The Iranian APT group Educated Manticore has intensified spear-phishing attacks targeting Israeli journalists, cybersecurity experts, and academics using sophisticated phishing kits disguised as legitimate Google authentication pages. Their campaigns employ multi-stage tactics, including fake Google Meet invitations and dynamic React-based phishing infrastructure, to harvest credentials and 2FA codes, enabling cyber-espionage aligned with Iran-Israel tensions. #EducatedManticore #IranIsraelConflict #GooglePhishingKit
Category: Threat Research
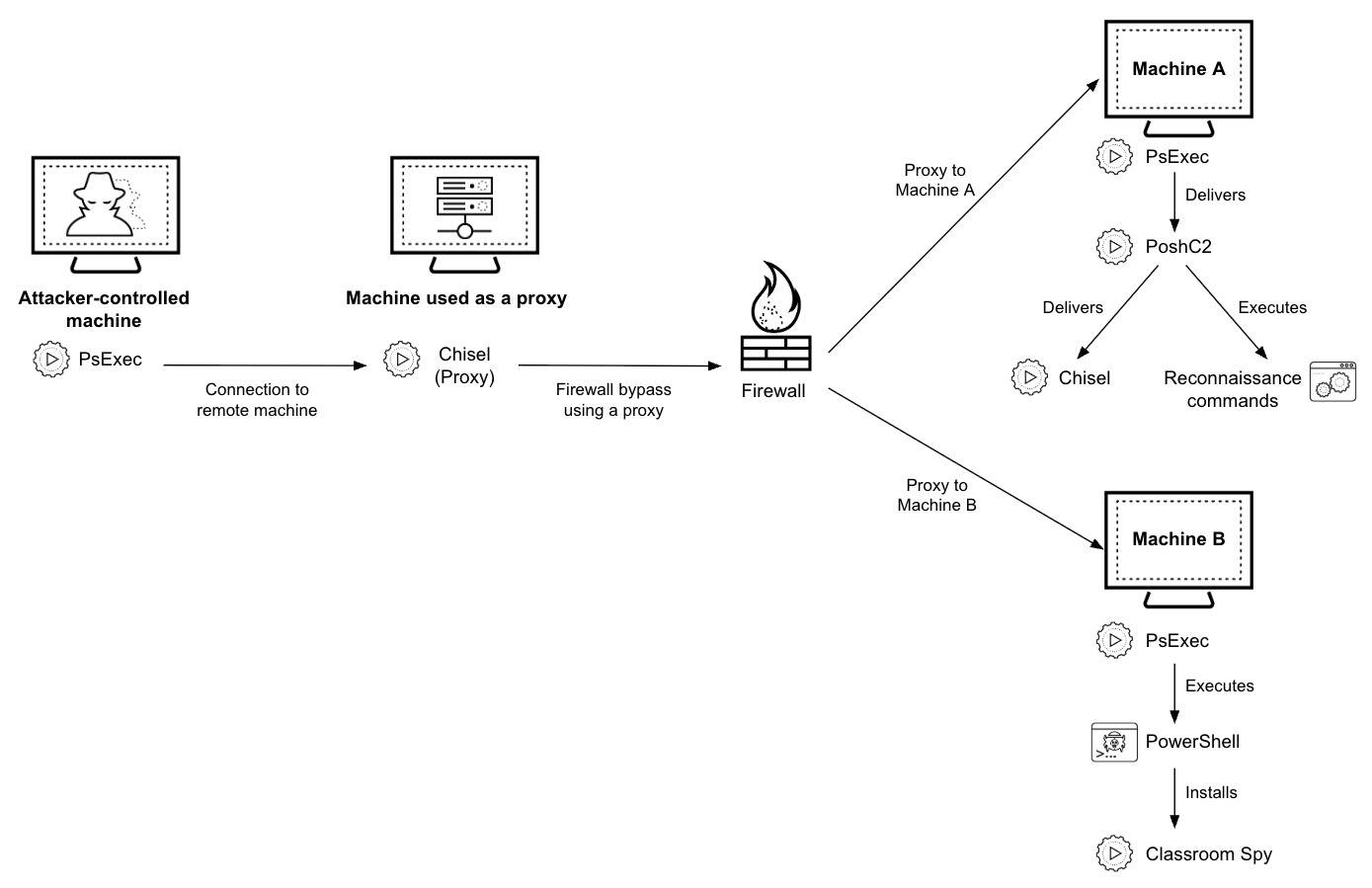
RapperBot is a botnet family active since 2021, primarily targeting IoT devices such as routers and network cameras with weak passwords or vulnerabilities, and it has recently started extorting victims with protection fees. The botnet uses sophisticated custom encryption algorithms for its command and control communication and exhibits a unique DNS-TXT record resolution technique for its C2 domains. #RapperBot #Deepseek #NETLAB360

