RenderShock is a zero-click attack framework that exploits passive file preview, indexing, and automation in modern operating systems to execute malicious payloads without user interaction. It leverages trusted system features to perform reconnaissance, credential theft, remote code execution, and persistence, posing significant stealth and detection challenges. #RenderShock #NTLMLeak #RemoteTemplateInjection
Category: Threat Research
The article explores the rising threat of ClickFix campaigns, detailing how attackers use social engineering to trick users into executing malicious commands across various industries in 2025. It highlights prominent campaigns delivering NetSupport RAT, Latrodectus, and Lumma Stealer malware and provides hunting and mitigation strategies to combat these threats. #ClickFix #NetSupportRAT…

Privilege escalation vulnerabilities in Java Spring applications often evade dynamic testing but can be effectively detected through secure code review by analyzing authorization logic in the source code. This article outlines authorization implementation patterns in Spring Security and provides a practical step-by-step guide for identifying and mitigating authorization flaws during code review. #JavaSpring #PrivilegeEscalation #SecureCodeReview

Three real-world cloud compromises affecting Microsoft Azure and Amazon Web Services environments were analyzed, revealing threat actors using stolen credentials to gain unauthorized access, exfiltrate data, and deploy ransomware. The cases highlight the importance of AI-driven anomaly detection and autonomous response to contain attacks and prevent escalation. #MicrosoftAzure #AmazonWebServices #Rclone #AkiraRansomware

SafePay ransomware rapidly emerged in early 2025 as a highly active and dangerous threat, targeting over 200 victims worldwide, including managed service providers and SMBs. It employs sophisticated techniques such as disabling endpoint protections, exfiltrating data via network shares, and encrypting files using a combination of AES and RSA, with many similarities to the LockBit ransomware family. #SafePay #LockBit #IngramMicro

AiLock ransomware, first identified in March 2025, employs advanced encryption techniques including ChaCha20 and NTRUEncrypt to target files selectively based on size and uses a multi-threaded IOCP approach for encryption. The ransomware group actively updates its negotiation and data leak sites, signaling ongoing and future operations. #AiLock #NTRUEncrypt
Attackers frequently inject malicious code into website theme files like footer.php to execute browser redirects without the knowledge of site administrators. This method exploits the fact that themes load on every page and are not easily monitored for unauthorized changes. #BrowserRedirect #FooterPHP #WebsiteThemeInjection

This report analyzes a malware campaign hosted on GitHub that disguises the Lumma Stealer payload as legitimate tools like “Free VPN for PC” and “Minecraft Skin Changer.” The malware uses advanced obfuscation, process injection, and DLL side-loading techniques to evade detection while communicating with multiple C2 domains. #LummaStealer #GitHubMalware #LaunchExe

This article examines the prevalence of misleading and recycled data breaches in threat intelligence, highlighting how such noise complicates effective cybersecurity response. It provides a framework to differentiate genuine threats from false alarms caused by sensationalized reports, underground forums, and fabricated datasets. #16BillionCredentialLeak #BreachForums #ICMRDataLeak

This report highlights significant cyber threats targeting the financial sector, including a major data breach of 44 million Indonesian users by the threat actor Bjorka and a ransomware attack by the Everest group on J*** Bank in Jordan. It emphasizes the need for enhanced security measures such as real-time protection systems…

The unpatched GeoServer vulnerability CVE-2024-36401 continues to be exploited by threat actors to install malware such as NetCat and XMRig CoinMiner, with confirmed cases in South Korea. Attackers use PowerShell and Bash scripts to deploy these malicious tools, enabling remote control and cryptocurrency mining. #GeoServer #CVE202436401 #NetCat #XMRig…
Pay2Key.I2P, an Iranian-backed ransomware-as-a-service linked to the Fox Kitten APT group and Mimic ransomware, has rapidly expanded its operations targeting Western organizations with ideological motives. The ransomware includes advanced evasion techniques and recently added Linux targeting, collecting over $4 million in ransom payments within four months. #Pay2Key.I2P #FoxKitten #MimicRansomware

Varonis Threat Labs discovered a critical vulnerability named Count(er) Strike in ServiceNow’s platform that allowed minimal-access users to infer and exfiltrate sensitive data across multiple tables. ServiceNow addressed the issue by releasing security updates and introducing new access control mechanisms like Query ACLs and Security Data Filters. #CounterStrike #ServiceNow #CVE-2025-3648…

BloodHound and its associated collectors—SharpHound, SoapHound, and ShadowHound—are powerful tools used to analyze and visualize Active Directory relationships, identifying potential attack paths and privilege escalation routes within networks. These tools, employed by advanced threat actors such as the Ryuk and Play ransomware gangs, enable both attackers and defenders to discover vulnerabilities related to permissions, misconfigurations, and domain structures. #BloodHound #SharpHound #SoapHound #ShadowHound #Ryuk #PlayRansomware
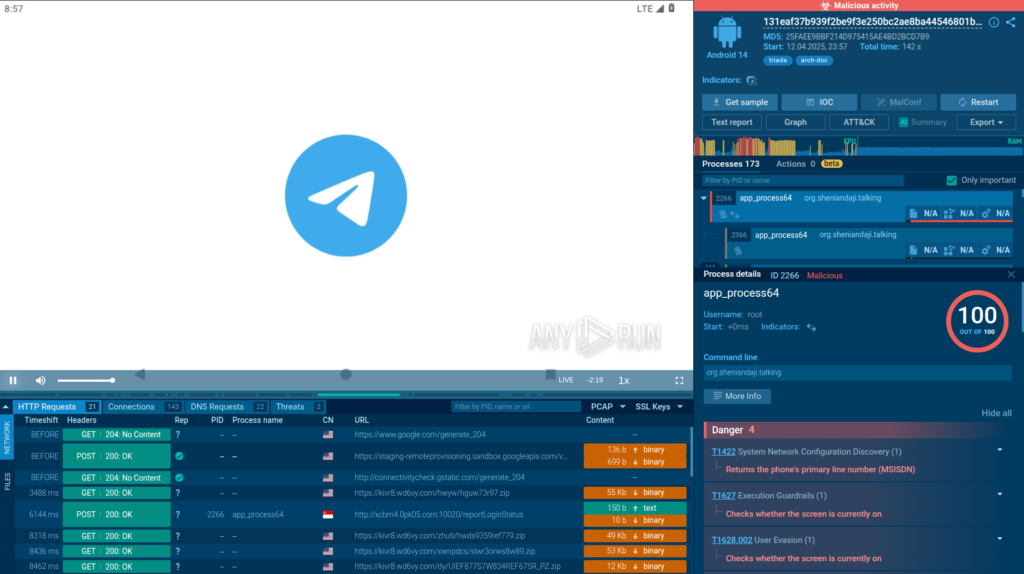
The article analyzes the advanced Android packer named Ducex, used by the Triada malware to obfuscate and encrypt its payload, complicating detection and analysis. It reveals Ducex’s use of modified RC4 encryption, self-debugging, anti-debugging techniques, and payload storage within the classes.dex file. #Triada #Ducex #libducex #SM4…