The Arctic Wolf Labs team discovered that the cyber-espionage group UAC-0226 significantly upgraded its infostealer malware GIFTEDCROOK from basic browser data theft to advanced intelligence gathering targeting Ukrainian governmental and military institutions. The malware uses spear-phishing with military-themed PDFs to exfiltrate sensitive data via Telegram, aligned with key geopolitical events. #GIFTEDCROOK #UAC0226 #CERTUA
Keypoints
- GIFTEDCROOK evolved through three versions (v1, v1.2, v1.3) from browser data theft to extensive document and credential exfiltration.
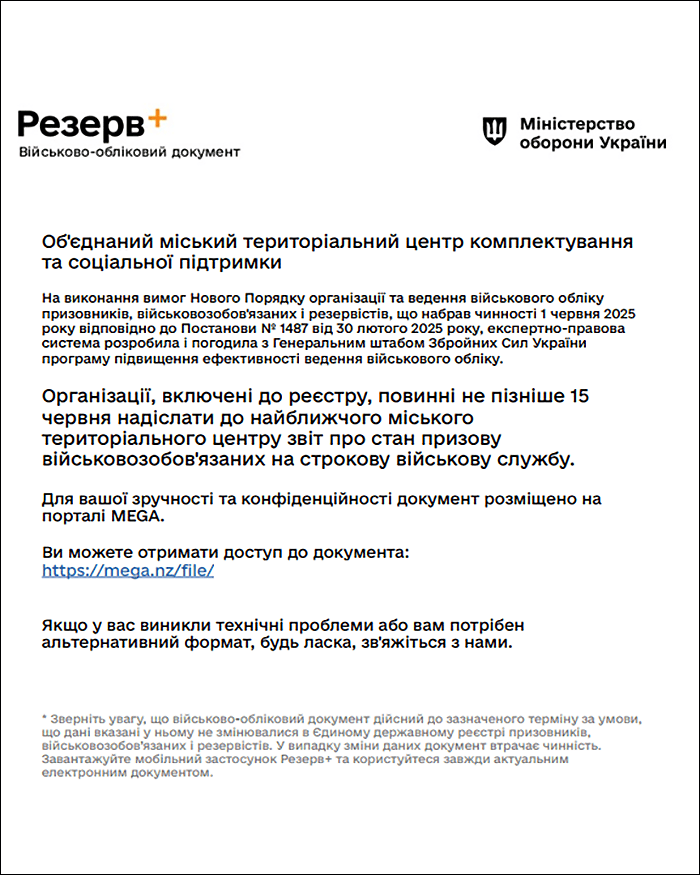
- The primary infection vector is spear-phishing emails with military-themed PDF lures targeting Ukrainian governmental and military entities.
- Exfiltrated data is sent to Telegram bot channels, leveraging encrypted zip archives uploaded in parts if exceeding 20 MB.
- Phishing email headers showed weak SPF settings and use of decoy recipients to conceal true targets within Ukraine.
- Infrastructure overlap revealed multi-group operations targeting Ukraine with related malware like NetSupport RAT.
- GIFTEDCROOK v1.3 extended file search to documents modified within 45 days and collects browser secrets from multiple browsers.
- Detection and remediation focus on monitoring specific file paths, Telegram API communications, and spear-phishing awareness.
MITRE Techniques
- [T1566] Phishing – Delivered malware via spear-phishing emails with military-themed PDF lures exploiting social engineering tactics (“…spammer’s preference for spoofing locations…”)
- [T1204.002] User Execution: Malicious File – Victims are tricked into enabling macros in documents, enabling execution of embedded malware (“…user manually enables macros…”)
- [T1056] Input Capture – Stealing browser secrets including cookies and login data from Chrome, Edge, and Firefox (“…extracts browser secrets, including cookies and login data…”)
- [T1039] Data from Network Shared Drive – Collection and exfiltration of documents and files by file extension and modification dates (“…targets specific file types…files created or modified within the last 45 days…”)
- [T1105] Ingress Tool Transfer – Downloads malware payloads via Mega.nz legitimate cloud storage (“…weaponized link to a Mega[.]nz-hosted file…”)
- [T1071.001] Application Layer Protocol: Web Protocols – Data exfiltration performed through Telegram bot API (“…dispatched to a dedicated Telegram channel…”)
- [T1083] File and Directory Discovery – Malware searches local directories and organizes files into subdirectories mimicking original locations (“…copies files into new directory, organizing into subdirectories…”)
- [T1070] Indicator Removal on Host – Use of batch script to auto-delete malware traces post-exfiltration (“…The Infomaster_delete.bat file… functioning as an auto-eraser…”)
Indicators of Compromise
- [SHA-256 Hashes] Multiple malicious files including GIFTEDCROOK v1.2 and v1.3 samples – a6dd44c4b7a9785525e7f487c064995dc5f33522dad8252d8637f6a6deef3013, b9d508d12d2b758091fb596fa8b8b4a1c638b7b8c11e08a1058d49673f93147d, and others
- [Domains] Mega.nz links used for hosting malicious files – weaponized PDF links to files on Mega;
- [URLs] Telegram API endpoints used for data exfiltration – hxxps://api.telegram.org/bot7806388607:AAFb6nCE21n6YmK6-bJA6IrcLTLfhlwQ254/sendDocument, hxxps://api.telegram.org/bot7726014631:AAFe9jhCMsSZ2bL7ck35PP30TwN6Gc3nzG8/sendDocument
- [File Paths] Malware installation and temporary files – %ProgramData%InfomasterInfomaster, %ProgramData%PhoneInfoPhoneInfo, C:Users%Username%AppDataLocalTemp[a-zA-Z0-9]{13}[a-zA-Z0-9]{13}