RapperBot is a botnet family active since 2021, primarily targeting IoT devices such as routers and network cameras with weak passwords or vulnerabilities, and it has recently started extorting victims with protection fees. The botnet uses sophisticated custom encryption algorithms for its command and control communication and exhibits a unique DNS-TXT record resolution technique for its C2 domains. #RapperBot #Deepseek #NETLAB360
Keypoints
- RapperBot was first disclosed by CNCERT in July 2022 but has been active since 2021, with over 50,000 bots observed and daily targeting above 100 devices since March 2025.
- The botnet primarily infects IoT devices with public network access, especially network cameras and routers, exploiting Telnet weak passwords and known vulnerabilities.
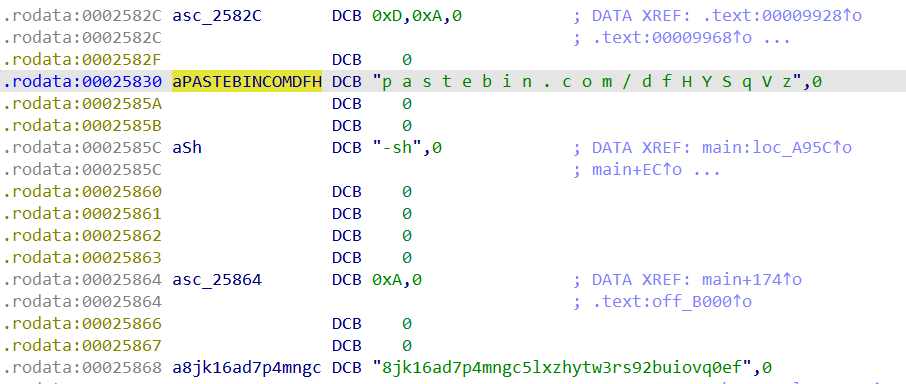
- RapperBot uses DNS-TXT records to resolve C2 domains with a complex custom decryption algorithm introduced in 2025 and rotates through 32 generated C2 domains.
- The malware has undergone at least seven variants, evolving its encryption and proxy capabilities, with key focuses on string decryption and DNS-TXT record parsing.
- Unlike many botnets, RapperBot’s network protocol is simple, employing XOR with a variable key and various packet types for login, heartbeat, and attack commands.
- The botnet has actively attacked significant platforms like the AI platform DeepSeek and Twitter and spreads extortion messages demanding $5,000 XMR for protection.
- XLAB registered some unused C2 domains proactively to monitor botnet scale and distribution, confirming over 50,000 active bot IP addresses in recent months.
MITRE Techniques
- [T1110] Brute Force – Used Telnet weak passwords to gain access to IoT devices (‘primarily spreads through Telnet weak passwords and exploits known vulnerabilities’).
- [T1071] Application Layer Protocol – Uses DNS-TXT records for command and control domain resolution with custom encryption (‘RapperBot resolves its C2 domain through DNS-TXT records’).
- [T1499] Endpoint Denial of Service – Executes DDoS attacks against various targets (‘primarily used for DDoS attacks with proxy capabilities added starting October 2024’).
- [T1204] User Execution – Contains provocative messages and taunts within samples possibly to influence reverse engineers (‘authors asked reverse engineers whether they listened to their music whilst analyzing’).
Indicators of Compromise
- [Domain] C2 domains generated and monitored – iranistrash.libre, churchofhollywood.libre, iguessimhere.libre, and 32 other domains with .info and .live TLDs.
- [IP Address] Hardcoded backup C2 servers – 86.104.72.130 (Canada), 194.156.98.15 (China), 94.131.118.154 (France), plus others.
- [XMR Wallet] Extortion payments – 48SFiWgbAaFf75KsRSEEr4iDcxrevFzVmhgfb6Qudss52JK8cCR8bwmUxNBPN2VmqDTucJL3eabiZc5XRYVGkbh6BH58Ytk for protection fee donations.
- [Download Domain] Malware download sites – pool.rentcheapcars.sbs, o0s.cc, 4v.wtf, zyb.ac.
- [File Hash] Sample variants with SHA1 hashes – e.g., 8a9a098dabcc09c8a770777f12c71017bb26940b (2023-07-21), cc687e707919c4176ab03bdc76ab01bbaa7c0e22 (2024-10-10).
Read more: https://blog.xlab.qianxin.com/rapperbot-en/