A new phishing campaign targeting SPID users was detected, involving fraudulent emails that impersonate official communications to steal login credentials. CERT-AGID issued preventive measures and shared related Indicators of Compromise to mitigate the threat. #SPIDPhishing #CERTAGID #SPID
Keypoints
- A phishing campaign targeting SPID users uses fraudulent emails with the subject “Your digital certificate has just been renewed.”
- The emails impersonate the official address [email protected] but are sent from third-party servers without DKIM signatures.
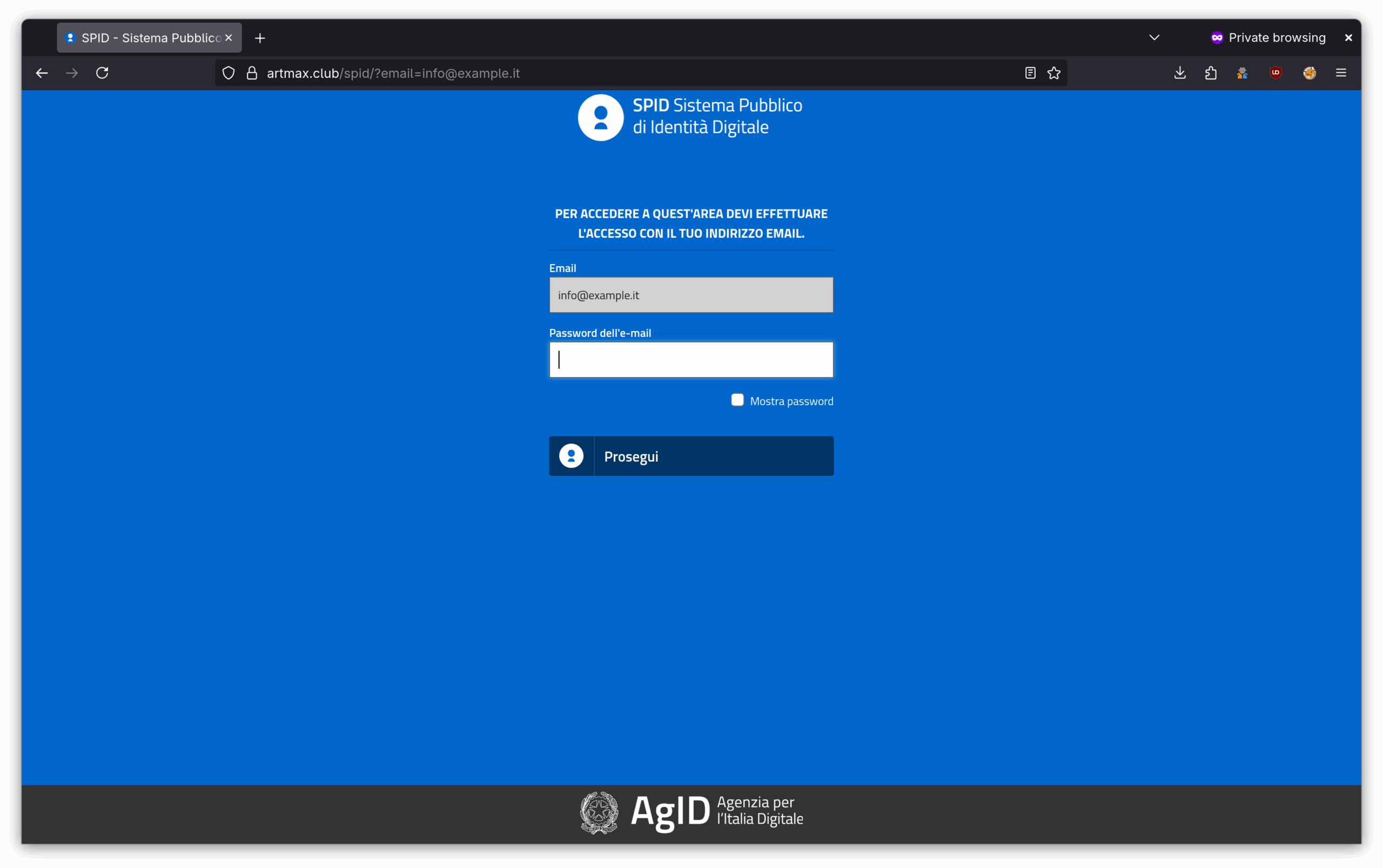
- The phishing email directs victims to a fake SPID login page to steal credentials.
- Emails are delivered to business mailboxes such as [email protected] and bypass SPF checks if not properly configured.
- AgID requested the takedown of the phishing domain and hosting service to prevent further data theft.
- CERT-AGID distributed Indicators of Compromise (IoCs) to accredited entities via its feed.
- Users and administrators are advised to implement SPF, DMARC, and DKIM to prevent email spoofing and report suspicious emails to [email protected].
MITRE Techniques
- [T1566] Phishing – The campaign used fraudulent emails impersonating the address [email protected] to lure victims into entering credentials on fake login pages. (“…inviting to download a supposed new digital certificate necessary for access to SPID services…”)
- [T1537] Transfer Data to Cloud Account – Attackers hosted phishing pages on a third-party domain that was later requested to be disabled. (“…requested the deactivation of the domain hosting the phishing pages and the hosting service.”)
- [T1598] Phishing: Spearphishing Link – Emails contained links redirecting victims to fake SPID login portals. (“…link in the email body leads to a fake SPID login page where login credentials are requested.”)
- [T1071] Application Layer Protocol – Use of email communication to deliver phishing messages that bypass SPF authentication if improperly configured. (“…emails can only be delivered if the destination server does not correctly implement SPF authentication.”)
Indicators of Compromise
- [Email Address] Fraudulent sender address used in phishing emails – [email protected] impersonated but emails sent from unauthorized third-party servers.
- [Domain] Phishing domain hosting fake SPID login pages – domain hosting was requested for deactivation (specific domain details provided in CERT-AGID feed).
- [URL] Links to fraudulent SPID login pages – included in email bodies directing users to credential theft sites.
Read more: https://cert-agid.gov.it/news/il-tema-spid-sfruttato-per-una-nuova-campagna-di-phishing/