A critical vulnerability (CVE-2025-3248) in Langflow is being actively exploited to deploy the Flodrix botnet, which enables attackers to perform DDoS attacks and exfiltrate sensitive data. The Flodrix malware uses sophisticated evasion techniques and is distributed through malicious Python payloads targeting vulnerable Langflow servers. #CVE20253248 #Flodrix
Category: Threat Research
Attackers have significantly increased the use of Windows shortcut (.lnk) files for malware distribution, with malicious samples rising from 21,098 in 2023 to 68,392 in 2024. This article categorizes LNK malware into four types and explains their mechanisms, emphasizing the importance of cautious handling of unknown LNK files. #LNKMalware #CVE-2010-2568 #PaloAltoNetworks…
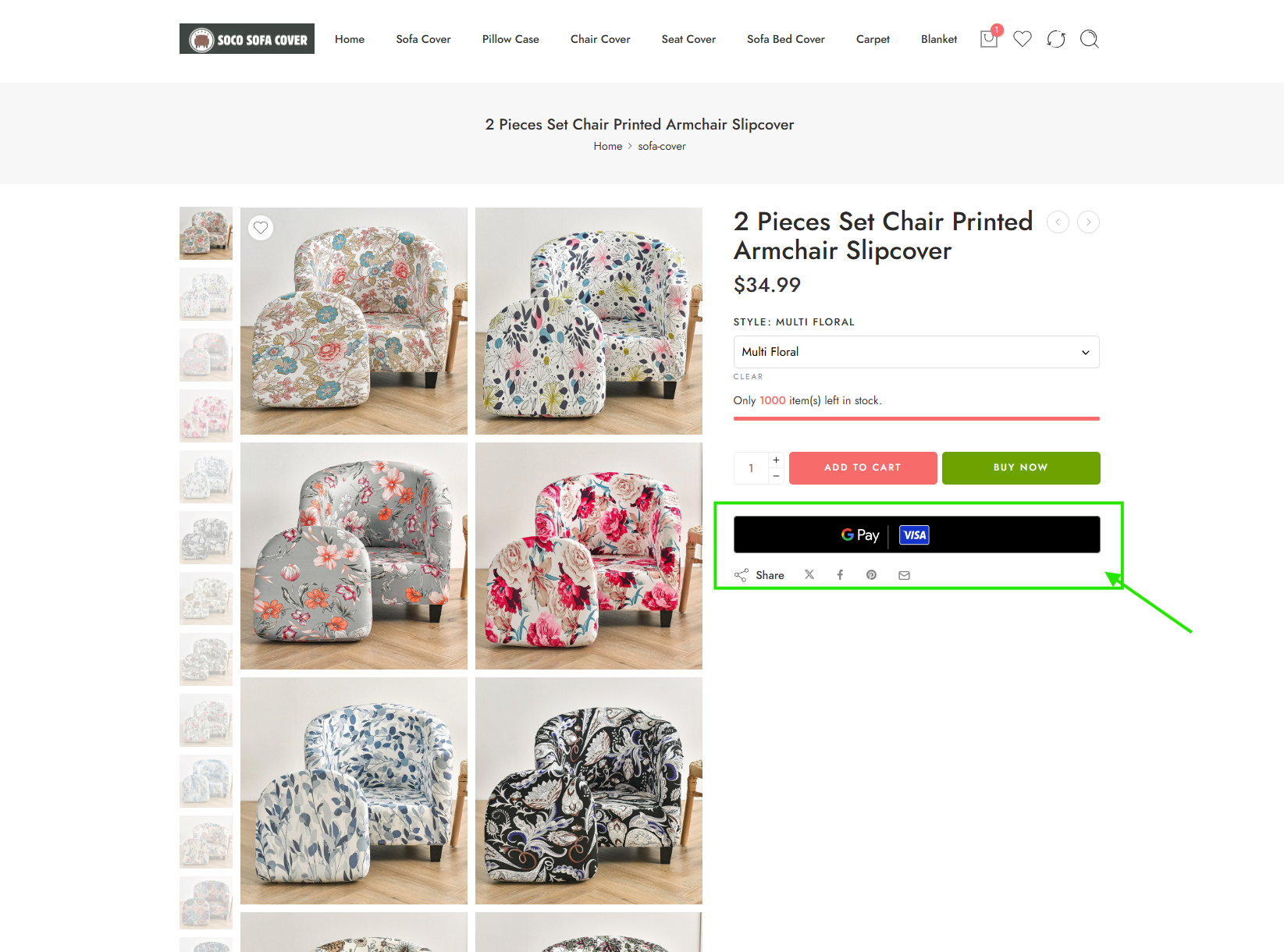
Silent Push Threat Analysts uncovered a large-scale Chinese-operated phishing campaign targeting global shoppers through thousands of fake marketplace websites spoofing major retail and payment brands. The campaign notably exploited the “Hot Sale 2025” event in Mexico and used advanced payment scams involving services like Google Pay to steal user financial information….
