamming over 80,000 websites since September 2024 using AI-generated custom messages and CAPTCHA bypass techniques. Researchers identified numerous related IoCs including 34 domains, 16 email-connected domains, and 22 IP addresses, some of which are malicious. #AkiraBot #SEOspamming #Namecheap #DNSChronicle
Keypoints
- AkiraBot has targeted over 400,000 websites and actively spammed 80,000+ sites since September 2024.
- The bot uses OpenAI to generate tailored outreach messages matching the purpose of targeted websites.
- It employs multiple CAPTCHA bypass mechanisms and network detection evasion techniques to avoid detection.
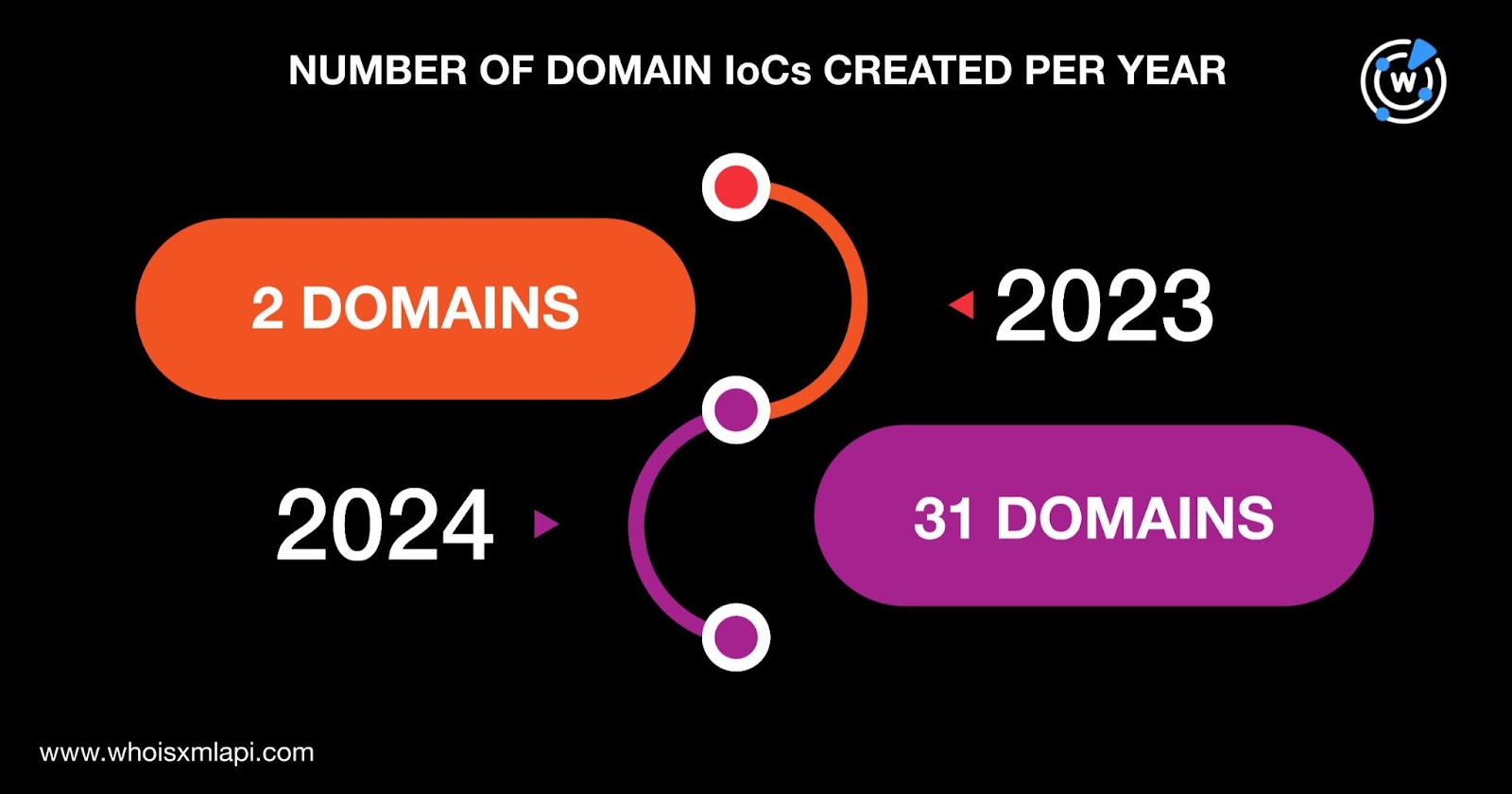
- Researchers identified 34 domains as indicators of compromise (IoCs) related to AkiraBot activities.
- Further investigation revealed 16 email-connected domains and 22 IP addresses linked to these IoCs, with 10 IPs confirmed malicious.
- Most domains were registered between 2023 and 2024, predominantly via the Namecheap registrar and largely based in Iceland.
- Historical data analysis showed domain-to-IP resolutions dating back to as early as 2017.
MITRE Techniques
- [T1204] User Execution – AkiraBot generates custom messages with OpenAI encouraging user interaction and engagement (“…uses OpenAI to generate custom outreach messages matching the target sites’ purpose…”).
- [T1566.001] Phishing: Spearphishing Link – The bot spams website chats and contact forms with tailored messages designed to promote malicious SEO services, potentially tricking users into interacting with harmful content (“…framework made to spam website chats and contact forms to promote a low-quality SEO service…”).
- [T1598] Phishing for Information – Use of multiple CAPTCHA bypass mechanisms to evade security controls and maintain persistent interaction on target sites (“…employs multiple CAPTCHA bypass mechanisms and network detection evasion techniques.”).
Indicators of Compromise
- [Domains] 34 AkiraBot-related domains including akirateam[.]com, goservicewrap[.]com, and searchengineboosters[.]com, mostly registered via Namecheap.
- [IP Addresses] 22 IP addresses linked to these domains, such as 198[.]57[.]247[.]157; 10 of which have been confirmed malicious.
- [Email Addresses] 32 email addresses found in historical WHOIS records for 20 domains, including three public emails connected to 16 email-linked domains.
Read more: https://circleid.com/posts/framing-the-akirabot-framework-under-the-dns-lens