This article details three separate cloud environment intrusions targeting Microsoft Azure and Amazon Web Services (AWS) customers, involving stolen credentials, unauthorized access, data exfiltration, and ransomware deployment. It emphasizes the importance of anomaly detection, autonomous response, and continuous monitoring to mitigate such threats effectively. #MicrosoftAzure #AmazonWebServices #Darktrace #Rclone #AkiraRansomware
Category: Threat Research

Researchers at ReversingLabs uncovered a sophisticated supply chain attack compromising the ETHcode VS Code extension through a malicious GitHub pull request that introduced a deceptive dependency. This attack demonstrates the risks posed by software supply chain vulnerabilities in trusted developer tools and emphasizes the need for thorough review of new contributors and dependencies. #ETHcode #keythereum-utils #7finney
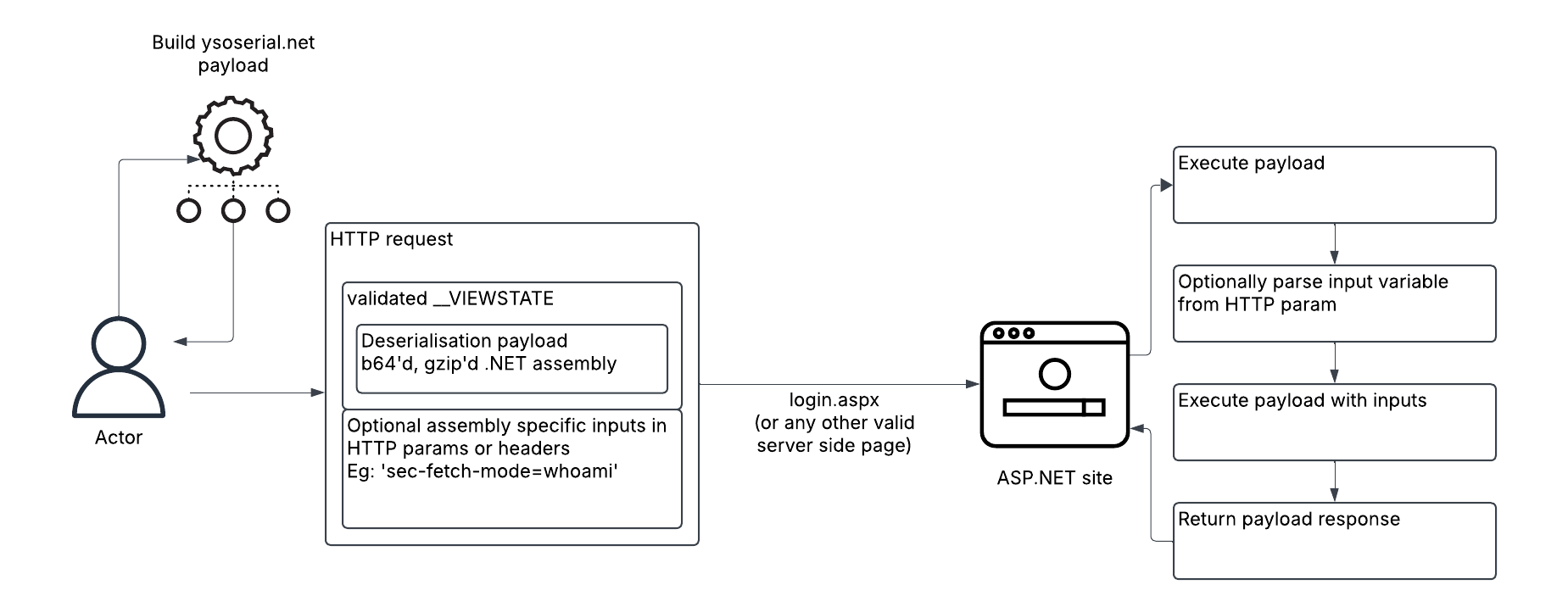
Unit 42 researchers identified a campaign by the group TGR-CRI-0045 exploiting leaked ASP.NET Machine Keys to perform View State deserialization attacks on IIS servers, enabling in-memory execution of malicious payloads with minimal forensic traces. The group, attributed with medium confidence to Gold Melody, targeted organizations across various industries in the US…
NetSPI discovered a Remote Code Execution vulnerability in SailPoint’s IQService component due to default insecure configurations including a hard-coded encryption key and lack of authentication. An exploit was developed demonstrating unauthenticated command execution, leading SailPoint to enforce TLS and client authentication in updates. #SailPointIQService #RemoteCodeExecution #NetSPI