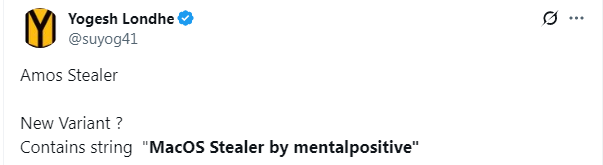
A new macOS stealer by MentalPositive has been identified targeting Ledger Live users in 2025, potentially representing a variant of the 2023 Atomic macOS Stealer (AMOS). This new malware exhibits similarities in credential and crypto wallet theft but uses different programming languages and introduces unique build IDs for campaign management. #MentalPositive #AMOS #LedgerLive

Since 2018, APT-C-36, known as Blind Eagle, has targeted Latin American organizations, especially in Colombia, using phishing campaigns and exploiting vulnerabilities like CVE-2024-43451. In a recent campaign detected by Darktrace in 2025, Blind Eagle used WebDAV-based payload delivery and dynamic DNS for command-and-control, leading to data exfiltration from a Colombian customer. #BlindEagle #APT-C-36 #CVE-2024-43451 #WebDAV #Remcos

Attackers are compromising poorly managed Linux servers by installing proxy tools TinyProxy and Sing-box using brute-force SSH access with weak credentials. These proxies enable attackers to misuse infected systems as proxy nodes for concealing harmful activities or generating profit. #TinyProxy #SingBox #LinuxServerAttacks…
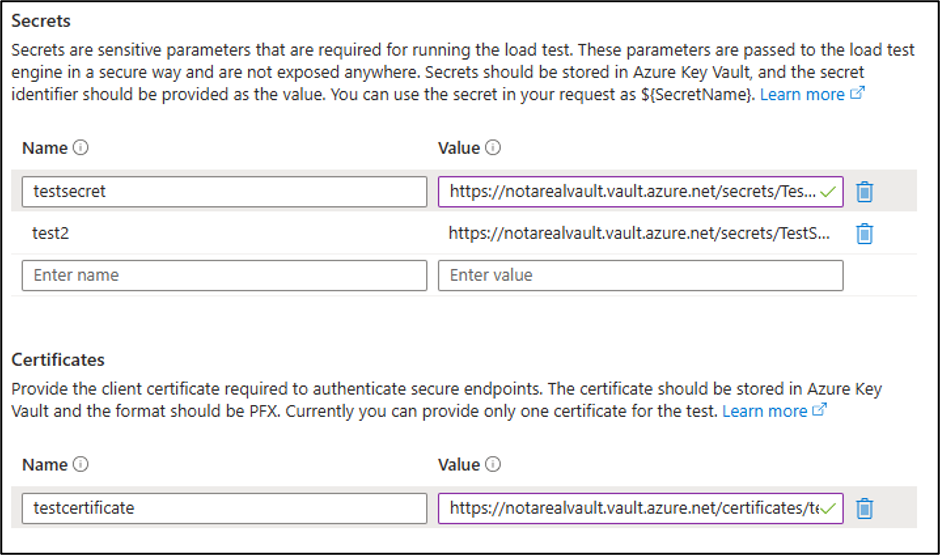
