The article analyzes a severe memory leak vulnerability, CVE-2025-5777, affecting Citrix Netscaler devices, which allows attackers to extract uninitialized memory data via crafted HTTP requests. This flaw is actively exploited in the wild, posing risks similar to the infamous CitrixBleed vulnerability, with many users yet to apply patches. #CVE20255777 #CitrixNetscaler #CitrixBleed
Category: Threat Research
APT36 (Transparent Tribe) has launched a sophisticated cyber-espionage campaign targeting the Indian defense sector using Linux-focused malware delivered via phishing emails. The campaign employs a multi-stage attack involving a malicious .desktop file that downloads a decoy PowerPoint and executes an ELF binary payload to gain unauthorized access. #APT36 #BOSSLinux #TransparentTribe

Cisco has issued urgent patches for a critical vulnerability (CVE-2025-20309) in Unified Communications Manager that allows root access via hard-coded credentials. Several advanced threat actors, including APT28 and MuddyWater, are likely to exploit this flaw on over a thousand exposed devices worldwide. #CVE-2025-20309 #UnifiedCommunicationsManager #APT28 #MuddyWater
In June 2025, eSentire’s Threat Response Unit uncovered a trojanized version of SonicWall’s NetExtender VPN client, named “SilentRoute,” which exfiltrates user credentials to a threat actor’s server. The malware bypassed security protections using a fraudulently obtained GlobalSign digital certificate and sophisticated code modifications to mimic legitimate software. #SilentRoute #SonicWall #GlobalSign
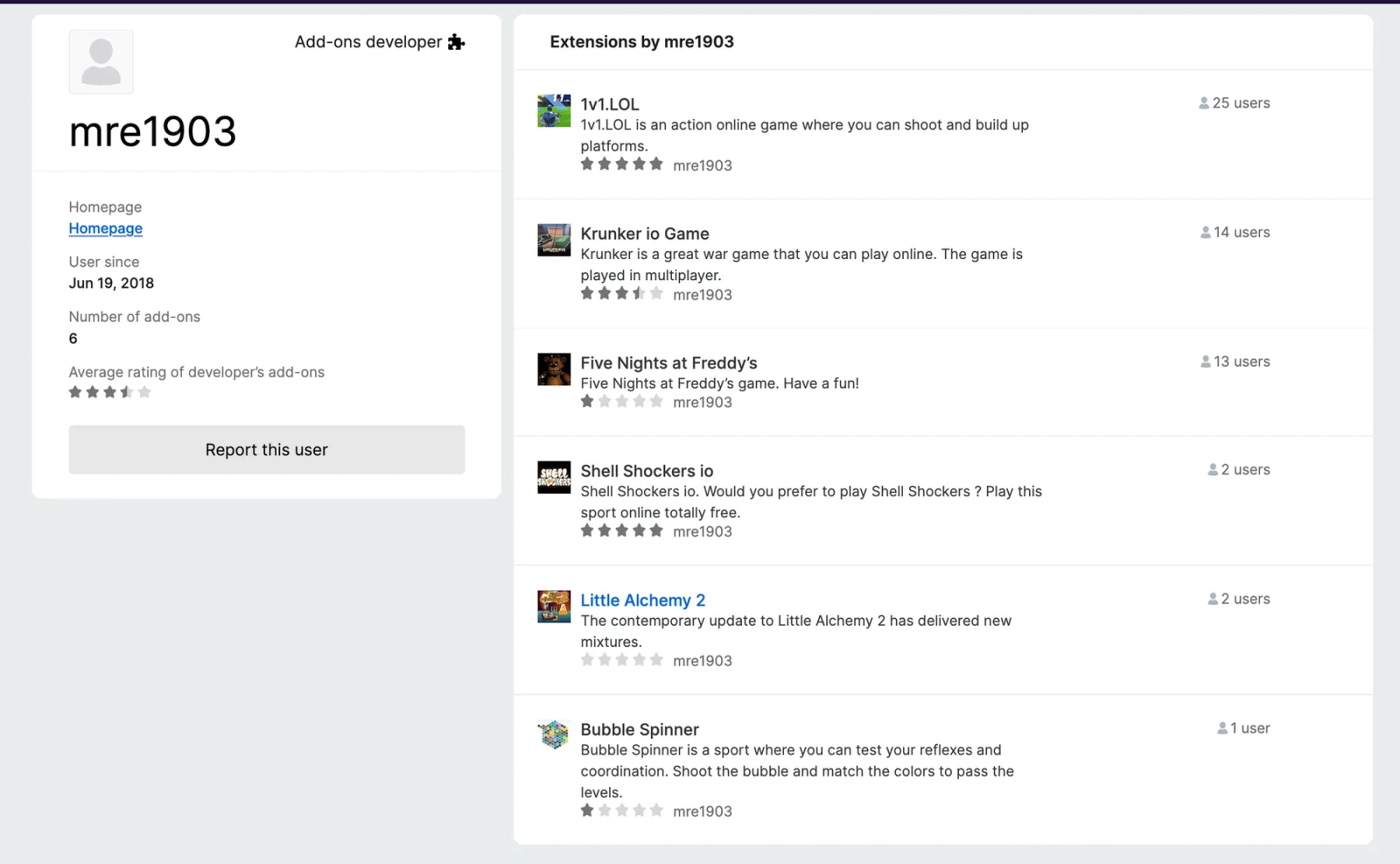
Malicious browser extensions disguised as popular games and useful tools are increasingly targeting users across major browsers, employing tactics like redirects to scam sites, affiliate hijacking, and OAuth credential theft. The threat actor mre1903 leads a coordinated campaign of fake gaming extensions, while others like GimmeGimme and CalSyncMaster perform affiliate fraud and steal Google authentication tokens, respectively. #mre1903 #CalSyncMaster #GimmeGimme

A malicious Excel file named blcopy.xls uses steganography to embed and load multiple payloads, including a PowerShell script hidden within a JPEG image. The final payload is a DLL, likely a Katz stealer, delivered through a complex multi-stage infection chain involving HTA, BAT, VBS, and VBA scripts. #blcopy.xls #KatzStealer #steganography #PowerShell #VBA

FortiGuard Labs has identified a new botnet named RondoDox exploiting critical vulnerabilities CVE-2024-3721 and CVE-2024-12856 in TBK DVR and Four-Faith router devices, enabling remote command execution and