The malicious Python package psslib, published by threat actor umaraq, masquerades as a password security tool but forces immediate Windows system shutdowns upon incorrect password entry. This typosquatting attack targets developers relying on the legitimate passlib library and highlights risks in software supply chains. #psslib #umaraq #passlib
Keypoints
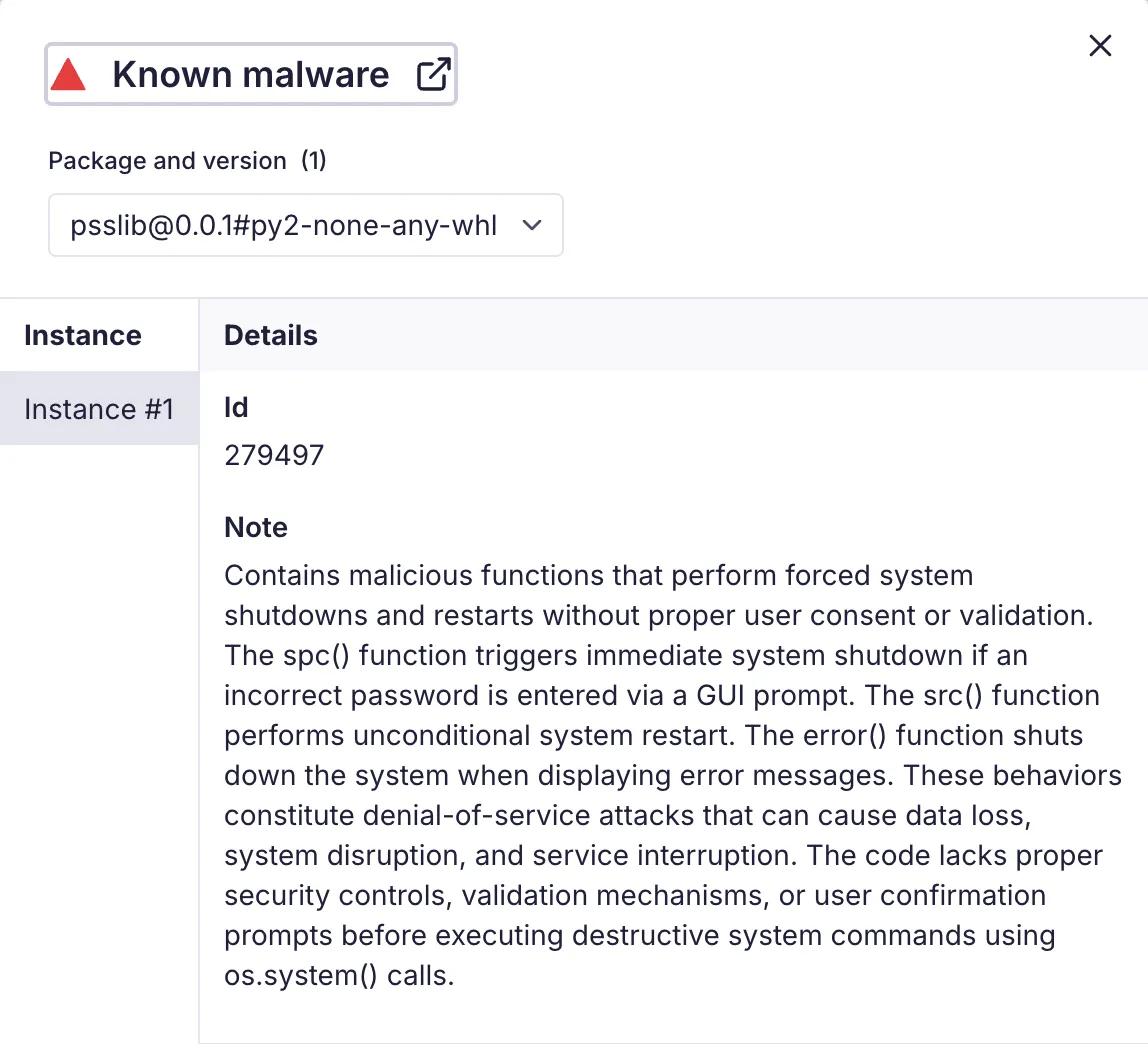
- The psslib package pretends to be a security library but executes immediate shutdown commands on Windows systems when incorrect passwords are entered.
- It typosquats the widely-used passlib library, exploiting developer trust and targeting Python developers using authentication tools.
- psslib contains multiple functions to forcibly shut down or restart Windows systems without authentication or warning.
- The malicious commands only affect Windows systems, as Linux/macOS platforms do not support the Windows-specific shutdown syntax.
- This attack demonstrates supply chain risks with destructive payloads disguised as useful security software.
- Future threats may evolve to target other platforms, use more sophisticated triggers, and blend legitimate functionality with destructive behavior.
- Socket’s security tools can help detect such malicious packages in real time through pull request analysis, CLI alerts, and browser extensions.
MITRE Techniques
- [T1195.002] Supply Chain Compromise – The psslib package compromises the software supply chain by typosquatting a legitimate library and inserting malicious code. (‘Supply Chain Compromise: Compromise Software Supply Chain’)
- [T1036.005] Masquerading – The package mimics the legitimate passlib library name to deceive developers. (‘Masquerading: Match Legitimate Name or Location’)
- [T1529] System Shutdown/Reboot – The package executes Windows shutdown commands to force immediate system shutdown upon incorrect password entry. (‘System Shutdown/Reboot’)
Indicators of Compromise
- [Malicious Package] Python package on PyPI – psslib, a typosquatted package targeting passlib users.
- [Threat Actor Identifiers] PyPI alias and emails – umaraq; umar[.]maq@yandex[.]com, umarmoiz2010@gmail[.]com.
Read more: https://socket.dev/blog/malicious-python-package-typosquats-popular-passlib-library