The Azure Load Testing service allows embedding of scripting code within JMeter (JMX) and Locust files, enabling attackers to execute commands, generate Managed Identity tokens, and extract secrets or certificates. Automated tools like MicroBurst can exploit these features to perform code execution, reverse shells, and secret extraction, highlighting detection opportunities through Azure Diagnostics Logs. #AzureLoadTesting #JMeter #ManagedIdentity #MicroBurst
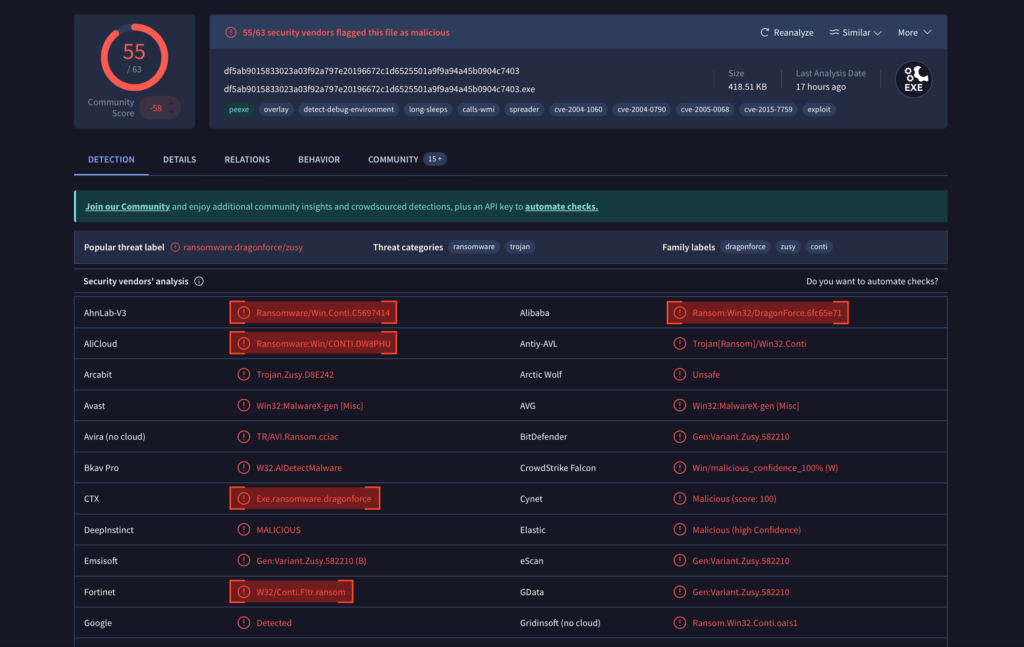
A new ransomware sample labeled as DragonForce or Conti exhibits unique traits linked to a threat actor named DEVMAN, indicating a hybrid built on DragonForce code but customized with distinct features. This sample demonstrates unusual behavior such as encrypting its own ransom notes and operates primarily offline with multiple encryption modes,…

A phishing campaign targeting Colombian organizations uses a Remote Access Trojan (DCRAT) distributed via obfuscated email attachments to gain control and steal sensitive data from infected Microsoft Windows systems. The attack chain employs multiple evasion techniques including steganography, base64 encoding, and multi-stage payload delivery to avoid detection. #DCRAT #ColombianGovernment #FortiMail
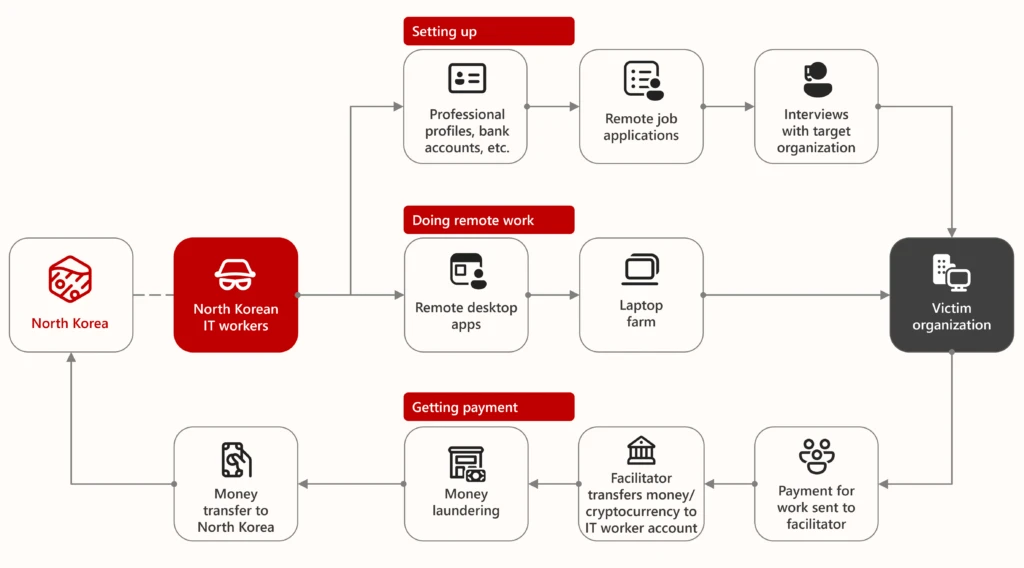
