North Korean threat actors employ Nim-compiled binaries and multi-stage attack chains targeting Web3 and cryptocurrency businesses on macOS, utilizing novel persistence methods and process injection techniques. Their malware leverages heavily obfuscated AppleScripts for initial access and continuous backdoor communications, along with Bash scripts to exfiltrate sensitive user data such as browser credentials and Telegram messages. #NimDoor #DPRKThreatActors #macOSMalware #ProcessInjection #AppleScriptBeacon
Keypoints
- North Korean-aligned threat actors use Nim, C++, and AppleScript in multi-stage macOS malware campaigns targeting Web3 and crypto organizations.
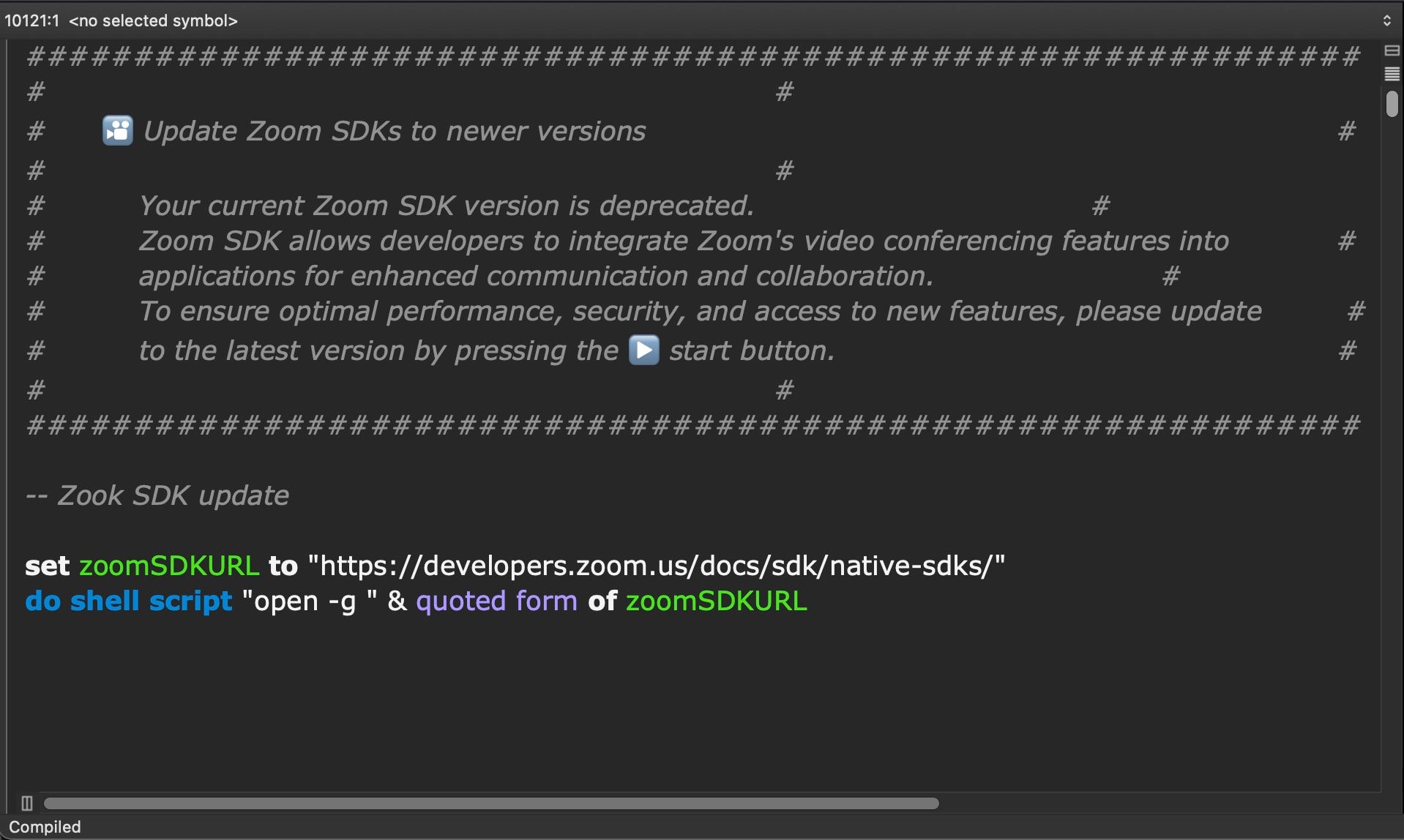
- The attack chain begins with social engineering via Telegram and fake Zoom update scripts delivering malicious AppleScripts.
