The Androxgh0st botnet has evolved with a significant increase in the number and variety of Initial Access Vectors (IAVs), exploiting vulnerabilities in popular platforms, IoT devices, and academic institution servers. It uses webshells, command injection, and cryptomining payloads hosted via compromised domains such as the University of California, San Diego’s “USArhythms” subdomain. #Androxgh0st #Spring4Shell #ApacheShiro #Lantronix
Category: Threat Research

A phishing campaign since early 2024 leverages legitimate cloud services like TryCloudflare to deliver evasive malware such as AsyncRAT, enabling remote access, credential theft, and ransomware across thousands of organizations. The campaign uses multi-stage execution with Python scripts and cloud tunneling to bypass traditional endpoint protections, highlighting the need for layered defense strategies. #AsyncRAT #TryCloudflare #Halcyon
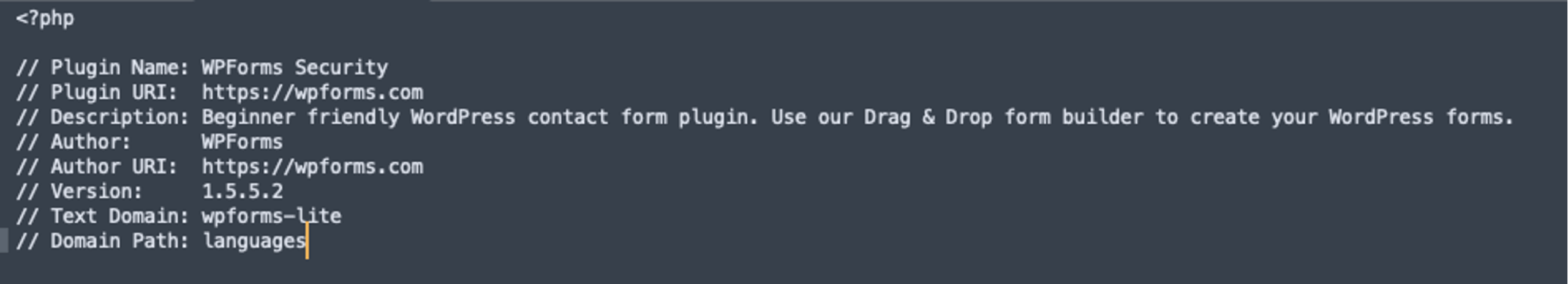
A malicious WordPress plugin named php-ini.php was found creating a hidden admin user on infected websites, activated only via a specific URL parameter. The attackers used a simplistic approach by replacing legitimate plugin files and hardcoding the admin account, making detection easier. #php-iniphp #mr_administartor

New variants of Chaos RAT have been identified targeting both Windows and Linux systems through phishing campaigns using malicious PDFs. The malware employs advanced obfuscation techniques to steal data, deploy cryptominers, and maintain persistent control over infected devices. #ChaosRAT #RemoteAdministrationTool

The article analyzes a targeted intrusion by the North Korean BlueNoroff threat group against a Web3 organization, focusing on phishing lures disguised as Zoom extensions and extensive infrastructure pivoting using DNS, host, and registration data. Nearly 200 related malicious domains and numerous IP addresses linked to DPRK activity were identified to enable proactive threat tracking. #BlueNoroff #APT38 #LazarusGroup #ZoomExtension #Validin

Between June 12-18, 2025, over 35 pro-Iranian hacktivist groups launched coordinated cyberattacks against Israeli infrastructure, primarily using DDoS, website defacements, and data breaches. Despite a high volume of attacks, the methods remained unsophisticated and often involved exaggerated claims to gain media attention. #DDoS #HackYourMom #APT_IRAN