ComfyUI, a popular AI image-generation framework, has been targeted by Pickai, a lightweight backdoor exploiting its vulnerabilities to steal sensitive AI data and maintain persistent control over infected hosts. Pickai leverages diverse process spoofing, multiple persistence mechanisms, and a resilient network communication strategy involving rotating command-and-control domains, threatening large-scale supply chain networks including Rubick.ai and its customers. #ComfyUI #Pickai #Rubickai

In January 2025, a threat group targeted users in Taiwan using the HoldingHands RAT, distributing malware via phishing emails disguised as official government messages. This campaign involved complex attack chains with multiple loaders and shellcode snippets, continuously evolving alongside other malware families like winos 4.0 and Gh0stCringe. #HoldingHandsRAT #winos4.0 #Gh0stCringe #TaiwanPhishingCampaign
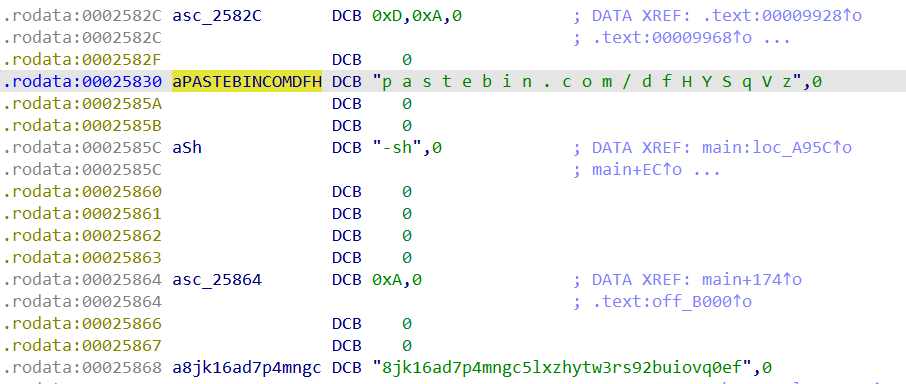
Researchers identified a threat actor cluster named CL-CRI-1014 targeting financial institutions in Africa using open-source tools like PoshC2, Chisel, and Classroom Spy to gain initial access and sell it on dark web markets. The attackers employ evasion techniques such as forging legitimate file signatures and disguising malware to maintain persistence and…
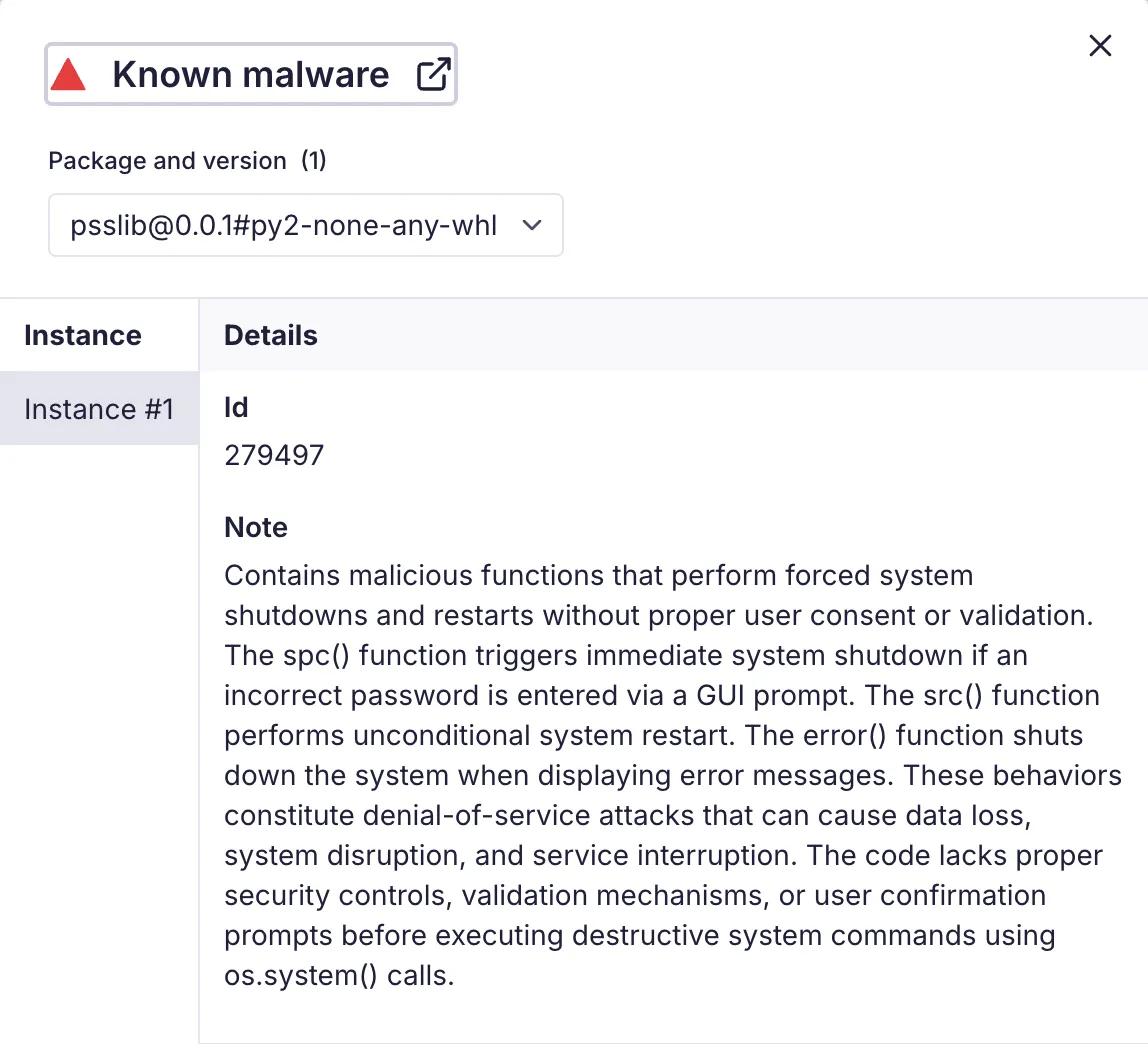
The malicious Python package psslib, published by threat actor umaraq, masquerades as a password security tool but forces immediate Windows system shutdowns upon incorrect password entry. This typosquatting attack targets developers relying on the legitimate passlib library and highlights risks in software supply chains. #psslib #umaraq #passlib