Since 2024, North Korean remote IT workers have been leveraging AI technologies like image manipulation and voice-changing software to enhance fraudulent employment operations worldwide. Microsoft tracks these activities under the codename Jasper Sleet and advises organizations to strengthen vetting and monitoring procedures to defend against this sophisticated insider threat. #JasperSleet #NorthKoreanITWorkers #Faceswap #AstrillVPN

Remcos malware campaigns have remained highly active, utilizing sophisticated techniques such as NT namespace path parsing to create spoofed Windows system directories and evade detection. The malware spreads mainly through phishing emails containing malicious shortcut files, enabling attackers to gain persistent control over infected systems. #Remcos #NTNamespace #PhishingEmails #Esentutl
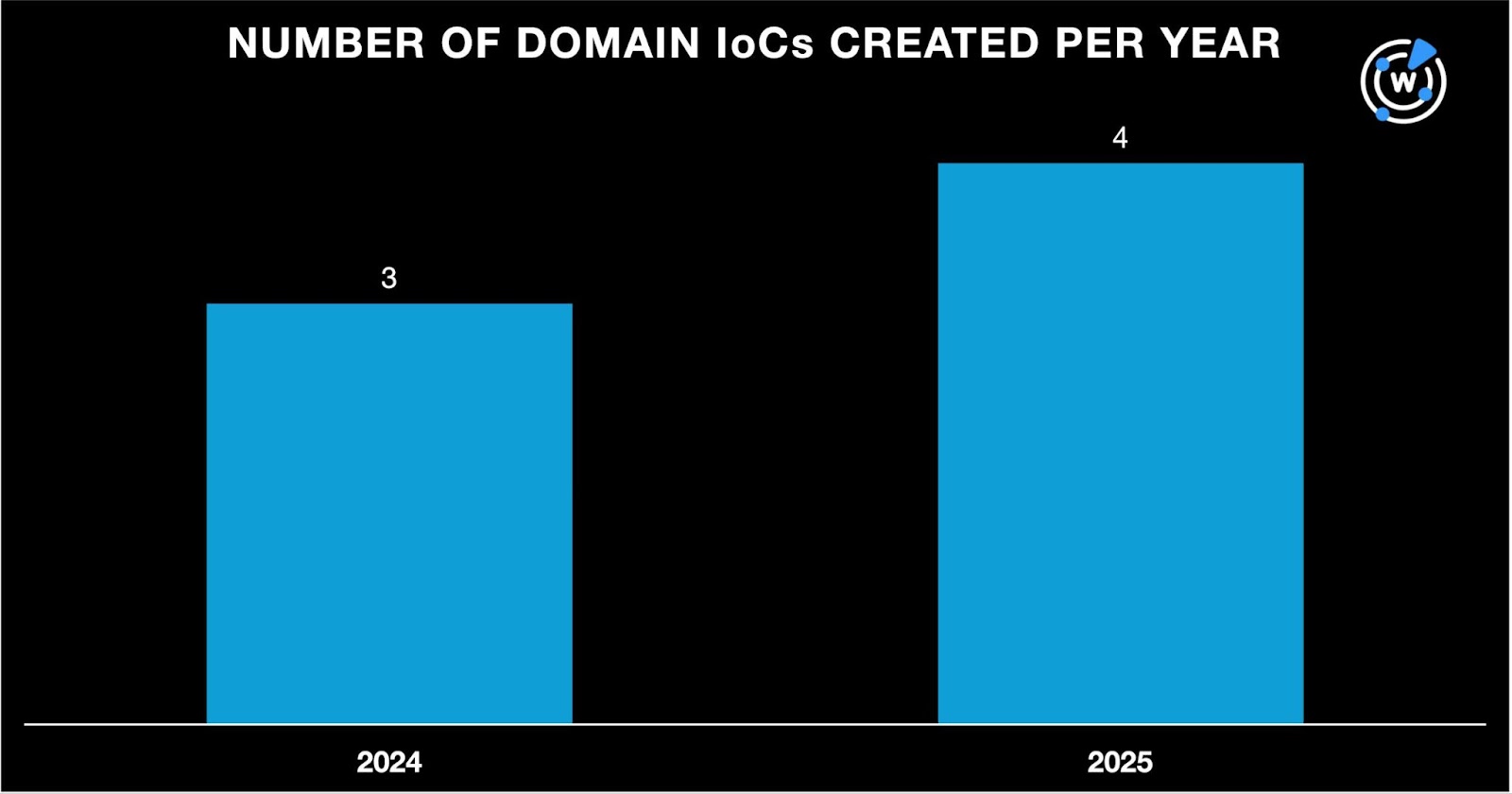
Cybercriminals hijacked Japanese securities accounts, leading to over 3,500 fraudulent stock transactions and losses exceeding ¥300 billion from January to April 2025. Through analysis of phishing-related domains and emails, researchers uncovered thousands of connected domains, including those weaponized for phishing attacks targeting stock owners. #JapaneseStockFraud #PhishingDomains

