XWorm is a versatile remote access trojan (RAT) used by threat actors targeting software supply chains and gaming industries, employing varied stagers and loaders to evade detection. Splunk’s Threat Research Team analyzed recent samples and provided multiple detection techniques to help identify XWorm activity in enterprise environments. #XWorm #LockBit #AsyncRAT
Keypoints
- XWorm RAT has evolved into a modular, frequently updated malware used for keylogging, remote access, data exfiltration, and command execution.
- Threat actors use XWorm alongside AsyncRAT and ransomware payloads linked to the LockBit ransomware group.
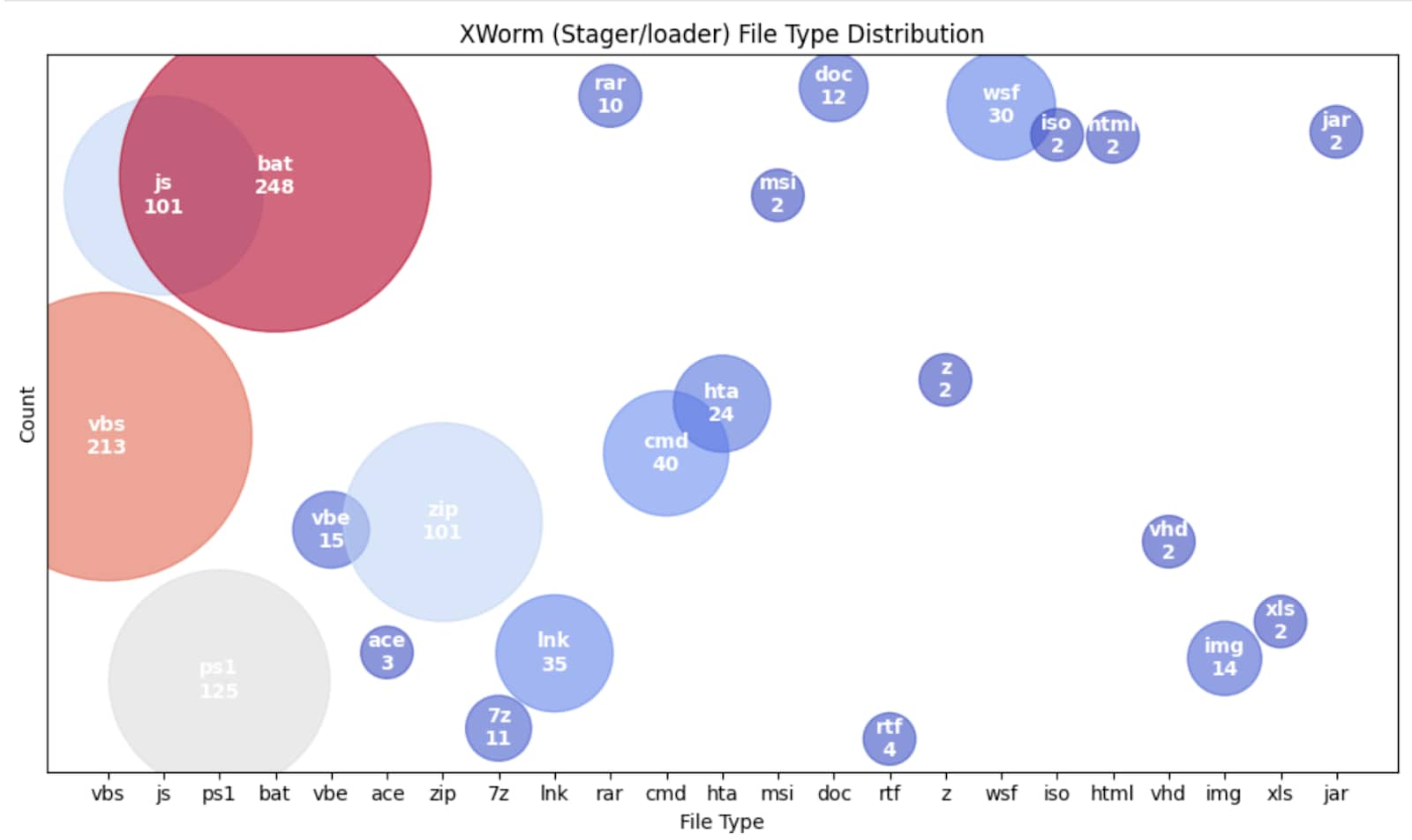
- XWorm uses diverse initial access vectors including PowerShell, VBS, batch scripts, .hta, .lnk, ISO, and Office macros to evade detection.
- The malware employs obfuscation, disables Windows AMSI and ETW for defense evasion, and establishes persistence via registry keys and scheduled tasks.
- XWorm performs process injection, API hooking, and modifies Microsoft Defender exclusion settings to maintain stealth and persistence.
- It gathers system information including antivirus software, GPU details, and device drivers to aid in its operations.
- Splunk provides a comprehensive set of 31 analytic detections to identify and mitigate XWorm activities in affected systems.
MITRE Techniques
- [T1059.001] PowerShell – Used to execute scripts that download payloads and bypass execution policies (‘powershell -ExecutionPolicy Bypass -File’).
- [T1204.002] Malicious File – Execution of malicious .hta and PowerShell downloader files to retrieve XWorm payloads.
- [T1027] Obfuscated Files or Information – Use of obfuscated .vbs and .bat scripts to hinder analysis and detection.
- [T1562.001] Impair Defenses: Disable or Modify Tools – Patching AmsiScanBuffer() and EtwEventWrite() functions to evade antivirus and logging mechanisms.
- [T1547.001] Registry Run Keys – Creating registry keys to maintain persistence by executing stager scripts.
- [T1053] Scheduled Task/Job – Establishing scheduled tasks for persistence and potential privilege escalation.
- [T1027.013] Encrypted/Encoded File – Decrypting AES-encrypted files and decompressing GZIP data for payload delivery.
- [T1574.001] Hijack Execution Flow: DLL Side-Loading – Attempts to load a malicious DLL via DLL side-loading through msconfig.exe.
- [T1055] Process Injection – Injecting shellcode into system processes like Taskmgr, explorer, or svchost for stealth and execution.
- [T1518.001] Security Software Discovery – Querying WMI to detect installed antivirus software.
- [T1652] Device Driver Discovery – Retrieving webcam or capture device driver information using capGetDriverDescriptionA() API.
- [T1082] System Information Discovery – Using WMI to collect GPU details of the infected host.
- [T1091] Replication Through Removable Media – Spreading via removable drives with copies of malicious executables and shortcut files.
- [T1219] Remote Access Tools – Processing backdoor commands received from C2 servers for various malicious activities.
- [T1071.001] Web Protocols – Utilizing HTTP POST requests with a custom User-Agent for C2 communication.
Indicators of Compromise
- [File Hashes] XWorm component hashes – 78b15b9b54925120b713a52a09c66674463bd689e3b01395801ef58c77651127 (Bat loader), 0f10d6cbaf195a7b0c9f708b7f0a225e2de29beb769bdf8d1652b682b1c4679f (Powershell script), and others including batch scripts, VB scripts, .hta and JavaScript files.
- [File Names] Phishing lures targeting users – filenames resembling invoices, receipts, delivery and shipping notifications used to trick victims into launching malicious files.
Read more: https://www.splunk.com/en_us/blog/security/xworm-shape-shifting-arsenal-detection-evasion.html