Zscaler ThreatLabz researchers discovered AI-themed websites exploiting Black Hat SEO to spread malware such as Vidar Stealer, Lumma Stealer, and Legion Loader through complex redirection chains and browser fingerprinting. These campaigns use deceptive JavaScript hosted on trusted CDNs and package malware in large installers to evade detection, targeting users searching for popular AI tools. #VidarStealer #LummaStealer #LegionLoader #BlackHatSEO #getrunkhomuto_info

CERT-AGID identified a malspam campaign targeting an Italian email provider’s storage space, delivering the malware XWorm and Katz Stealer through a complex multi-stage infection chain. The attack leveraged steganography within an image to hide payloads and employed PowerShell obfuscation along with MSBuild.exe for execution. #KatzStealer #XWorm #CERTAGID

This article analyzes a Havoc variant malware used in a sustained cyber intrusion targeting critical national infrastructure in the Middle East, detailing its deployment via a disguised remote injector mimicking conhost.exe. The Havoc framework’s modular design enables attackers to remotely control compromised Windows systems through a range of commands and in-memory execution techniques. #Havoc #RemoteAccessTrojan #conhost.exe
CyberAv3ngers is a cyber threat group engaged in Iran-Israel conflict, blending real cyberattacks with psychological operations and propaganda to influence public perception and sow fear. Their activities range from hijacking industrial control systems to orchestrating narrative-driven campaigns supported by suspected ties to Iran’s IRGC-Cyber Electronic Command. #CyberAv3ngers #IRGCCEC #IOCONTROL

Iranian state-sponsored APT groups such as APT35, APT33, and Pioneer Kitten are expected to increase cyber attacks targeting cloud and Linux environments following U.S. strikes on Iranian nuclear infrastructure. The Sysdig Threat Research Team provides guidance and detection strategies to help organizations defend against these advanced threats. #APT35 #APT33 #PioneerKitten