The Kimsuky group’s ClickFix tactic manipulates victims into executing malicious PowerShell commands via deceptive messages and phishing emails, often disguising itself as error notifications or security procedures. This threat has been employed by state-sponsored actors from North Korea, Iran, and Russia, emphasizing the need for robust EDR detection strategies against obfuscated malware and unusual behaviors. #ClickFix #Kimsuky #BabyShark
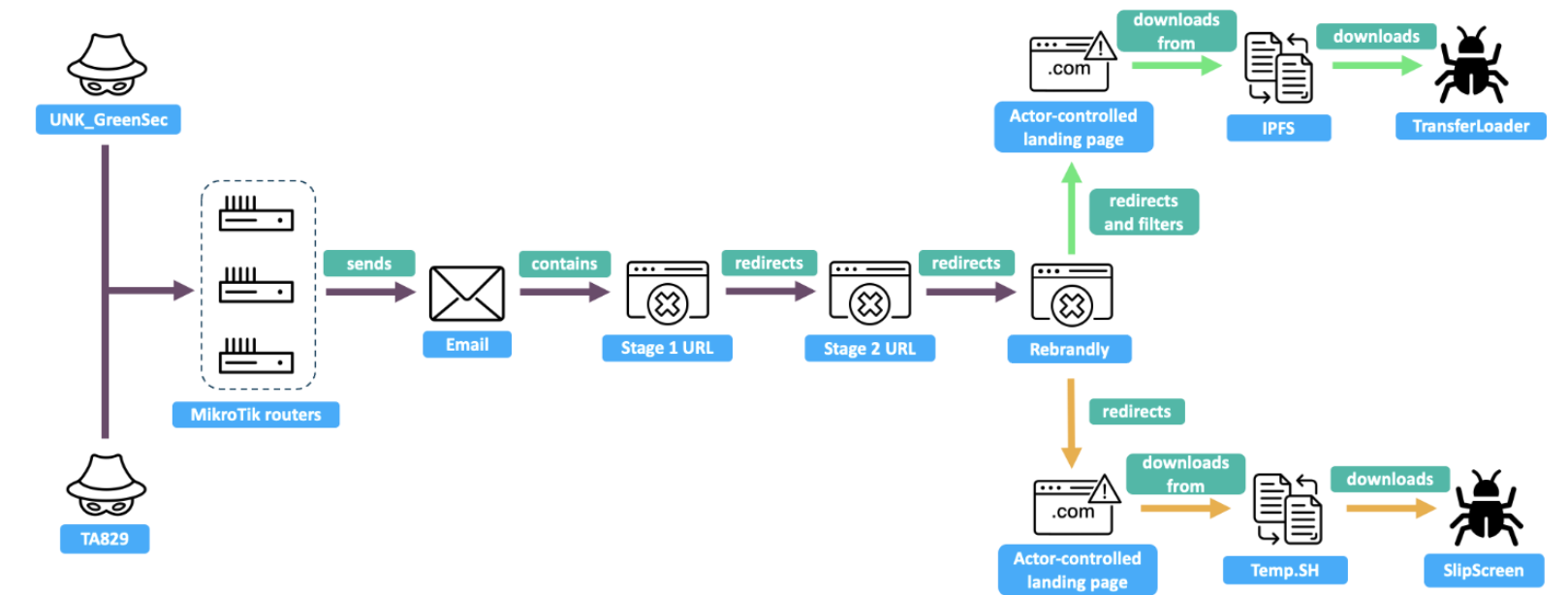
TA829 is a cybercriminal actor that also conducts espionage campaigns aligning with Russian state interests, utilizing custom malware like SingleCamper and DustyHammock. A separate cybercriminal cluster, UNK_GreenSec, operates a similar infrastructure and tactics deploying the TransferLoader malware, which has been observed delivering Morpheus ransomware. #TA829 #UNK_GreenSec #TransferLoader #SingleCamper #DustyHammock #MorpheusRansomware…
A threat actor conducted a multi-day intrusion starting with a password spray attack on an exposed RDP server, followed by credential harvesting using Mimikatz and Nirsoft tools, extensive network discovery, data exfiltration via Rclone over SFTP, and finally deploying RansomHub ransomware across the network using SMB and remote services. The incident featured lateral movement using legitimate tools like Atera and Splashtop for persistence and exhibited advanced evasion tactics including clearing shadow copies and event logs. #RansomHub #Mimikatz #Rclone #Atera #Splashtop #RDPPasswordSpray