control. The malware employs advanced evasion, persistence, and mimicking techniques to launch distributed denial-of-service (DDoS) attacks and evade detection. #RondoDox #CVE20243721 #CVE202412856

Janela RAT is a repurposed variant of BX RAT, targeting Latin America fintech sectors with multi-stage infection involving GitLab-hosted MSI installers and a malicious Chromium browser extension for data theft. The malware uses obfuscated GoLang and .NET binaries to load payloads, execute commands, and communicate with C2 servers via WebSocket, employing a sophisticated multi-file infection chain and configuration system. #JanelaRAT #BXRAT #GitLab #ChromiumExtension #LATAMFintech
Intelligence Group 13 is a key operational unit within Iran’s IRGC cyber command, integrating cyber-espionage, sabotage, and psychological warfare to conduct hybrid operations against adversaries. This group leverages a complex ecosystem of front companies and propaganda arms like CyberAveng3rs to execute covert intrusions, influence campaigns, and asymmetric retaliation targeting critical infrastructure and public perception. #IntelligenceGroup13 #CyberAveng3rs #ShahidKavehGroup #IRGCCyberCommand

Elastic Security Labs has detected multiple infostealer campaigns leveraging the commercial AV/EDR evasion framework SHELLTER, particularly the Shellter Elite version 11.0 released in April 2025. The framework provides sophisticated evasion capabilities, including polymorphic shellcode, API unhooking, payload encryption, and advanced anti-analysis techniques, which allow threat actors to deploy highly evasive malware. #SHELLTER #ShellterElite #LUMMA #ARECHCLIENT2 #RHADAMANTHYS
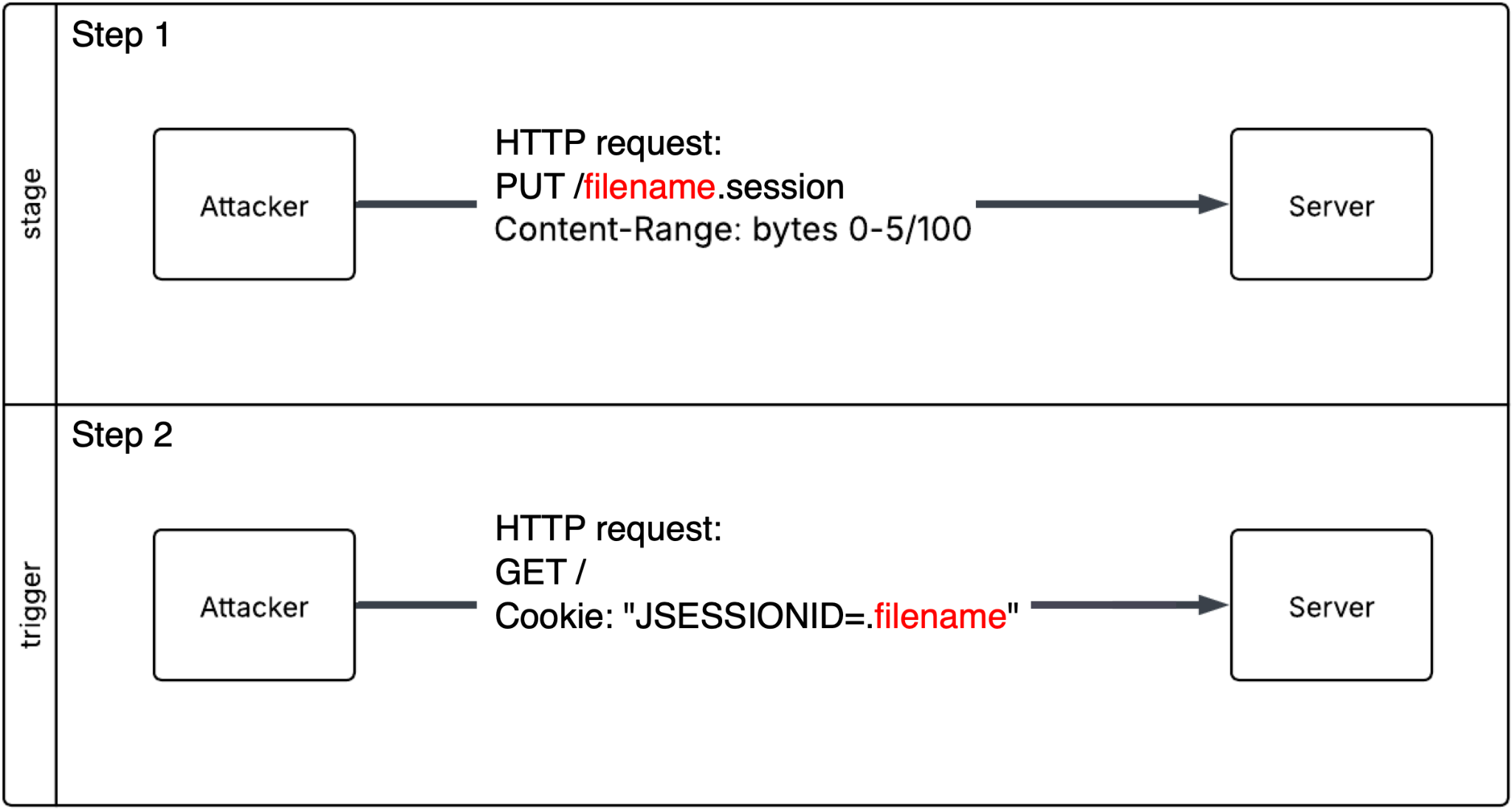
In March 2025, critical remote code execution vulnerabilities were disclosed in Apache Tomcat (CVE-2025-24813) and Apache Camel (CVE-2025-27636 and CVE-2025-29891), exposing millions of developers to potential exploits. Following disclosure, widespread scanning and exploitation attempts were observed globally, emphasizing the urgent need for patching. #CVE2025-24813 #ApacheTomcat #CVE2025-27636 #CVE2025-29891 #ApacheCamel…

A threat actor exploited exposed Java Debug Wire Protocol (JDWP) interfaces on TeamCity CI/CD servers to deploy a customized, stealthy XMRig cryptominer, achieving rapid remote code execution and establishing multiple persistence mechanisms. The attack involved abusing JDWP’s lack of authentication, using disguised payloads, and employing various persistence techniques including systemd services, cron jobs, and shell scripts. #JDWP #XMRig #TeamCity