Insikt Group identified a new Delphi-based variant of the DRAT remote access trojan, named DRAT V2, used by the TAG-140 threat actor targeting Indian government organizations. This variant introduces enhanced command execution capabilities and updated C2 obfuscation techniques, reflecting TAG-140’s evolving tradecraft in espionage campaigns. #DRATV2 #TAG140 #BroaderAspect
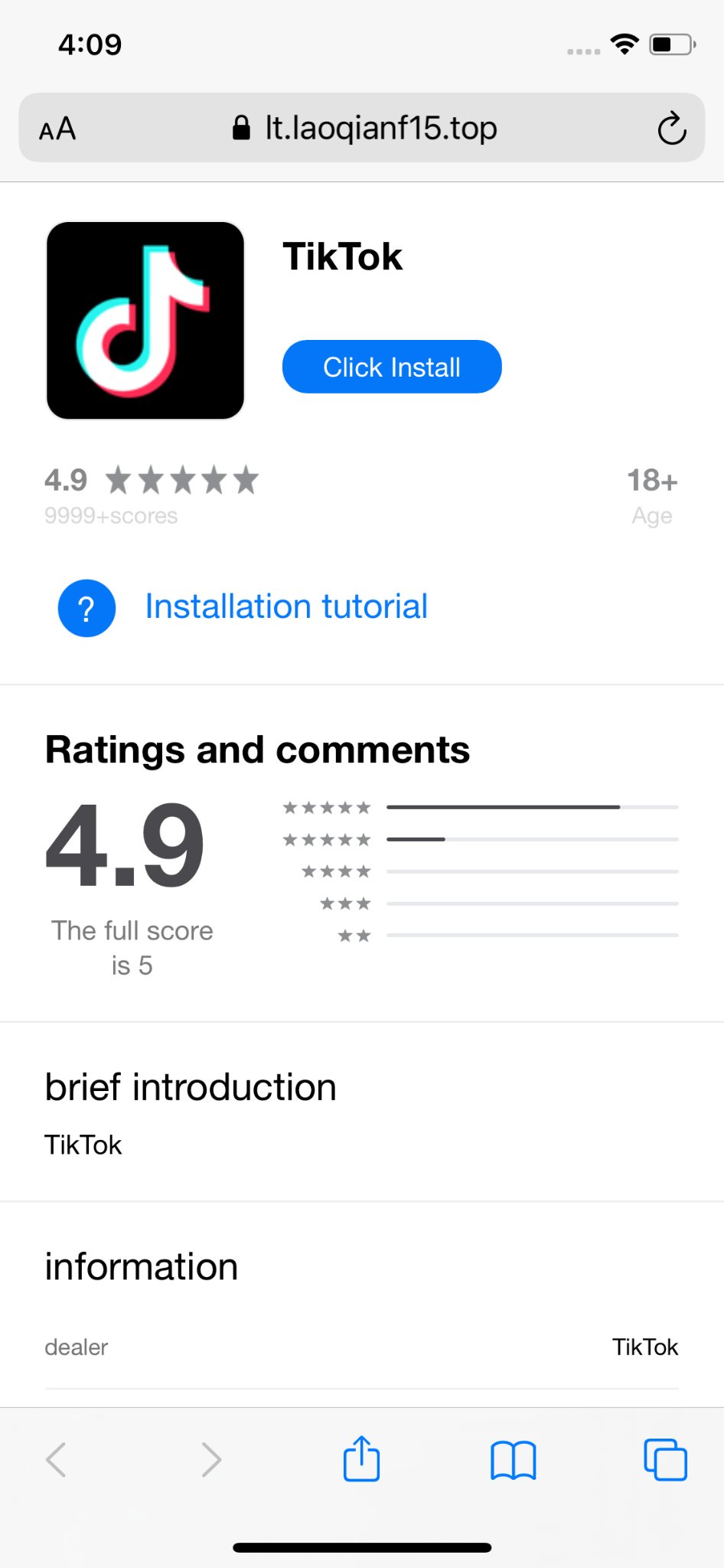
In early 2025, a spyware campaign linked to the SparkCat group was identified targeting crypto wallet seed phrases by exfiltrating images from victims’ devices on iOS and Android, using malicious frameworks and apps distributed via official and unofficial app stores. This spyware uses sophisticated techniques, including AES-256 encryption and OCR to select images, and has infected thousands of users primarily in Southeast Asia and China. #SparkCat #SparkKitty #TikTokMall #AFNetworking #SINOPEC_SABIC

Since March 2025, there has been a rise in malware infections using validly signed ConnectWise software abused by threat actors through Authenticode stuffing. Attackers manipulate ConnectWise configurations to disguise remote access malware with fake icons and messages, evading detection by many antivirus products. #EvilConwi #ConnectWise #AuthenticodeStuffing

A PowerShell script named y1.ps1 was discovered in an open directory on a Chinese server, acting as a shellcode loader that executes malicious code in-memory and connects to Cobalt Strike infrastructure for post-exploitation activities. The script utilizes evasion techniques like API hashing and reflective DLL injection and communicates with command-and-control servers hosted mainly in China, Russia, and other global locations. #PowerShellLoader #CobaltStrike #BaiduCloud #BegetLLC