APT36, a Pakistan-based cyber espionage group, is conducting sophisticated phishing campaigns targeting Indian defense personnel by distributing malicious PDFs that mimic official government documents to steal credentials. The malware employs advanced anti-analysis methods, keylogging, and encrypted communication to maintain long-term access and exfiltrate sensitive data. #APT36 #TransparentTribe #IndiaDefense #PhishingCampaign #CYFIRMA
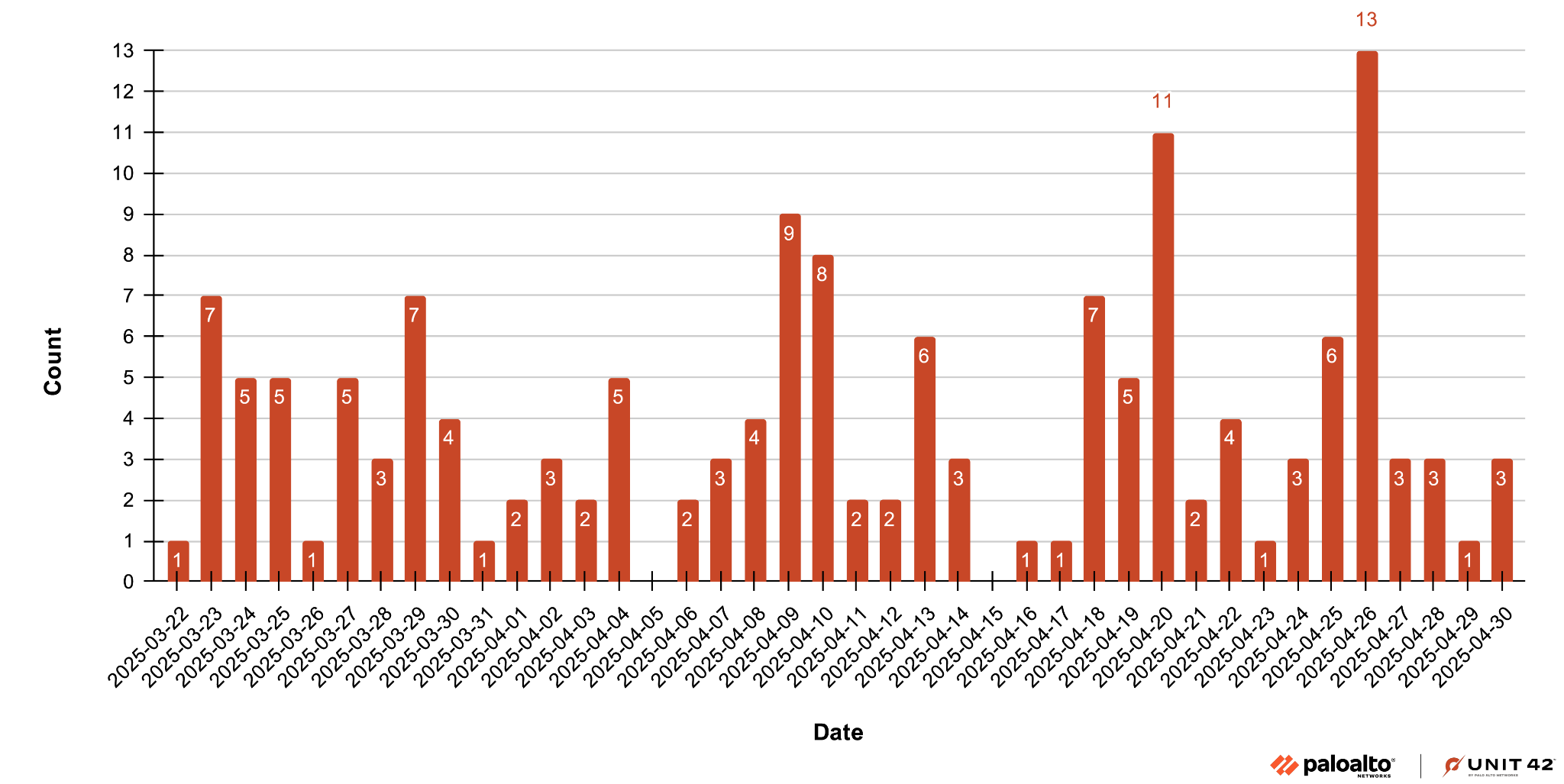
In March 2025, the Prometei botnet resurfaced with new Linux variants featuring enhanced stealth through UPX packing and a custom configuration JSON trailer. This malware focuses on cryptocurrency mining and credential theft while employing a domain generation algorithm and self-updating capabilities to maintain persistence. #Prometei #Monero #Unit42…
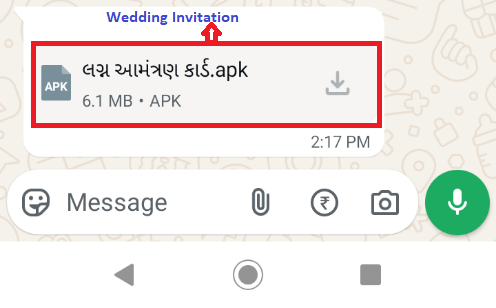
An Android phishing campaign named “Wedding Invitation” utilizes the SpyMax RAT to steal banking and personal information from Indian mobile users through a malicious APK distributed via WhatsApp. The malware collects keystrokes, intercepts notifications for OTPs, and exfiltrates compressed data to a C2 server to facilitate fraudulent activities. #SpyMax #WeddingInvitation #AndroidRAT #IndianMobileUsers
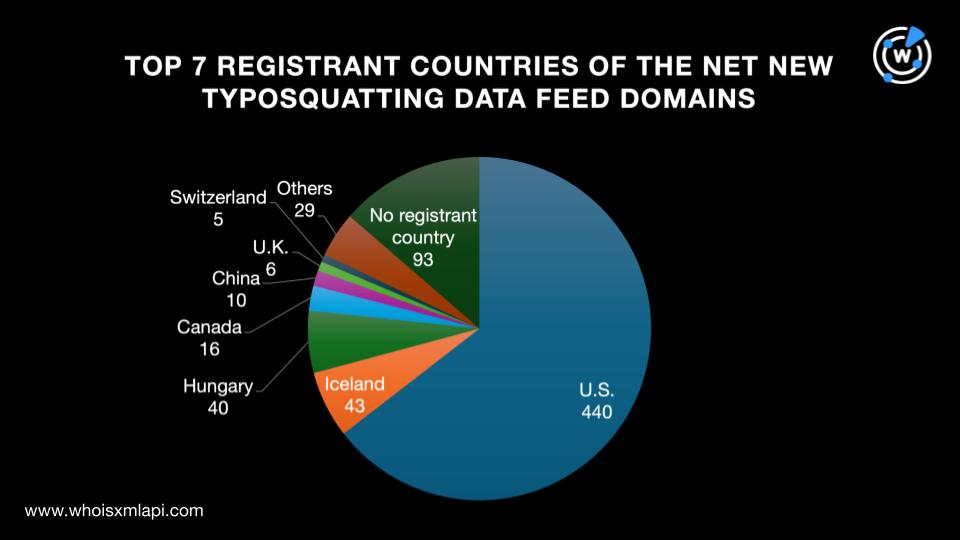
The FBI issued a warning about the LabHost phishing-as-a-service campaign, revealing over 42,000 related indicators of compromise. An extensive DNS investigation uncovered additional typosquatting domains, IP addresses, and subdomains associated with the campaign. #LabHost #PhishingAsAService #IASC