Threat actors have significantly increased their abuse of the .es top-level domain (TLD) for credential phishing campaigns, with a 19-fold rise from Q4 2024 to Q1 2025, making it the third most abused TLD in early 2025. Most .es domains used in these campaigns host credential phishing pages on randomly generated subdomains, often spoofing Microsoft. #esTLD #CredentialPhishing #MicrosoftSpoofing
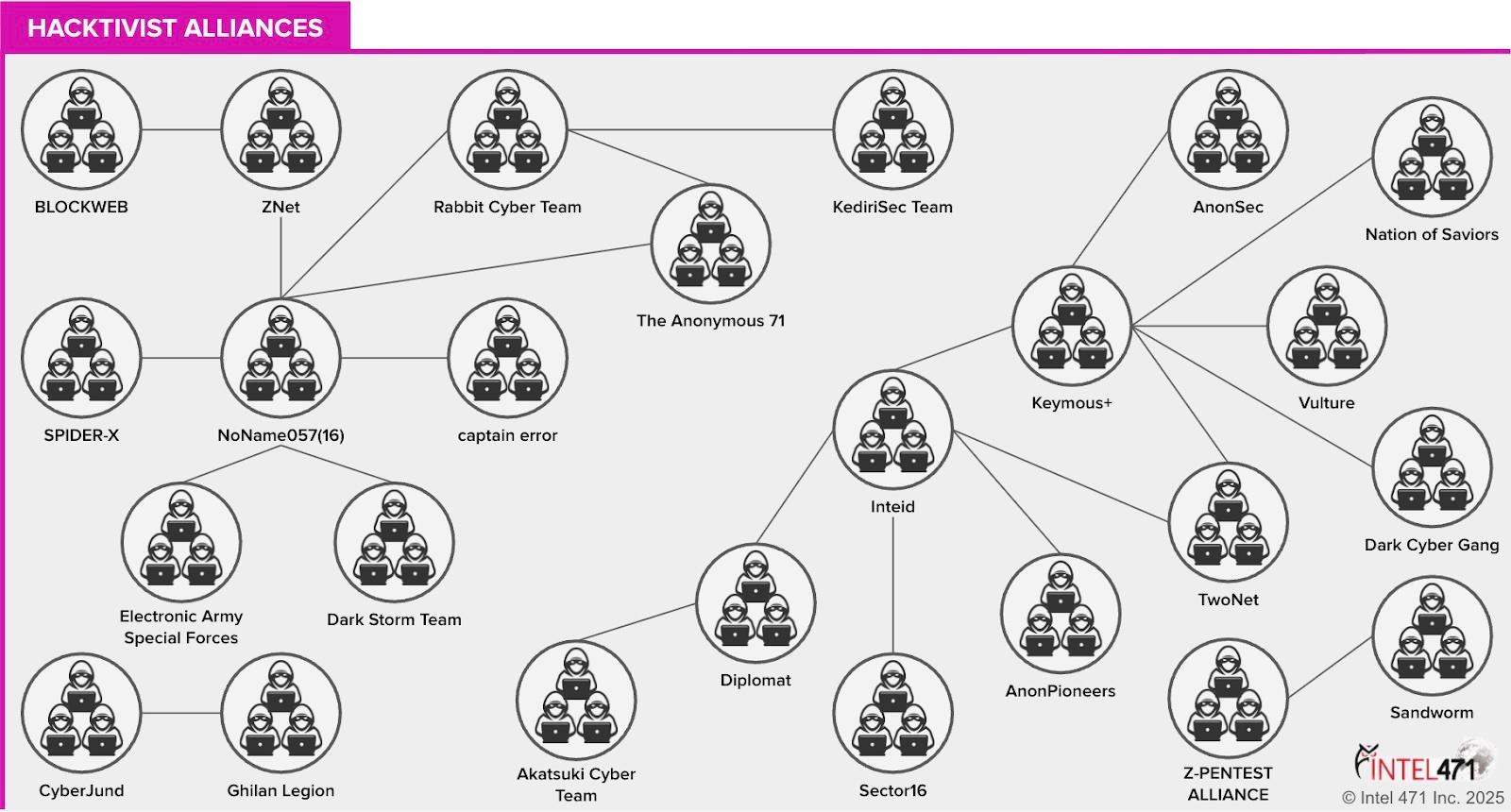
The Russia-Ukraine war has fueled increased pro-Russian hacktivist campaigns involving DDoS attacks, data theft, and website defacements targeting European and allied nations. Key groups like NoName057(16), IT Army of Russia, and TwoNet lead politically motivated cyberattacks, sometimes with suspected ties to Russian state actors. #NoName05716 #ITArmyofRussia #TwoNet #CyberArmyofRussiaReborn
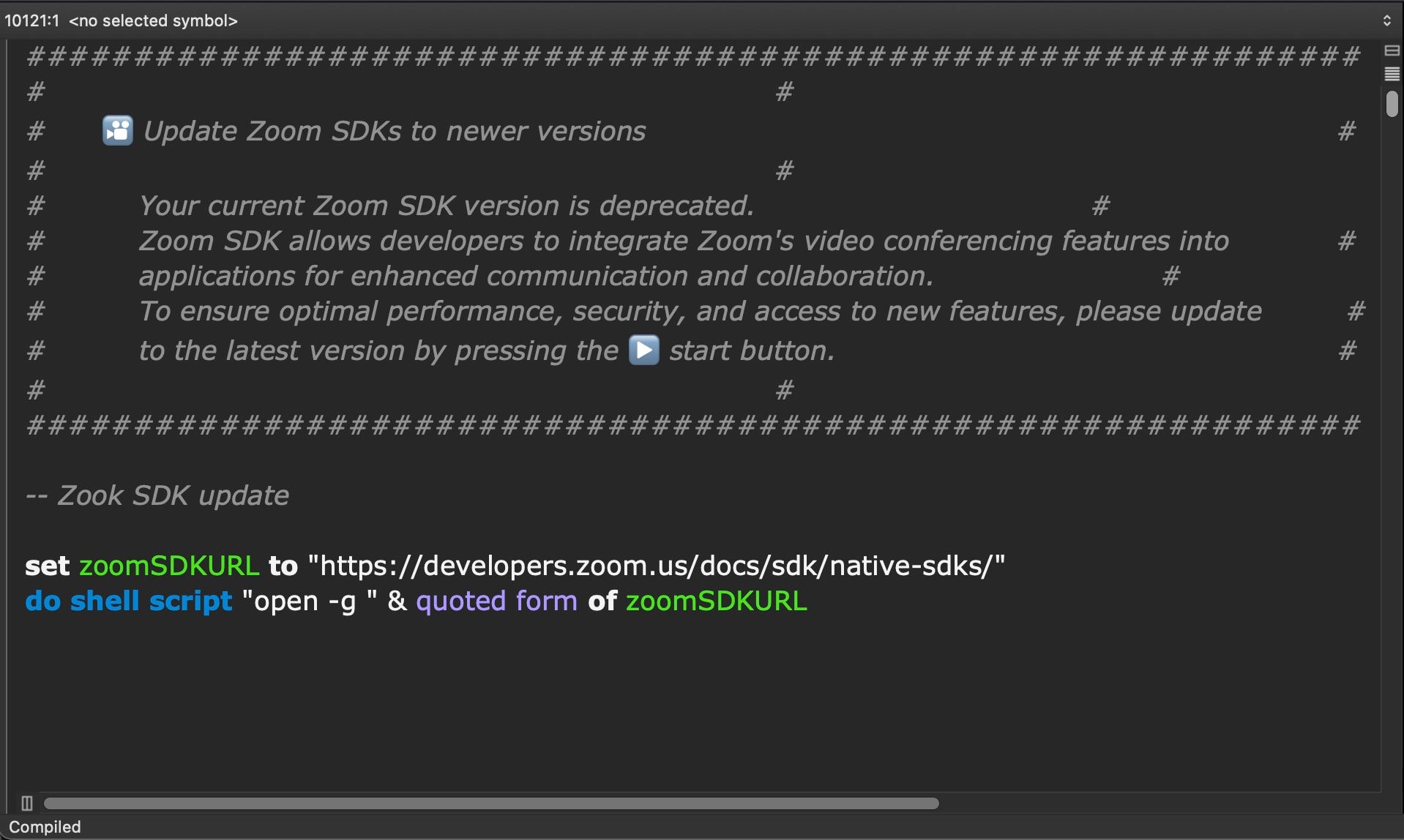
North Korean threat actors employ Nim-compiled binaries and multi-stage attack chains targeting Web3 and cryptocurrency businesses on macOS, utilizing novel persistence methods and process injection techniques. Their malware leverages heavily obfuscated AppleScripts for initial access and continuous backdoor communications, along with Bash scripts to exfiltrate sensitive user data such as browser credentials and Telegram messages. #NimDoor #DPRKThreatActors #macOSMalware #ProcessInjection #AppleScriptBeacon