Silent Push Threat Analysts uncovered a large-scale Chinese-operated phishing campaign targeting global shoppers through thousands of fake marketplace websites spoofing major retail and payment brands. The campaign notably exploited the “Hot Sale 2025” event in Mexico and used advanced payment scams involving services like Google Pay to steal user financial information. #SilentPush #HotSale2025 #FakeMarketplace #PhishingCampaign #GooglePay
Keypoints
- A phishing scam campaign was initiated from a tip by Mexican journalist Ignacio Gómez Villaseñor regarding “Hot Sale 2025” targeting Spanish-language shoppers.
- The campaign expanded globally, targeting English and Spanish audiences with thousands of fake websites spoofing retailers like Apple, Michael Kors, and Wrangler Jeans.
- Technical indicators confirm the threat actor originates from China, using private infrastructure with Chinese language elements.
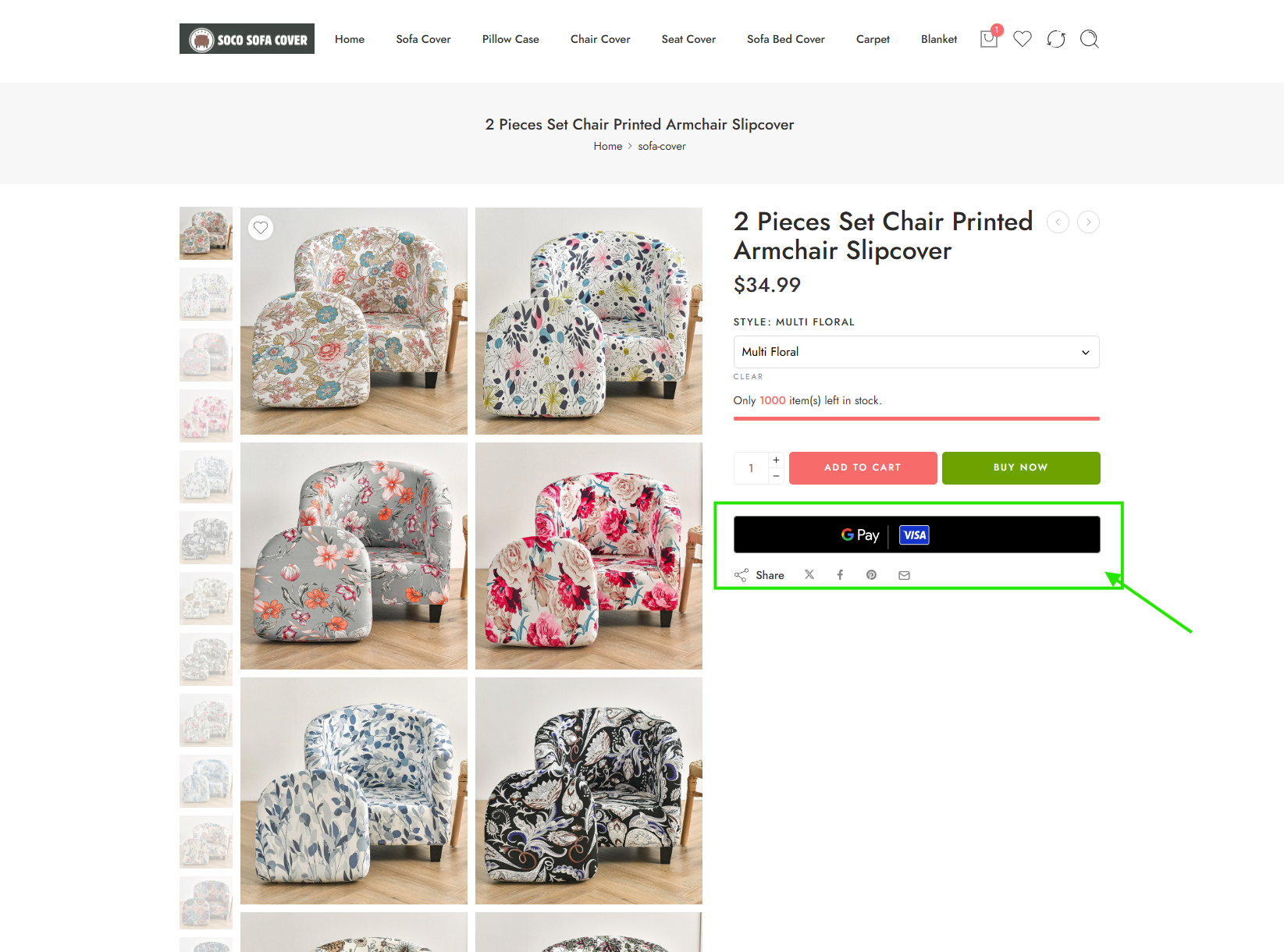
- The threat actor abused online payment services including PayPal, MasterCard, Visa, and Google Pay to collect sensitive payment data without delivering goods.
- Many phishing sites used genuine Google Pay purchase widgets to make scams appear legitimate and bypass virtual credit card protections.
- Numerous well-known brands were spoofed, with several fake sites blending multiple brand elements or using misspellings to deceive users.
- Although some fake domains have been taken down, thousands remain active, making traditional mitigation techniques insufficient.
MITRE Techniques
- [T1566] Phishing – The threat actor created phishing websites spoofing retail brands to deceive users and harvest payment data (“…multiple phishing websites with pages spoofing well-known retailers…”).
- [T1583] Acquire Infrastructure – Use of private technical infrastructure with Chinese language elements to host thousands of scam websites (“…private technical fingerprint associated with this infrastructure, which contains Chinese words…”).
- [T1565] Data Manipulation – Use of fake payment processing pages simulating payment flows to steal credit card information (“…entering false bank card data…the system reacts as if you were actually processing a payment…”).
- [T1587] Develop Capabilities – Deployment of Google Pay widgets to facilitate payment scams circumventing virtual card protections (“…sites using Google Pay…threat actor group is also stealing payments…”).
Indicators of Compromise
- [Domain] Fake phishing websites associated with the campaign – harborfrieght[.]shop, rizzingupcart[.]com, guitarcentersale[.]com, brooksbrothersofficial[.]com, and others.
- [Domain] Spoofing well-known retailer domains with typographical errors or brand impersonations – nordstromltems[.]com, josbankofficial[.]com, tommyilfigershop[.]com.