The Socket Threat Research Team uncovered an ongoing North Korean supply chain attack using typosquatted npm packages to distribute multi-stage malware including HexEval Loader, BeaverTail, and InvisibleFerret. The threat actors use social engineering on LinkedIn to lure developers into executing malicious code, enabling persistent infostealing and keylogging capabilities. #ContagiousInterview #HexEval #BeaverTail #InvisibleFerret
Keypoints
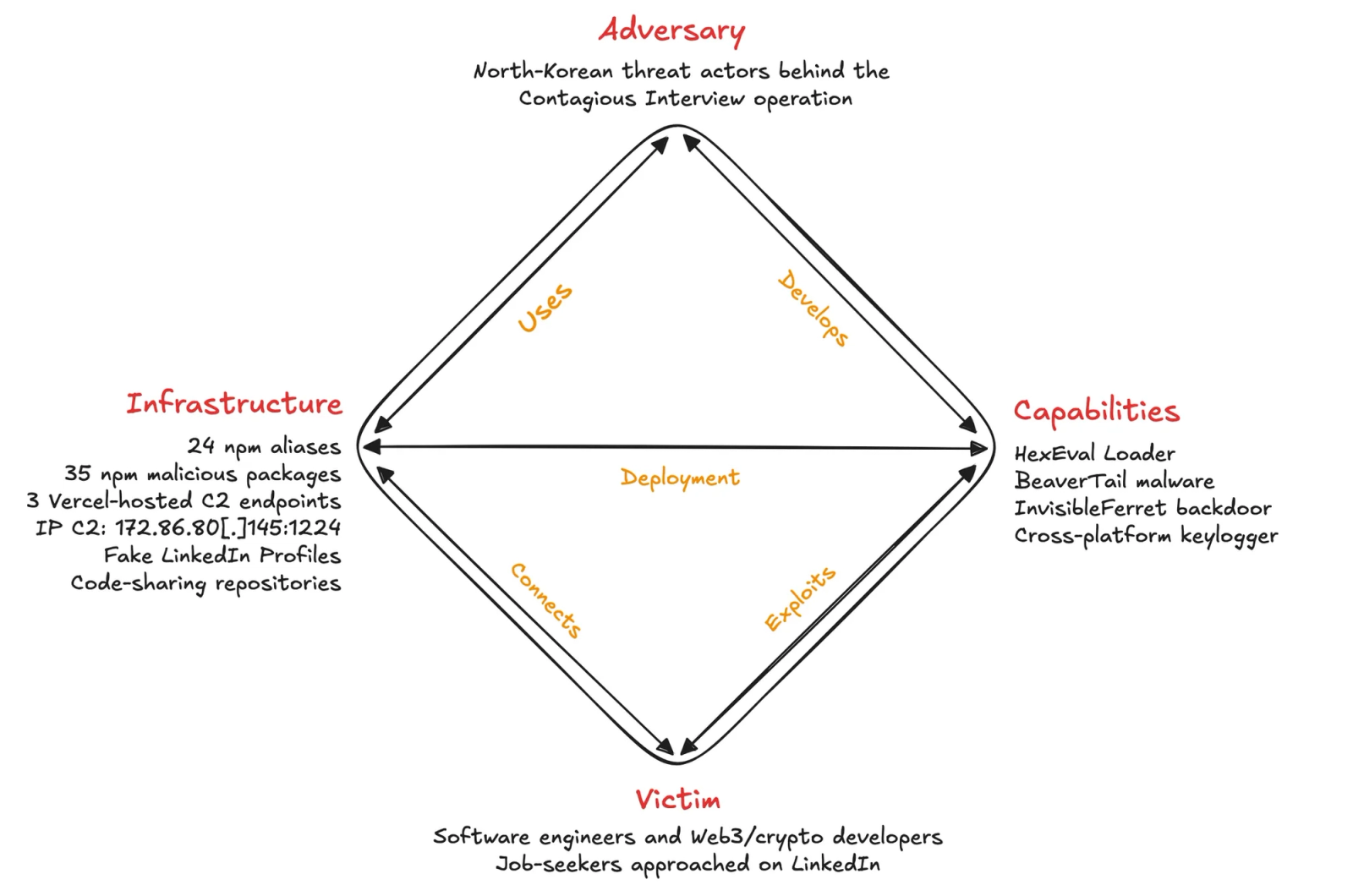
- The North Korean Contagious Interview operation published 35 malicious npm packages under 24 accounts, with 6 still live and downloaded over 4,000 times.
- Each package includes HexEval Loader, a hex-encoded loader that collects host metadata and retrieves the BeaverTail infostealer and InvisibleFerret backdoor as follow-on stages.
- Threat actors pose as LinkedIn recruiters, sending fake coding assignments that embed these malicious npm packages and pressuring victims to run code outside container environments.
- BeaverTail malware steals browser data, cryptocurrency wallets, and loads the InvisibleFerret backdoor, enabling layered control and data exfiltration.
- A cross-platform keylogger named jsonsecs was found, capable of capturing keystrokes on Windows, macOS, and Linux systems via native binaries.
