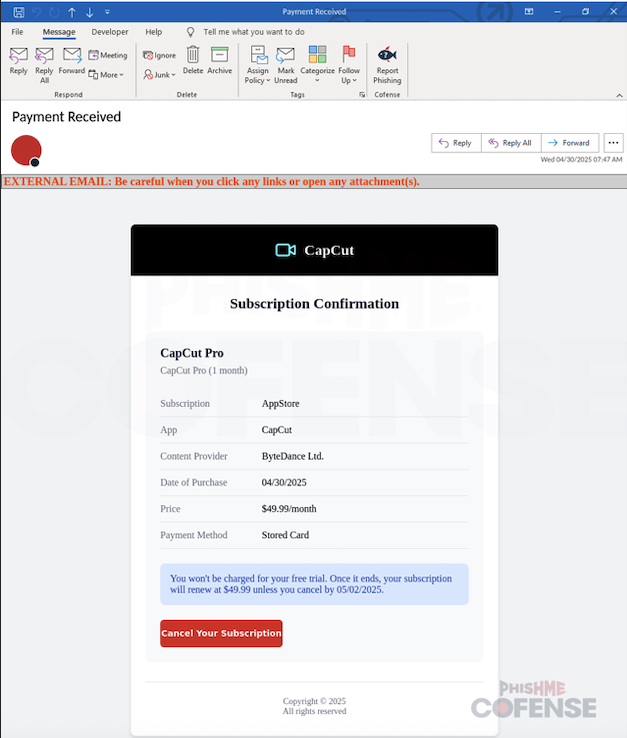
Cybercriminals are exploiting CapCut’s popularity through a phishing campaign that uses fake invoice emails to steal Apple ID credentials and credit card information. The attack involves a two-stage process with convincing fake login pages and a deceptive refund request to trick victims. #CapCutPhishing #Flashersofts.store
Keypoints
- A phishing campaign impersonates CapCut invoices to harvest Apple ID and credit card data.
- Attackers use a fake Apple ID login page hosted on an unrelated domain “flashersofts.store”.
- Stolen credentials are sent via HTTP POST requests to server IP 104.21.33.45.
- The phishing scam involves a two-step process: first stealing login credentials, then requesting card information under the guise of a refund.
- Input validation is used on the credit card form to ensure data accuracy and increase victim trust.
- A fake authentication code prompt is used at the end to delay suspicion and prevent reporting by victims.
- The phishing emails contain infection URLs hosted on domains like ynotmail.io and payload URLs on flashersofts.store.
MITRE Techniques
- [T1566] Phishing – Use of fake CapCut invoice emails to lure victims into entering credentials. (“… crafted convincing fake CapCut invoice lures …”)
- [T1056.001] Input Capture: Keylogging – A fake Apple ID login page captures user credentials via HTTP POST requests. (“… credentials … sent via an HTTP POST request to 104.21.33.45 …”)
- [T1204.002] User Execution: Malicious File – Users click “Cancel your subscription” button leading to phishing websites. (“… will open a webpage in their default browser.”)
- [T1539] Steal Web Session Cookie – Use of input validation on credit card forms to gather accurate financial data. (“… input box not recognizing anything less than a standard amount of card number digits …”)
- [T1566.002] Spearphishing Link – Attack involves links in emails redirecting users to faux login pages. (“… phishing scheme … infection URL: hXXps://yms1.ynotmail.io/…”)
Indicators of Compromise
- [Domain] phishing and payload hosting domains – flashersofts.store, ynotmail.io
- [IP Address] command and control and payload servers – 104.21.33.45, 172.67.141.41, 104.21.33.43
- [URL] infection and payload URLs – hXXps://yms1.ynotmail.io/clients/link.php?M=703770538&N=3194361&L=453538585&F=H99.192.255.26, hXXps://flashersofts.store/Applys/project/index.php
Read more: https://cofense.com/blog/capcut-con-apple-phishing-card-stealing-refund-ruse