BERT is a newly emerged ransomware group active in Europe, Asia, and the US, targeting multiple sectors including healthcare and technology with Windows and Linux variants. Their tactics involve PowerShell loaders, privilege escalation, and fast multi-threaded encryption, including forced shutdowns of ESXi virtual machines to maximize damage. #BERT #WaterPombero #ESXi #PowerShell #TrendVisionOne
Keypoints
- BERT ransomware targets both Windows and Linux platforms, affecting sectors such as healthcare, technology, and event services across Asia, Europe, and the US.
- The group uses PowerShell-based loaders like start.ps1 to escalate privileges, disable security features, and deploy the ransomware payload from a Russian-associated IP address.
- BERT’s ransomware employs multi-threaded encryption, with the Linux variant using up to 50 threads and forcibly shutting down ESXi virtual machines to hinder recovery efforts.
- The ransomware code has evolved from storing file paths before encryption to concurrent queue processing, improving encryption speed and efficiency.
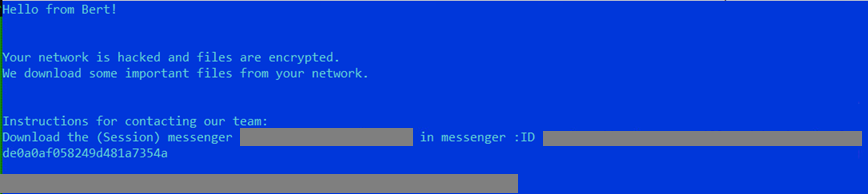
- BERT variants append file extensions such as “.encryptedbybert” (Windows) and “.encrypted_by_bert” (Linux) and drop ransom notes in victim systems.
- The group’s Linux variant possibly derives from REvil ransomware code, indicating reuse of known ransomware frameworks targeting ESXi servers.
- Trend Vision One detects and blocks BERT-related IOCs and offers hunting queries, threat insights, and intelligence reports to aid defense.
MITRE Techniques
- [T1059.001] Command and Scripting Interpreter: PowerShell – Uses PowerShell scripts to execute the ransomware payload and perform post-infection activities (“Uses PowerShell to perform its activities and run the payload”).
- [T1562.001] Impair Defenses: Disable or Modify Tools – Disables Windows Defender and security tools via PowerShell script (“Disabling Defender and related protections by modifying the registry using PowerShell”).
- [T1562.004] Impair Defenses: Disable or Modify System Firewall – Disables domain, public, and private firewall profiles through PowerShell commands (“Disables Domain, Public and Private Firewall profiles using the PowerShell command Set-NetFirewallProfile”).
- [T1548.002] Abuse Elevation Control Mechanism: Bypass User-Account Control – Bypasses UAC prompt allowing privilege escalation (“Disabling UAC allows program to elevate its privilege without prompting the user through the UAC notification box”).
- [T1083] File and Directory Discovery – Enumerates files and directories prior to encryption on Windows and Linux systems (“Enumerating files and directories”).
- [T1673] Virtual Machine Discovery – Enumerates VM images on Linux systems using esxcli (“Uses the command esxcli vm process list to enumerate VM images”).
- [T1057] Process Discovery – Identifies and terminates key processes on Windows before encryption (“Identifying and stopping key services”).
- [T1486] Data Encrypted – Encrypts files on victim systems using multi-threaded processes on Windows and Linux (“Encrypting victim’s files”).
- [T1485] Data Destruction – Destroys data to prevent recovery post-encryption (“Destroying data to prevent recovery”).
- [T1490] Inhibit System Recovery – Encrypts VM snapshots on ESXi hosts to inhibit recovery (“Encrypts snapshots of Virtual Machines (ESXi)”).
Indicators of Compromise
- [IP Address] Ransomware payload download server – 185[.]100[.]157[.]74 used to host payload.exe and start.ps1 loader script.
- [File Hashes] Windows PowerShell loader and ransomware payload samples – b2f601ca68551c0669631fd5427e6992926ce164f8b3a25ae969c7f6c6ce8e4f (start.ps1 script), 75fa5b506d095015046248cf6d2ec1c48111931b4584a040ceca57447e9b9d71 (BERT Windows ransomware).
- [File Hashes] Linux variant ransomware sample – c7efe9b84b8f48b71248d40143e759e6fc9c6b7177224eb69e0816cc2db393db.
- [File Extensions] Encrypted files marked with “.encryptedbybert” on Windows and “.encrypted_by_bert” on Linux.
- [File Names] Ransom notes named encrypted_by_bert-decrypt.txt on Linux and standard ransom notes on Windows variants.