The vulnerability CVE-2025-5777, known as "CitrixBleed 2," affects Citrix NetScaler ADC and Gateway and has been actively exploited following the release of a public Proof-of-Concept. Numerous Italian organizations, including public administrations and financial institutions, remain vulnerable due to delayed patching, prompting urgent mitigation efforts. #CVE20255777 #CitrixBleed2 #CERTAGID
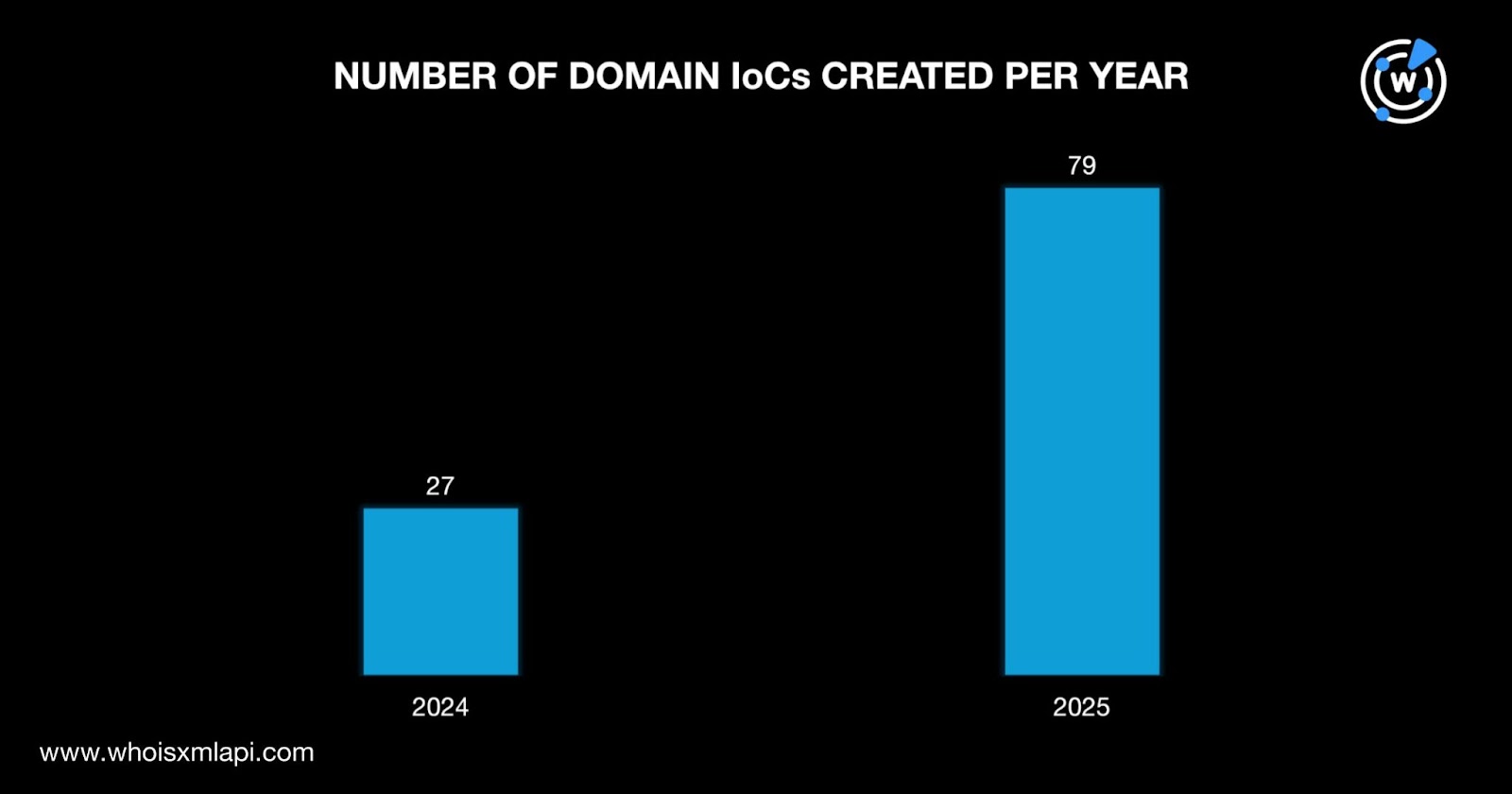
The U.S. Department of Justice seized 114 domains linked to a major information-stealing campaign using Lumma Stealer. Analysis revealed the domains were recently created, primarily registered through PDR and originating mostly from Russia, with many domain and IP indicators confirmed as malicious. #LummaStealer #DOJ #PDR
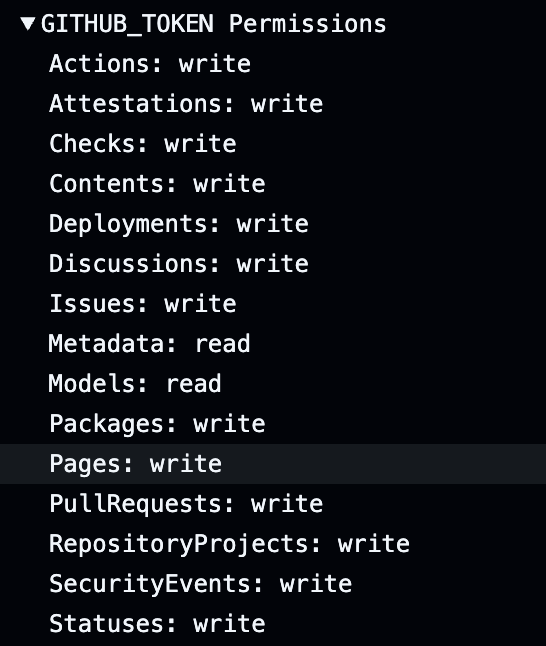
A critical vulnerability, CVE-2025-53104, affecting the gluestack-ui GitHub repository can be exploited to execute arbitrary commands on GitHub Actions runners, leading to secret exfiltration and repository compromise. This vulnerability was patched on June 13, 2025, but poses serious risks to NPM package integrity and confidentiality. #CVE202553104 #gluestack #GitHubActions

