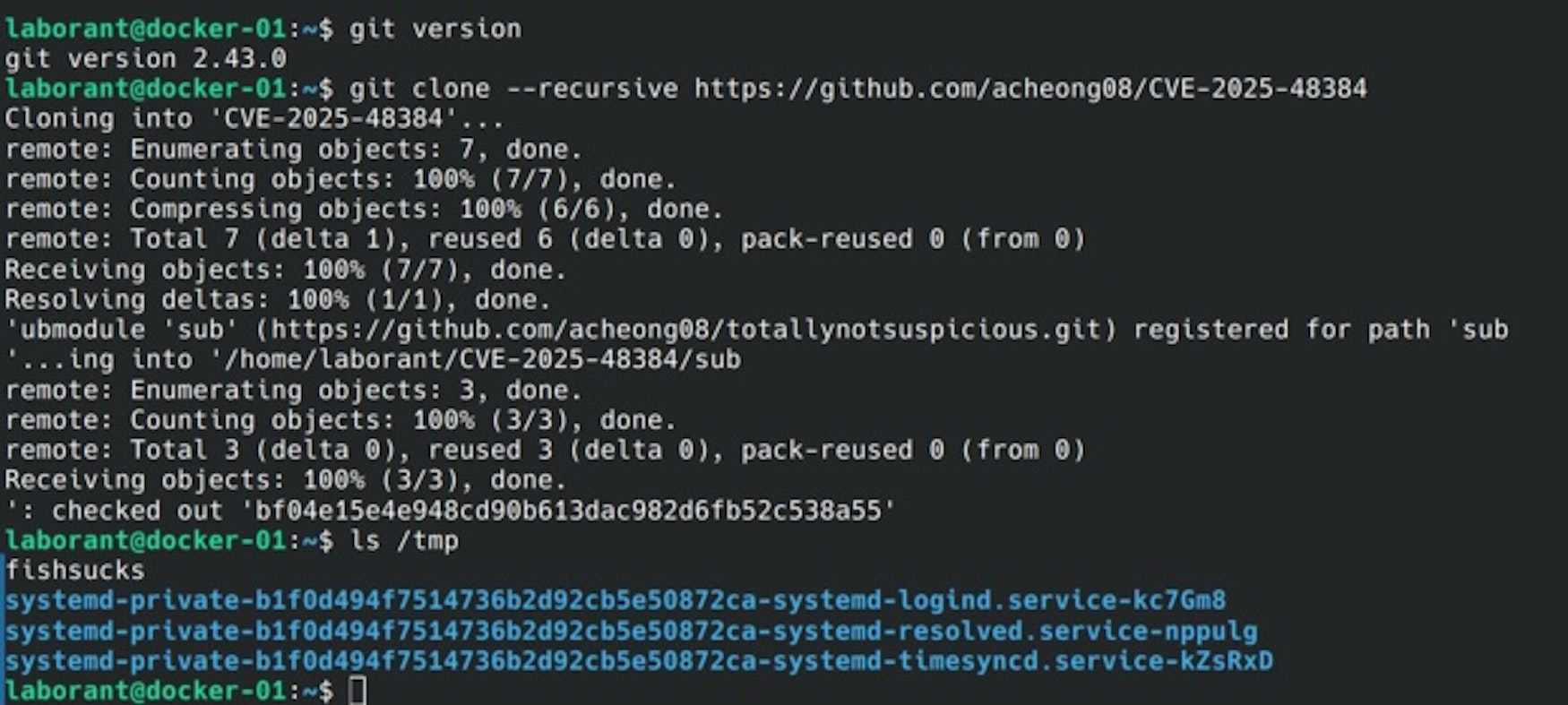
CVE-2025-48384 is a critical vulnerability in Git CLI versions 2.50.0 and earlier that allows arbitrary file write and remote code execution via malicious repositories using the –recursive clone option. The GitHub Desktop client for macOS is also vulnerable, and no patch is currently available for it, making users advised to switch to patched Git CLI versions urgently. #CVE202548384 #GitCLI #GitHubDesktop
Keypoints
- The vulnerability allows attackers to perform arbitrary file writes by exploiting Git’s handling of .gitmodules files containing carriage return characters, leading to remote code execution.
- Git CLI versions 2.50.0 and prior on macOS and Linux are vulnerable; Windows is not affected due to system differences.
- The GitHub Desktop client for macOS is vulnerable due to its default use of git clone –recursive, with no patch currently available.
- An attacker could deploy malicious Git Hook scripts or overwrite Git configuration files to maintain persistence or steal intellectual property unnoticed.
- Official patches were released for Git CLI on July 8, 2025, with users advised to upgrade to version 2.50.1 or later immediately.
- Security recommendations include auditing submodules in .gitmodules before cloning repositories from untrusted sources and using patched Git CLI versions instead of GitHub Desktop on macOS.
- Datadog provides queries and custom detection rules for Workload Protection and Cloud Security to identify usage of vulnerable Git versions and potential exploitation attempts.
MITRE Techniques
- [T1222] File and Directory Permissions Modification – The vulnerability allows arbitrary file writes by manipulating .gitmodules file parsing and subsequent writing of malicious Git Hook scripts (‘attackers can manipulate the internal submodule paths and cause Git to write files to unexpected locations’).
- [T1059] Command and Scripting Interpreter – Execution of malicious Git Hook scripts results in executing arbitrary code during common Git commands such as commit or merge.
- [T1027] Obfuscated Files or Information – Attackers exploit carriage return character handling to bypass normal configuration parsing and redirect writes stealthily (‘Git’s config parser behavior preserves carriage return characters on write’).
- [T1531] Account Access Removal – Overwriting Git configuration files can be used to stealthily exfiltrate intellectual property, allowing persistent malicious activity under the guise of standard Git operations.
Indicators of Compromise
- [File Hashes] Proof-of-concept exploit files publicly available – Examples include arbitrary write exploit scripts targeting /tmp directory and malicious Git Hook script hashes (specific hashes not listed, “and 2 more hashes”).
- [File Names] Malicious Git Hook scripts – Files written to .git/hooks subdirectory on victim machines, enabling remote code execution.
- [Configuration Files] Modified Git config files – Overwritten remote “origin” sections used to exfiltrate intellectual property to attacker-controlled servers.
Read more: https://securitylabs.datadoghq.com/articles/git-arbitrary-file-write/