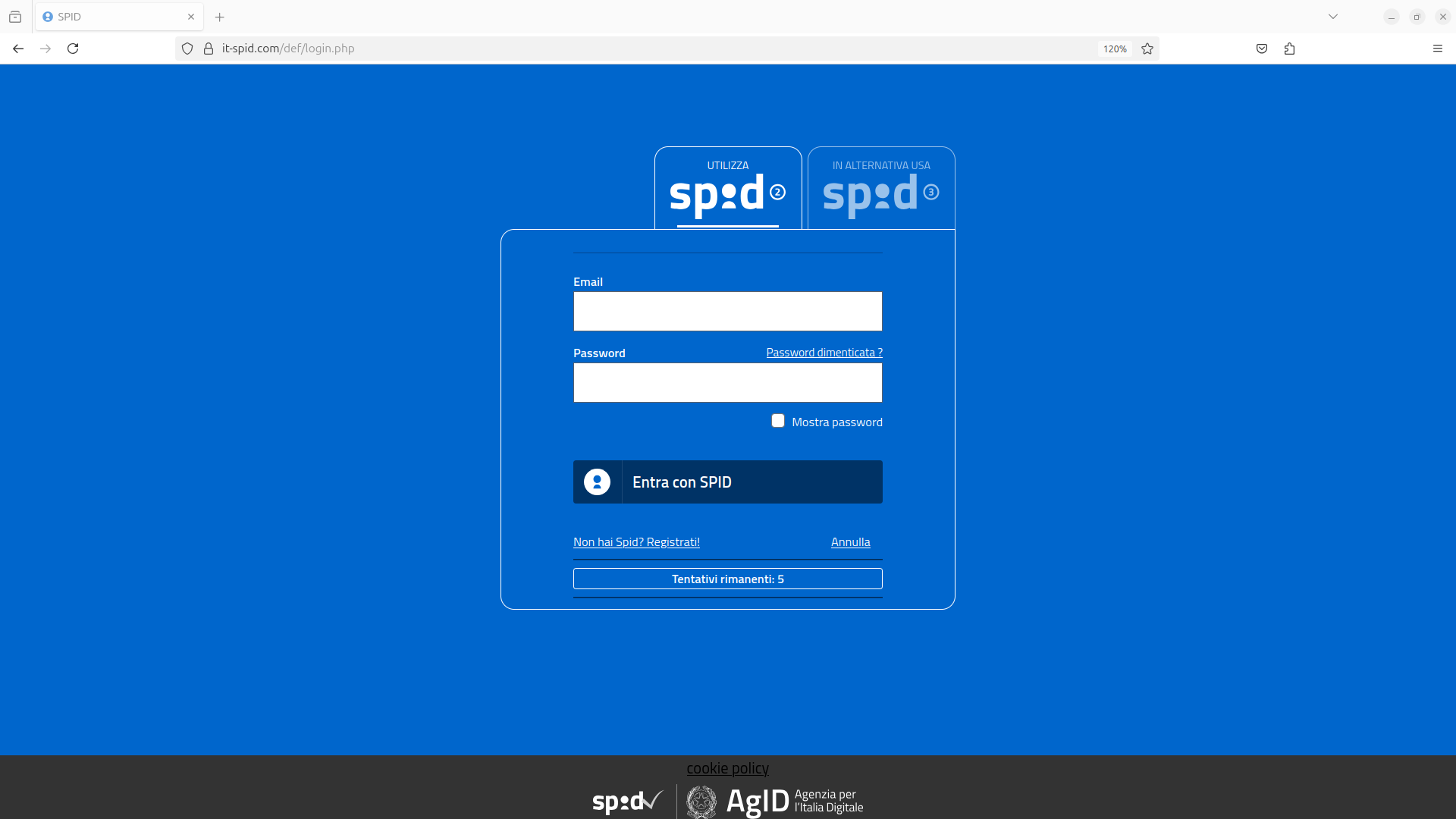
CERT-AGID identified a phishing campaign targeting SPID users, impersonating AgID to steal login credentials and identity documents via fraudulent emails. The attackers also request victims to record videos for identity verification on a malicious website hosted on the domain it-spid[.]com. #SPID #AgID #CERTAGID
Keypoints
- CERT-AGID detected a phishing campaign using AgID’s name and logo to target SPID users.
- Phishing emails prompt users to update their documentation by accessing a malicious website.
- The attackers steal SPID credentials and copies of victims’ identity documents.
- Victims are also asked to record videos following specific instructions to simulate identity verification.
- The malicious pages are hosted on the recently registered domain it-spid[.]com, unrelated to SPID.
- The campaign resembles previous SPID and INPS phishing attempts aimed at document theft.
- AgID requested takedown of the domain and shared IoCs through the CERT-AGID feed to prevent further data theft.
MITRE Techniques
- [T1566] Phishing – The campaign uses fraudulent emails impersonating AgID to lure victims to malicious sites (“phishing campaign targeting SPID users with fraudulent emails”).
- [T1204] User Execution – Victims are instructed to perform actions such as video recording as part of the scam (“requested to record a video following specific instructions for verification”).
- [T1078] Valid Accounts – Attackers steal SPID credentials to gain unauthorized access (“steal SPID credentials and identity documents”).
Indicators of Compromise
- [Domain] Malicious hosting domain – it-spid[.]com used to host phishing pages impersonating SPID system.
- [Email Addresses] Report suspicious emails to – [email protected] for analysis and mitigation.
Read more: https://cert-agid.gov.it/news/in-corso-una-nuova-campagna-di-phishing-a-tema-spid/