A new cross-platform botnet family named hpingbot, developed in Go language, is rapidly spreading and evolving with capabilities to launch DDoS attacks using the hping3 tool and distribute arbitrary payloads via Pastebin. The botnet shows strong innovation with independent propagation modules, multiple persistence mechanisms, and frequent updates, posing a significant threat as a potential long-term malware operation with risks of distributing advanced threats like ransomware or APT components. #hpingbot #hping3 #Pastebin

A recent resurgence of XMRig cryptominer malware was observed in April 2025, coinciding with a rally in Monero cryptocurrency prices and a major bitcoin theft converted to Monero. The malware employs multi-staged attacks utilizing LOLBAS techniques and Windows built-in tools to achieve persistence and evade detection. #XMRig #Monero #notif_su

A sophisticated phishing campaign impersonates Hungary’s HunCERT and other organizations by hosting credential-harvesting pages on Amazon S3 and using Cloudflare Turnstile for legitimacy. The campaign employs the Logokit phishing kit to automate branding and targets banking, logistics, and charitable institutions globally, with ongoing operations using the C&C domain mettcoint[.]com. #HunCERT #Logokit #mettcoint
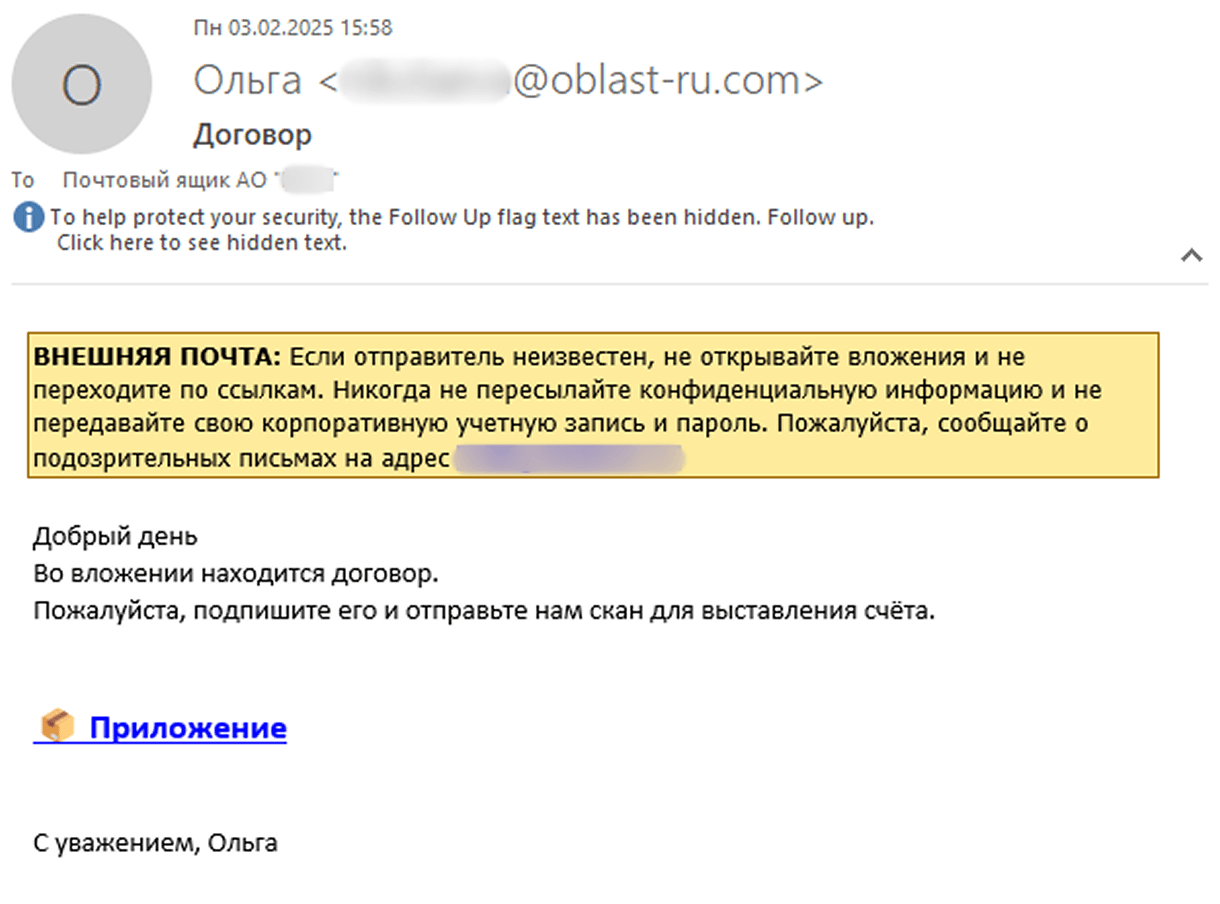
Since July 2024, the Batavia spyware campaign has targeted Russian industrial enterprises through malicious email attachments disguised as contracts, leading to a multi-stage infection process and data exfiltration. The malware comprises a VBS downloader script and two executable files that steal internal documents and system information. #Batavia #WebView.exe #javav.exe
