The Azure Load Testing service allows embedding of scripting code within JMeter (JMX) and Locust files, enabling attackers to execute commands, generate Managed Identity tokens, and extract secrets or certificates. Automated tools like MicroBurst can exploit these features to perform code execution, reverse shells, and secret extraction, highlighting detection opportunities through Azure Diagnostics Logs. #AzureLoadTesting #JMeter #ManagedIdentity #MicroBurst
Keypoints
- Azure Load Testing supports JMeter (JMX) and Locust files which can execute embedded scripting code, such as Groovy or Python, within the testing environment.
- Attackers can use JSR223Sampler elements in JMX files to execute arbitrary commands, including reverse shells, by injecting code into test plans.
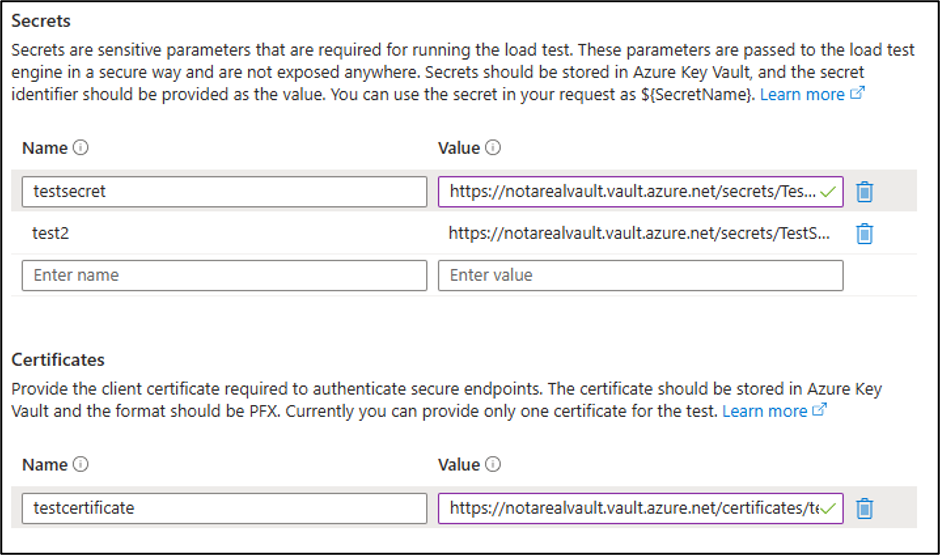
- The service uses Managed Identities to access Key Vault secrets and certificates, which can be accessed and extracted when code execution is achieved.
- Automated exploitation is possible via MicroBurst PowerShell tooling that enumerates Load Testing resources, scrapes secrets and certificates, runs malicious tests, and extracts sensitive data.
- Detection and hunting can be implemented by monitoring Azure Diagnostics Logs for unusual test enumeration, creation, execution, and deletion activities involving suspicious test names like “microburst”.
- Activity Logs are insufficient for detection, thus enabling diagnostic logging is essential to capturing malicious behaviors within the Load Testing service.
- The vulnerability was responsibly reported to Microsoft Security Response Center (MSRC), resulting in improvements but no immediate threat classification.
MITRE Techniques
- [T1059] Command and Scripting Interpreter – Attackers use scripting languages like Groovy embedded in JMeter JMX files to execute system commands (‘”whoami”.execute()’) and reverse shells within the Azure Load Testing environment.
- [T1078] Valid Accounts – Abuse of Managed Identities supported by the service to access Key Vault secrets and certificates for authentication data extraction.
- [T1218] Signed Binary Proxy Execution – Use of legitimate commands and scripts within Azure Load Testing to perform malicious activities such as HTTP requests containing encoded command outputs.
Indicators of Compromise
- [File Names] Malicious JMX test files – Examples include “microburst.jmx” used for code execution and data extraction.
- [Operation Names] Azure diagnostic log activities – Operations such as MICROSOFT.LOADTESTSERVICE/LOADTESTS/WRITETEST/ACTION with PATCH and PUT requests involving “microburst” test names indicate malicious actions.
- [URLs] External callback endpoints – Example: HTTPS servers specified in injected Groovy scripts for exfiltration (e.g., https://YOUR_SITE_HERE/).