Attackers have significantly increased the use of Windows shortcut (.lnk) files for malware distribution, with malicious samples rising from 21,098 in 2023 to 68,392 in 2024. This article categorizes LNK malware into four types and explains their mechanisms, emphasizing the importance of cautious handling of unknown LNK files. #LNKMalware #CVE-2010-2568 #PaloAltoNetworks
Keypoints
- Malicious Windows shortcut (.lnk) files have surged in 2024, with 68,392 detected samples compared to 21,098 in 2023.
- LNK malware is classified into four categories: exploit execution, malicious file execution, in-argument script execution, and overlay content execution.
- LNK files abuse the Target, LINKTARGET_IDLIST, RELATIVE_PATH, and COMMAND_LINE_ARGUMENTS fields to execute malicious payloads or scripts.
- CVE-2010-2568 remains a common vulnerability exploited by LNK file variants for system compromise.
- Common system targets for LNK malware include powershell.exe, cmd.exe, rundll32.exe, conhost.exe, wscript.exe, forfiles.exe, and mshta.exe.
- Overlay content execution techniques include using find/findstr commands, mshta for HTA payloads, and PowerShell commands to decode and execute embedded content.
- Palo Alto Networks offers protection through Next-Generation Firewall, Prisma Access, Advanced Threat Prevention, Cortex XDR, and XSIAM against these LNK-based threats.
MITRE Techniques
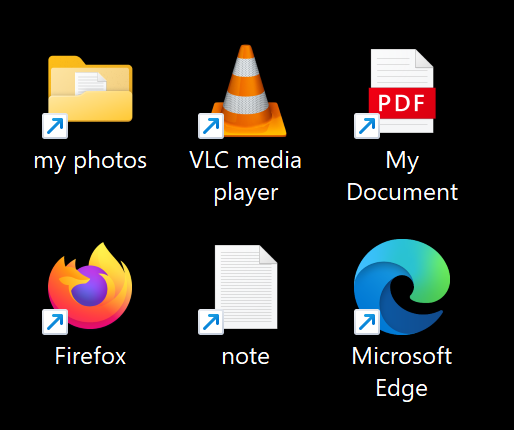
- [T1204] User Execution – Malicious LNK files trick users into executing malware by masquerading as legitimate files (“LNK malware files can have familiar icons or names that mimic trusted applications or documents to trick users into opening them”).
- [T1059] Command and Scripting Interpreter – Attackers use cmd.exe, powershell.exe, and mshta.exe to run malicious scripts embedded in LNK files (“PowerShell commands and intrinsics such as Select-String, Get-Content and .Substring can be used to find or extract content”).
- [T1064] Scripting – Malicious scripts are embedded within LNK files’ COMMAND_LINE_ARGUMENTS or appended as overlay content (“COMMAND_LINE_ARGUMENTS field can contain strings of any size, including a malicious script”).
- [T1106] Execution through API – LNK files execute targets using command-line arguments to launch malicious payloads (“attackers can also use command-line arguments to download and execute malicious code”).
- [T1202] Indirect Command Execution – Using system tools like wscript.exe, rundll32.exe, and forfiles.exe to indirectly execute malicious files (“LNK malware files often trigger malicious scripts or other files that cannot be directly executed”).
- [T1036] Masquerading – LNK files use icons and file naming to disguise malware (“LNK malware files can have familiar icons or names that mimic trusted applications or documents”).
- [T1086] PowerShell – Base64-encoded and obfuscated PowerShell scripts delivered via LNK files (“The full string for the malicious PowerShell script is Base64-encoded”).
- [T1203] Exploitation for Client Execution – Exploit-based LNK malware targets CVE-2010-2568 using corrupt LNK binaries to crash or leverage vulnerable Windows components (“the most common vulnerability targeted is CVE-2010-2568”).
Indicators of Compromise
- [File Hashes] SHA256 hashes of LNK malware samples – a90c87c90e046e68550f9a21eae3cad25f461e9e9f16a8991e2c7a70a3a59156, 08233322eef803317e761c7d380d41fcd1e887d46f99aae5f71a7a590f472205, and 9d4683a65be134afe71f49dbd798a0a4583fe90cf4b440d81eebcbbfc05ca1cd among others.
- [Domains] Malicious domain used in overlay content – pdf-online[.]top referenced for downloading malicious content.
- [File Names] Example malicious files executed by LNK – desktop.ini.exe (malicious executable), Video.3gp (encoded VBS script), and embedded HTA scripts.