Researchers identified a threat actor cluster named CL-CRI-1014 targeting financial institutions in Africa using open-source tools like PoshC2, Chisel, and Classroom Spy to gain initial access and sell it on dark web markets. The attackers employ evasion techniques such as forging legitimate file signatures and disguising malware to maintain persistence and bypass detection. #CL-CRI-1014 #PoshC2 #Chisel #ClassroomSpy
Keypoints
- CL-CRI-1014 has targeted African financial institutions since at least July 2023, aiming to broker initial network access for sale on dark web markets.
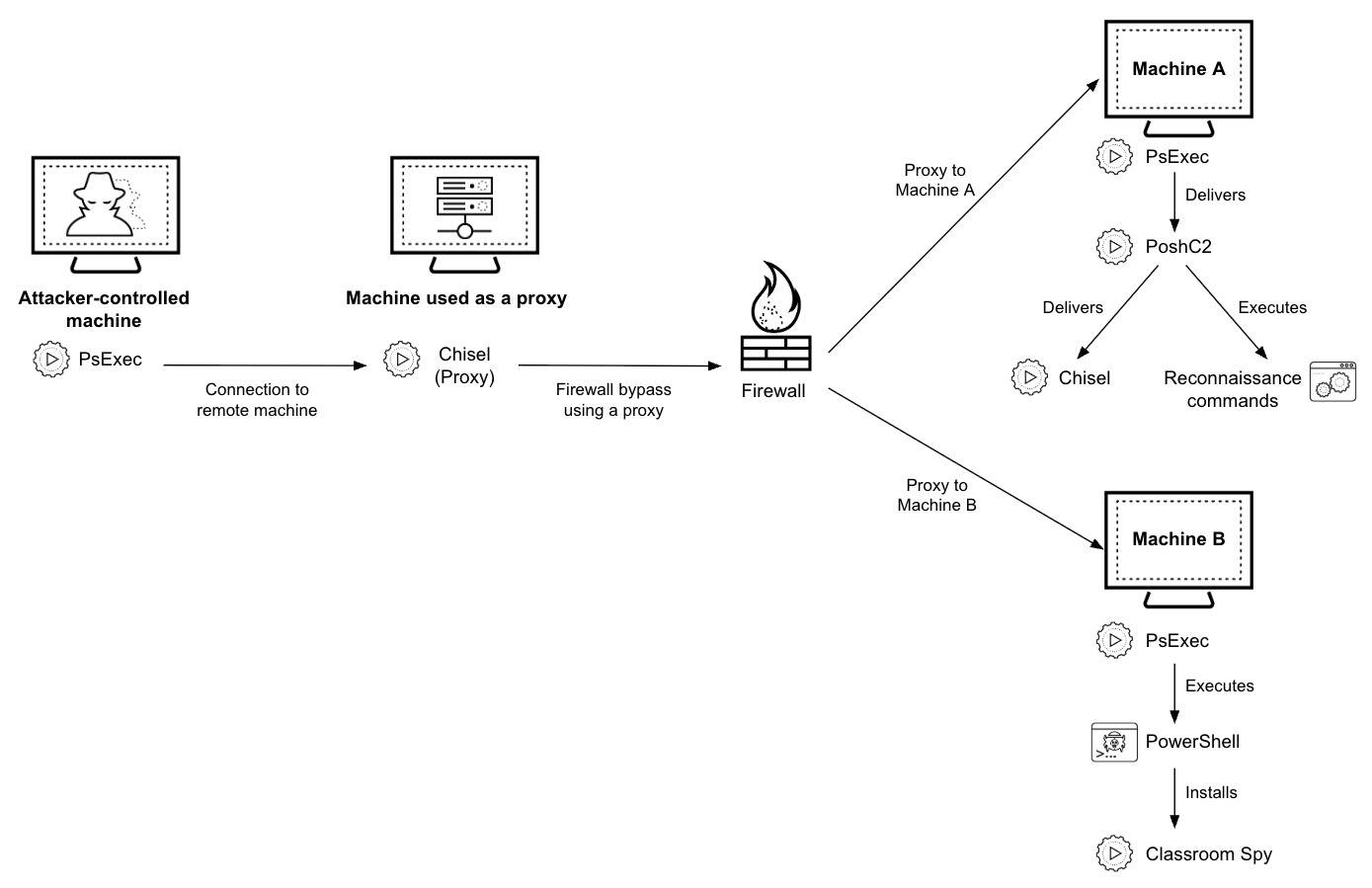
- The threat actor uses open-source tools including PoshC2 (attack framework), Chisel (tunneling utility), and Classroom Spy (remote administration software) in their attack playbook.
