Since July 2024, the Batavia spyware campaign has targeted Russian industrial enterprises through malicious email attachments disguised as contracts, leading to a multi-stage infection process and data exfiltration. The malware comprises a VBS downloader script and two executable files that steal internal documents and system information. #Batavia #WebView.exe #javav.exe
Keypoints
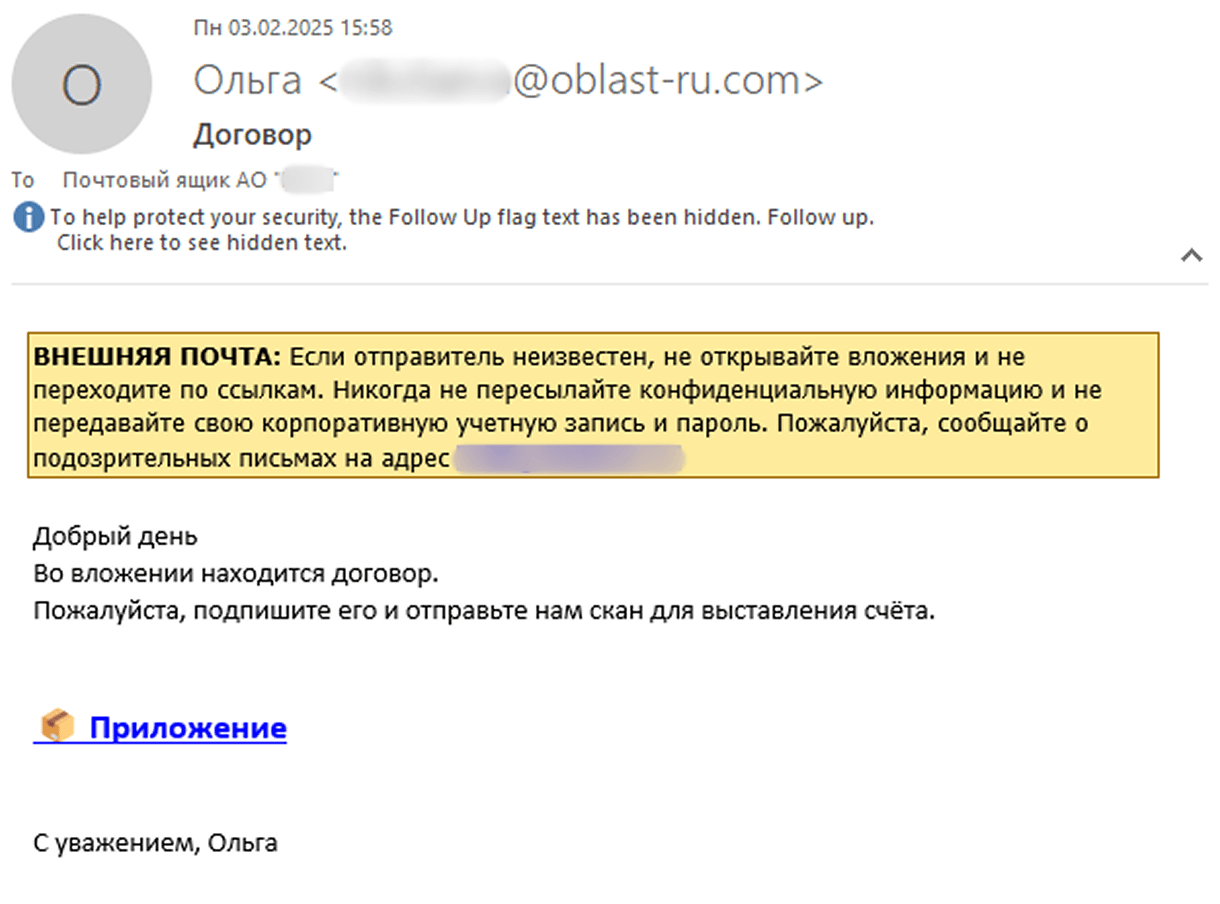
- Batavia spyware campaign started in July 2024 and targets Russian organizations via bait emails with malicious links pretending to be contracts.
- The infection involves three stages: a VBS downloader script, followed by execution of WebView.exe, then javav.exe, each performing specific data theft functions.
- The VBS script downloads an encrypted file and retrieves parameters from a command-and-control (C2) server to adapt the attack based on the victim’s OS.
- WebView.exe collects system logs and office documents, takes screenshots, and downloads further payloads while communicating with a different C2 domain.
- javav.exe expands file collection to include images, emails, archives, and other document types and introduces commands to change C2 servers and load extra modules.
- UAC bypass technique using computerdefaults.exe and registry modification is used to launch additional malicious payloads like windowsmsg.exe.
- More than 100 users across several dozen Russian industrial companies were targeted according to Kaspersky telemetry data.
MITRE Techniques
- [T1548.002] Bypass User Account Control – The malware uses the Windows utility computerdefaults.exe and registry key modification via reg.exe to bypass UAC and execute malicious payloads (‘add HKCUSoftwareClassesms-settingsShellOpencommand /v DelegateExecute /t REG_SZ /d “” /f’).
Indicators of Compromise
- [File Hash] Malicious files used in infections – Договор-2025-2.vbe (2963FB4980127ADB7E045A0F743EAD05), webview.exe (5CFA142D1B912F31C9F761DDEFB3C288), javav.exe (03B728A6F6AAB25A65F189857580E0BD)
- [Domain] Command and control servers delivering payloads – oblast-ru[.]com, ru-exchange[.]com
- [File Name] Malicious scripts and executables – Договор-2025-2.vbe, WebView.exe, javav.exe, windowsmsg.exe (payload)
Read more: https://securelist.com/batavia-spyware-steals-data-from-russian-organizations/116866/