Iran-aligned cyber threat actors, including APT42, MuddyWater, APT34, and Handala, conduct sophisticated espionage and disruptive campaigns primarily targeting Israeli and regional adversaries. These groups employ tactics such as spear-phishing, DNS tunneling, and DDoS attacks, reflecting Iran’s strategic geopolitical objectives. #APT42 #MuddyWater #APT34 #Handala

Infostealer malware disguised as legal and copyright infringement documents is actively distributed in Korea via email attachments, employing DLL Side-Loading and double extension techniques to evade detection. The malware targets sensitive user information, exfiltrating data related to emails, FTP, banking, and browser credentials to remote servers. #Rhadamanthys #Infostealer #DLLSideLoading #DoubleExtension…
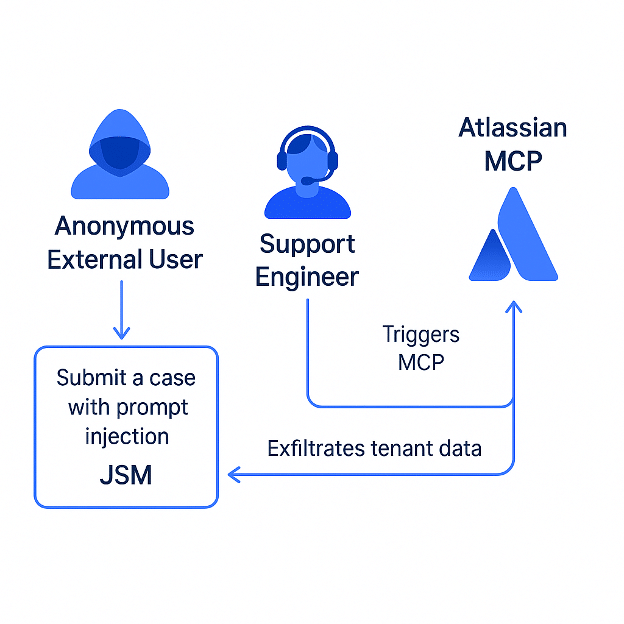
The article reveals a novel “Living off AI” attack that exploits Atlassian’s Model Context Protocol (MCP) integration with Jira Service Management to execute prompt injection attacks through malicious support tickets, granting threat actors privileged access without direct authentication. It highlights the need for prompt isolation and AI usage monitoring to prevent such vulnerabilities in enterprise AI workflows. #LivingOffAI #AtlassianMCP #JiraServiceManagement

Acronis Threat Research Unit identified the Shadow Vector malware campaign targeting Colombian users through malicious SVG files and spear-phishing emails impersonating legal institutions. The campaign deploys multistage payloads including AsyncRAT and RemcosRAT using DLL side loading and driver-based privilege escalation, with advanced obfuscation and anti-analysis techniques. #ShadowVector #AsyncRAT #RemcosRAT #KatzLoader
A phishing campaign exploits the GovDelivery system by using a fake toll payment scenario tied to a misleading .gov domain, aiming to steal personal and credit card information from employees. The campaign leverages fear and mimics legitimate services like TxTag to increase its effectiveness. #GovDelivery #TxTag #txtag-help.xyz