- NimDoor malware employs a rare macOS process injection method and communicates with C2 servers over wss (WebSocket Secure).
- A novel persistence mechanism intercepts SIGINT and SIGTERM signals to reinstall malware components upon termination attempts or system reboot.
- Bash scripts are used to exfiltrate browser data, Keychain credentials, and Telegram user data to attacker-controlled domains.
- The malware uses obfuscated AppleScripts as lightweight beacons and backdoors, regularly communicating with multiple C2 servers.
- NimDoor’s complex architecture includes binaries named installer, GoogIe LLC, and CoreKitAgent to maintain long-term access and evade detection.
MITRE Techniques
- [T1059.005] AppleScript – Used for initial access and continued backdoor communication with C2 (“The embedded AppleScript … beacons out every 30 seconds… functions both as a beacon and a backdoor.”)
- [T1056.001] Input Capture: Keylogging – Bash scripts exfiltrate user credentials and browser data (“…exfiltrate Keychain credentials, browser data and Telegram user data.”)
- [T1547.001] Boot or Logon Autostart Execution: Launch Agent – Malware establishes persistence using LaunchAgent plist com.google.update.plist (“creates folder paths at [~]/Library/CoreKit/ and [~]/Library/Application Support/GoogIe LLC/ … writes LaunchAgent com.google.update.plist”).
- [T1106] Execution through API – The InjectWithDyldArm64 binary injects code into a suspended process and resumes it for execution (“Target is spawned … in a suspended state… and injected with the trojan1_arm64 binary’s code.”)
- [T1574.001] Hijack Execution Flow: DLL Side-Loading or Injection – Process injection with special entitlements (“The InjectWithDyldArm64 binary has entitlements allowing injection and debugging: com.apple.security.cs.debugger, com.apple.security.get-task-allow.”)
- [T1071.003] Application Layer Protocol: WebSocket – Uses wss to communicate encrypted commands with C2 servers (“After first negotiating an HTTP handshake, the injected code uses wss to communicate with the C2…”)
- [T1543.003] Create or Modify System Process: Launch Agent – Malware writes and sets execution permissions to components upon receiving termination signals (“CoreKitAgent catches SIGINT and SIGTERM signals … writes LaunchAgent for persistence”).
Indicators of Compromise
- [Domains] Command and control and data exfiltration servers – dataupload.store, firstfromsep.online, safeup.store, support.us05web-zoom.pro, writeup.live
- [File Paths] Persistent and working directories on infected macOS systems – ~/Library/Application Support/Google LLC/GoogIe LLC, ~/Library/LaunchAgents/com.google.update.plist, ~/.ses, ~/Library/CoreKit/CoreKitAgent, ~/Library/DnsService/a, /private/tmp/.config, /private/tmp/cfg
- [File Hashes] Malware binaries with SHA-1 hashes – trojan1_arm64 (027d4020f2dd1eb473636bc112a84f0a90b6651c), GoogIe LLC (0602a5b8f089f957eeda51f81ac0f9ad4e336b87c), installer variants (06566eabf54caafe36ebe94430d392b9cf3426ba, 08af4c21cd0a165695c756b6fda37016197b01e7), CoreKitAgent (945fcd3e08854a081c04c06eeb95ad6e0d9cdc19, a25c06e8545666d6d2a88c8da300cf3383149d5a), netchk variants and others.
- [Scripts] Observatory AppleScripts for initial payload delivery and data exfiltration – zoom_sdk_support.scpt (023a15ac687e2d2e187d03e9976a89ef5f6c1617), tlgrm (bb72ca0e19a95c48a9ee4fd658958a0ae2af44b6), upl (4743d5202dbe565721d75f7fb1eca43266a652d4)