The Iranian APT group Educated Manticore has intensified spear-phishing attacks targeting Israeli journalists, cybersecurity experts, and academics using sophisticated phishing kits disguised as legitimate Google authentication pages. Their campaigns employ multi-stage tactics, including fake Google Meet invitations and dynamic React-based phishing infrastructure, to harvest credentials and 2FA codes, enabling cyber-espionage aligned with Iran-Israel tensions. #EducatedManticore #IranIsraelConflict #GooglePhishingKit
Keypoints
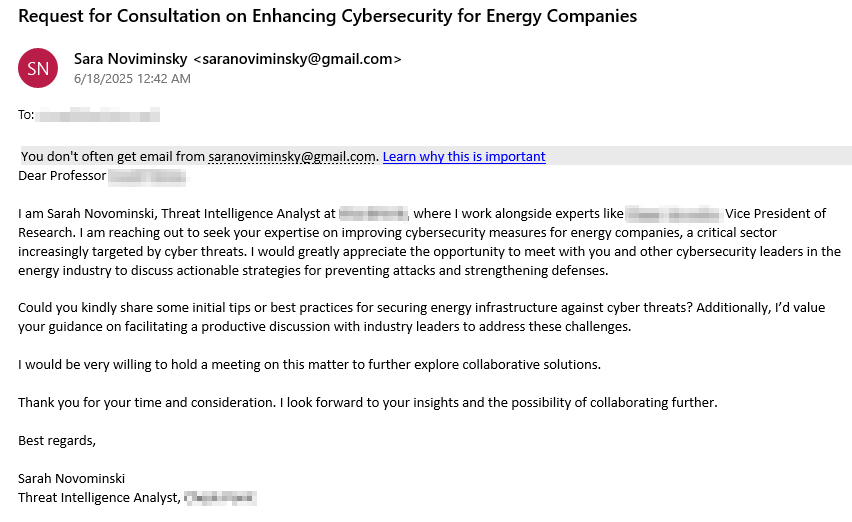
- Educated Manticore, linked to Iran’s IRGC-IO, targets Israeli cybersecurity and technology professionals through spear-phishing emails and WhatsApp messages impersonating cybersecurity company employees.
- Victims are lured to sophisticated React-based Single Page Application phishing kits mimicking Google, Outlook, and Yahoo login pages that capture passwords and multi-factor authentication codes.
- The phishing infrastructure supports dynamic authentication flows and includes a passive WebSocket keylogger to capture every keystroke in real-time.
- Fake Google Meet invitations hosted on Google Sites are used to increase legitimacy and direct victims to attacker-controlled credential harvesting pages.
- From January 2025, the group operates a large phishing domain infrastructure comprising over 130 domains linked to a dozen IP addresses, mainly registered through NameCheap.
- The phishing kits and domains demonstrate rapid setup, frequent takedown evasion, and use modern web technologies to maintain operational resilience and effectiveness.
- Educated Manticore’s activities reflect persistent targeting within the context of the Iran-Israel conflict, focusing on stealing credentials for espionage and identity theft.
MITRE Techniques
- [T1566] Spearphishing – Used spear-phishing campaigns via email and WhatsApp to deliver phishing links impersonating trusted individuals (“Initial vector: Spear-phishing”).
- [T1587.001] Develop Capabilities: Malware – Developed custom phishing kits serving as Single Page Applications to mimic login pages and harvest credentials (“Google Authentication Custom Phishing Kit”).
- [T1539] Steal Web Session Cookie – Phishing pages capture credentials and 2FA codes to facilitate unauthorized access (“enabling them to intercept both passwords and 2FA codes”).
- [T1110] Brute Force – The phishing kits allow capturing of multiple authentication steps for relay attacks bypassing MFA (“By supporting authentication flows, the kit enables 2FA relay attacks”).
- [T1204] User Execution – Social engineering tactics used to convince targets to interact with attackers and provide credentials (“prompt and persuasive interactions”).
- [T1566.002] Spearphishing Link – Delivered links in WhatsApp and email messages that direct victims to attacker-controlled pages (“fake Gmail login pages or Google Meet invitations”).
- [T1606] Forge Web Credentials – Used fake login pages hosted on attacker-controlled domains and Google Sites to steal credentials (“multi-stage phishing pages hosted on Google Sites”).
Indicators of Compromise
- [IP Addresses] Infrastructure IPs used by phishing domains – Examples: 185.130.226.71, 45.12.2.158, and others in cluster of at least a dozen IPs.
- [Domains] Phishing and backend domains used for hosting kits and infrastructure – Examples include idea-home.online, sendly-ink.shop, conn-ectionor.cfd, and over 130 additional domains related to campaigns.
- [File hashes] (Not explicitly listed in the article.)
- [URLs] Phishing URLs directing to phishing infrastructure – Examples: https://sendly-ink.shop/YtgtyyzP, Google Sites URLs hosting fake Google Meet pages.
Read more: https://research.checkpoint.com/2025/iranian-educated-manticore-targets-leading-tech-academics/