- The supply chain attack leverages typosquatting on popular npm package names and encodes C2 URLs to evade detection.
- Several C2 endpoints on vercel.app and an IP address 172[.]86[.]80[.]145 were identified delivering payloads conditionally based on the victim’s environment.
MITRE Techniques
- [T1195.002] Supply Chain Compromise – Compromising npm packages to deliver malware. “The Socket Threat Research Team has uncovered an extended North Korean supply chain attack that hides behind typosquatted npm packages.”
- [T1608.001] Stage Capabilities: Upload Malware – Deploying multi-stage payloads including BeaverTail and InvisibleFerret. “‘BeaverTail malware… designed for targeted data theft and persistent access.’”
- [T1204.002] User Execution: Malicious File – Victims pressured to run malicious code from fake job assignments on LinkedIn. “‘The threat actors send coding “assignments”… pressure candidates to run the code outside containerized environments while screen-sharing.’”
- [T1059.007] Command and Scripting Interpreter: JavaScript – Use of eval() to execute decoded scripts. “‘Then execute it by calling eval().’”
- [T1027.013] Obfuscated Files or Information: Encrypted/Encoded File – HexEval Loader uses hex-encoded strings for module names and URLs. “‘To evade static analysis, the threat actors encode module names and C2 URLs as hexadecimal strings.’”
- [T1546.016] Event Triggered Execution: Installer Packages – Malicious npm packages run during installation. “‘Each malicious package contains a hex-encoded loader we call HexEval. When the package installs… fetches and runs BeaverTail.’”
- [T1005] Data from Local System – BeaverTail searches local files for browser and wallet data. “‘BeaverTail scans local file systems for browser artifacts… cryptocurrency wallets… and macOS keychain databases.’”
- [T1082] System Information Discovery – HexEval collects host metadata such as platform, hostname, username, and MAC address. “‘HexEval Loader collects host metadata… platform: os.platform(), hostname: os.hostname().’”
- [T1083] File and Directory Discovery – BeaverTail enumerates files under approximately 200 profile directories. “‘BeaverTail scans local file systems across approximately 200 profile directories.’”
- [T1217] Browser Information Discovery – Targeting cookies, IndexedDB, extensions from browsers like Brave, Chrome, and Opera. “‘It searches for cookies, IndexedDB files, and extensions…’”
- [T1555.003] Credentials from Password Stores: Credentials from Web Browsers – Extracts browser credentials. “‘Targeting credentials from web browsers and their extensions.’”
- [T1555.001] Credentials from Password Stores: Keychain – Extracts macOS keychain data. “‘…macOS keychain databases.’”
- [T1056.001] Input Capture: Keylogging – jsonsecs package implements keystroke capture on multiple platforms. “‘A cross-platform keylogger package that captures every keystroke.’”
- [T1041] Exfiltration Over C2 Channel – Malware communicates with C2 servers via HTTPS POST requests to exfiltrate data. “‘Module issues an HTTPS POST request to its C2 server… evaluates returned code.’”
- [T1105] Ingress Tool Transfer – Downloading additional payloads like InvisibleFerret. “‘BeaverTail downloads additional payloads… which are extracted.’”
- [T1119] Automated Collection – Automated collection of host system data including environment variables and system info. “‘Collects environment variables, platform, hostname, username, and MAC address.’”
- [T1657] Financial Theft – Targeting cryptocurrency wallet files for theft. “‘BeaverTail also targets cryptocurrency wallets, attempting to extract files like Solana’s id.json, Exodus wallet data.’”
Indicators of Compromise
- [Malicious npm Packages] 35 packages including react-plaid-sdk, sumsub-node-websdk, vite-plugin-next-refresh, node-orm-mongoose, router-parse, and jsonsecs.
- [Threat Actor npm Aliases] liamnevin, loveryon, jtgleason, pablomendes, supercrazybug, alexander0110819, and others involved in publishing malicious packages.
- [Email Addresses] Used for fake recruiter personas such as maria.sam.recruiter@gmail[.]com, toptalent0921@gmail[.]com, business00747@gmail[.]com.
- [Malicious Bitbucket Repositories] hxxps://bitbucket[.]org/notion-dex/ultrax, hxxps://bitbucket[.]org/zoro-workspace/.
- [Command and Control Endpoints] hxxps://log-server-lovat[.]vercel[.]app/api/ipcheck/703, hxxps://ip-check-server[.]vercel[.]app/api/ip-check/208, hxxps://ip-check-api[.]vercel[.]app/api/ipcheck/703, and IP 172[.]86[.]80[.]145:1224.
- [SHA256 File Hashes] WinKeyServer: e58864cc22cd8ec17ae35dd810455d604aadab7c3f145b6c53b3c261855a4bb1, MacKeyServer: 30043996a56d0f6ad4ddb4186bd09ffc1050dcc352f641ce3907d35174086e15, X11KeyServer: 6e09249262d9a605180dfbd0939379bbf9f37db076980d6ffda98d650f70a16d.