The Russia-Ukraine war has fueled increased pro-Russian hacktivist campaigns involving DDoS attacks, data theft, and website defacements targeting European and allied nations. Key groups like NoName057(16), IT Army of Russia, and TwoNet lead politically motivated cyberattacks, sometimes with suspected ties to Russian state actors. #NoName05716 #ITArmyofRussia #TwoNet #CyberArmyofRussiaReborn
Keypoints
- Pro-Russian hacktivist groups have intensified cyberattacks since the 2022 Russia-Ukraine war, targeting government and critical infrastructure in NATO and European countries.
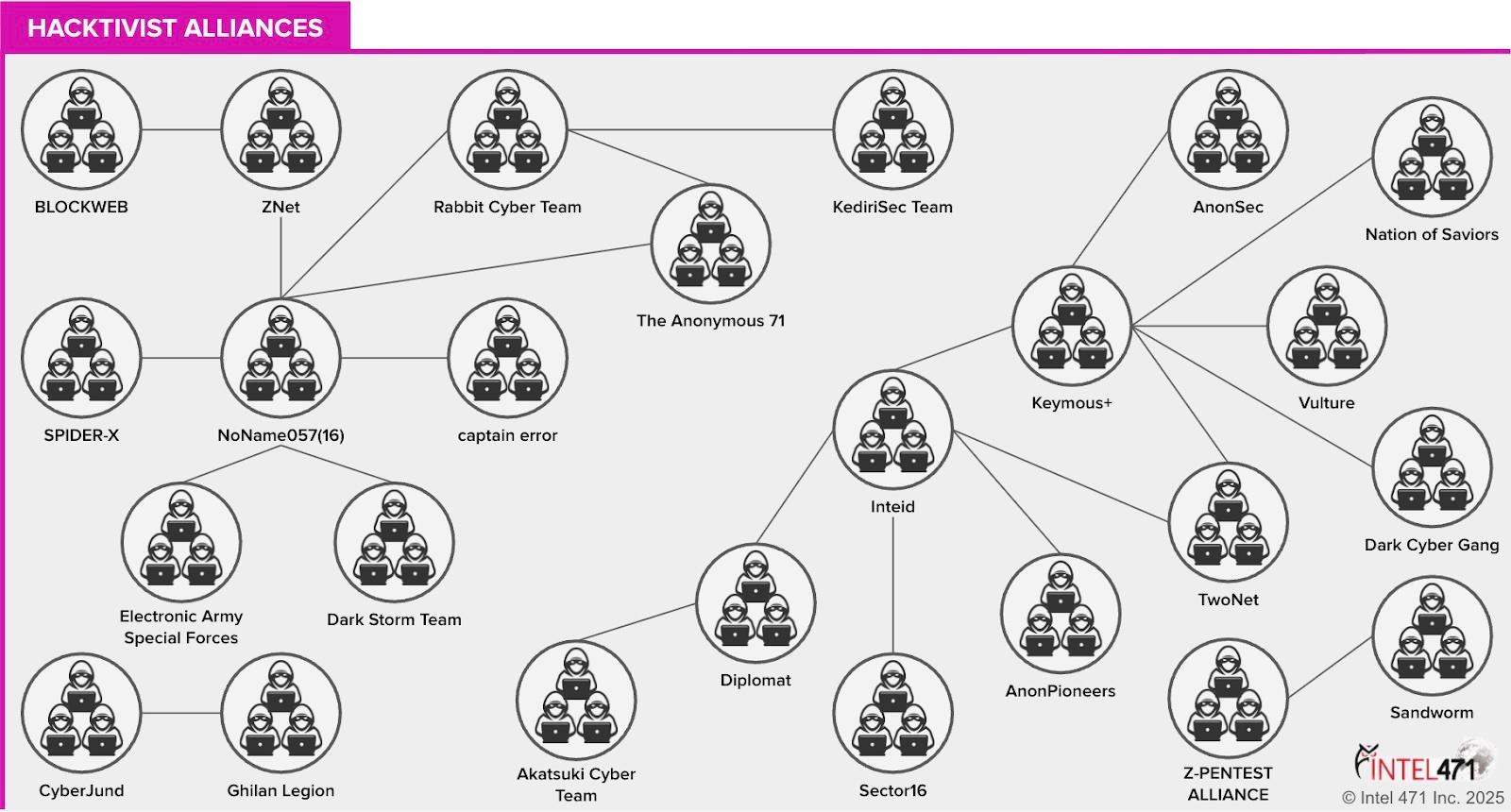
- NoName057(16) has become a leading pro-Russian hacktivist group, conducting frequent DDoS attacks and collaborating with other politically motivated groups.
- New groups such as IT Army of Russia and TwoNet emerged in 2025, using DDoS tools like PanicBotnet and MegaMedusa and recruiting insiders to support operations.
- The U.S. Treasury sanctioned prominent members of the Cyber Army of Russia Reborn (CARR) for attacks on U.S. critical infrastructure and potential ties to Russian GRU-affiliated groups.
- Some hacktivist attacks have escalated to targeting industrial control systems (ICS), causing operational disruptions, such as in a Texas water facility and an Arkansas water treatment plant.
- Evidence suggests possible Russian state support or direction of hacktivist groups to provide plausible deniability for cyber operations against Ukraine and Western allies.
- Hacktivist campaigns often tie attacks to current geopolitical events and use public channels like Telegram for coordination, propaganda, and recruitment.
MITRE Techniques
- [T1499] Endpoint Denial of Service – Groups conducted DDoS attacks against political and critical infrastructure targets. (“…DDoS attacks primarily against Ukrainian digital infrastructure…”)
- [T1071] Application Layer Protocol – Use of Telegram channels and bots for command, control, communication, and recruitment. (“…broadcasting operations via the Duty-Free underground forum and the t.me/itarmyofrussianews Telegram channel…”)
- [T1190] Exploit Public-Facing Application – Exploitation of SQL-injection (SQLi) vulnerabilities to steal data from Ukrainian targets. (“…The group often exploits structured query language-injection (SQLi) vulnerabilities to steal data and then leak those databases.”)
- [T1566] Phishing – Recruitment of insiders via Telegram and underground forums to obtain sensitive information. (“…The group also solicits insider information that could benefit Russian forces…”)
- [T0836] Data Manipulation – Tampering with Industrial Control Systems to disrupt water treatment and utility services. (“…claimed responsibility for causing the overflow of water storage tanks at a facility in Texas…”)
Indicators of Compromise
- [File Hashes] Pro-Russian hacktivist tools and DDoS utilities – PanicBotnet DDoS utility advertised by actor holynet, MegaMedusa Machine DDoS utility publicly available on GitHub.
- [Domains/Channels] Telegram channels used for communication and coordination – t.me/itarmyofrussianews, t.me/TwoNetOfficial (suspended), and t.me/DutyFreeForum.
- [File Names] Defacement targets – Lithuania-based freight company ExpressTrip targeted by NoName057(16) on July 4, 2022.
Read more: https://intel471.com/blog/pro-russian-hacktivism-shifting-alliances-new-groups-and-risks