- Classroom Spy is deployed via PowerShell scripts, renamed, and installed as a service to facilitate covert remote monitoring and control.
- Attackers forge file signatures and mimic legitimate application icons and names (e.g., Microsoft, Cortex, VMware) to hide malicious activities.
- PoshC2 implants utilize custom packers with anti-analysis features and implement proxy communications using stolen credentials.
- Persistence mechanisms include creating scheduled tasks disguised as legitimate services, startup folder shortcuts, and Windows services.
- Chisel is employed as a SOCKS proxy tunnel to bypass network controls such as firewalls for covert communication within compromised environments.
MITRE Techniques
- [T1059] Command and Scripting Interpreter – PowerShell scripts (slr.ps1, sqlx.ps1) are used to deploy Classroom Spy by extracting files from ZIP archives and installing them as services (‘PowerShell scripts to deploy and install Classroom Spy’).
- [T1105] Ingress Tool Transfer – Use of publicly available open-source tools like PoshC2, Chisel, and Classroom Spy transferred onto target systems for establishing foothold (‘using a combination of open-source and publicly available tools to establish their attack framework’).
- [T1562] Impair Defenses – Forging file signatures and mimicking legitimate application icons and paths to evade detection (‘disguised the tools used in these operations as legitimate processes’).
- [T1098] Account Manipulation – Use of stolen user credentials for proxy communication and lateral movement (‘stole user credentials for the infected networks and used them to set up a proxy’).
- [T1543] Create or Modify System Process – Establishing persistence by creating services, scheduled tasks, and startup folder shortcuts (‘Creating a service, saving a shortcut in Startup folder, using scheduled tasks for persistence’).
- [T1572] Protocol Tunneling – Using Chisel as a SOCKS proxy to tunnel communication and bypass network controls (‘Chisel as a SOCKS proxy to forward traffic’).
Indicators of Compromise
- [SHA256 Hashes] PoshC2 packed payloads – e.g., 3bbe3f42857bbf74424ff4d044027b9c43d3386371decf905a4a1037ad468e2c, 9149ea94f27b7b239156dc62366ee0f85b0497e1a4c6e265c37bedd9a7efc07f, and 11 more hashes.
- [SHA256 Hashes] Chisel executables – e.g., bc8b4f4af2e31f715dc1eb173e53e696d89dd10162a27ff5504c993864d36f2f, 9a84929e3d254f189cb334764c9b49571cafcd97a93e627f0502c8a9c303c9a4, and 3 more hashes.
- [SHA256 Hashes] Classroom Spy files – e.g., 831d98404ce5e3e5499b558bb653510c0e9407e4cb2f54157503a0842317a363, f5614dc9f91659fb956fd18a5b81794bd1e0a0de874b705e11791ae74bb2e533.
- [Domains] Malicious domains associated with campaign – finix.newsnewth365[.]com, mozal.finartex[.]com, vigio.finartex[.]com, bixxler.drennonmarketingreviews[.]com, genova.drennonmarketingreviews[.]com, and others.
Read more: https://unit42.paloaltonetworks.com/cybercriminals-attack-financial-sector-across-africa/