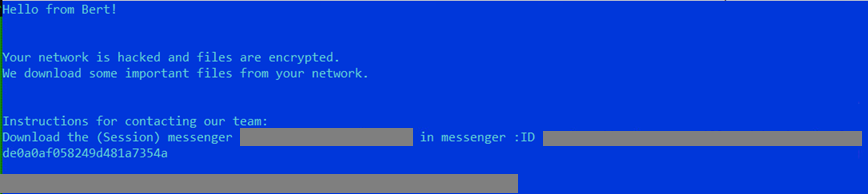
BERT is a newly emerged ransomware group active in Europe, Asia, and the US, targeting multiple sectors including healthcare and technology with Windows and Linux variants. Their tactics involve PowerShell loaders, privilege escalation, and fast multi-threaded encryption, including forced shutdowns of ESXi virtual machines to maximize damage. #BERT #WaterPombero #ESXi #PowerShell…

ASEC identified that XwormRAT malware is distributed via phishing emails using steganography embedded in JPG files to conceal the .NET loader and final payload. The malware initiation involves VBScript or JavaScript that triggers a PowerShell script to decode and execute the hidden malware, making detection difficult. #XwormRAT #ASEC #steganography…

A large-scale campaign involving over 40 fake Firefox extensions has been identified, designed to steal cryptocurrency wallet credentials by impersonating legitimate wallet tools like MetaMask and Coinbase. The campaign, active since at least April 2025, employs fake reviews and cloned open-source code to deceive users and quietly exfiltrate sensitive data. #MetaMask #Coinbase #FirefoxExtensions #CryptocurrencyTheft
Two critical vulnerabilities (CVE-2025-5349 and CVE-2025-5777) and a third critical zero-day RCE vulnerability (CVE-2025-6543) were disclosed in Citrix NetScaler ADC and Gateway products, exposing systems to unauthorized access and memory overflow attacks. Exploitation evidence has been observed in the wild, and users are strongly advised to update to patched versions immediately. #CitrixBleed2 #CVE20256543 #NetScalerADC
