In early 2025, a spyware campaign linked to the SparkCat group was identified targeting crypto wallet seed phrases by exfiltrating images from victims’ devices on iOS and Android, using malicious frameworks and apps distributed via official and unofficial app stores. This spyware uses sophisticated techniques, including AES-256 encryption and OCR to select images, and has infected thousands of users primarily in Southeast Asia and China. #SparkCat #SparkKitty #TikTokMall #AFNetworking #SINOPEC_SABIC
Keypoints
- The new spyware campaign affects both iOS and Android, deploying malicious frameworks disguised as legitimate libraries and delivering payloads via official app stores and third-party sources.
- The malware targets crypto wallet seed phrases by exfiltrating images from the device gallery using OCR technology.
- On iOS, malware is embedded as malicious frameworks mimicking AFNetworking or Alamofire, using Objective-C’s load selector to execute payloads.
- Android variants include Java and Kotlin malicious Trojans, with some implementing Xposed modules for hooking app code.
- Malicious apps were found on Google Play and the App Store, including modified TikTok versions and crypto-themed applications such as 币coin and SOEX.
- The spyware uses encrypted configuration files and communicates with C2 servers via RESTful APIs to receive commands and upload stolen images.
- Provisioning profiles, especially iOS Enterprise profiles, are exploited to install and run malicious apps bypassing App Store restrictions.
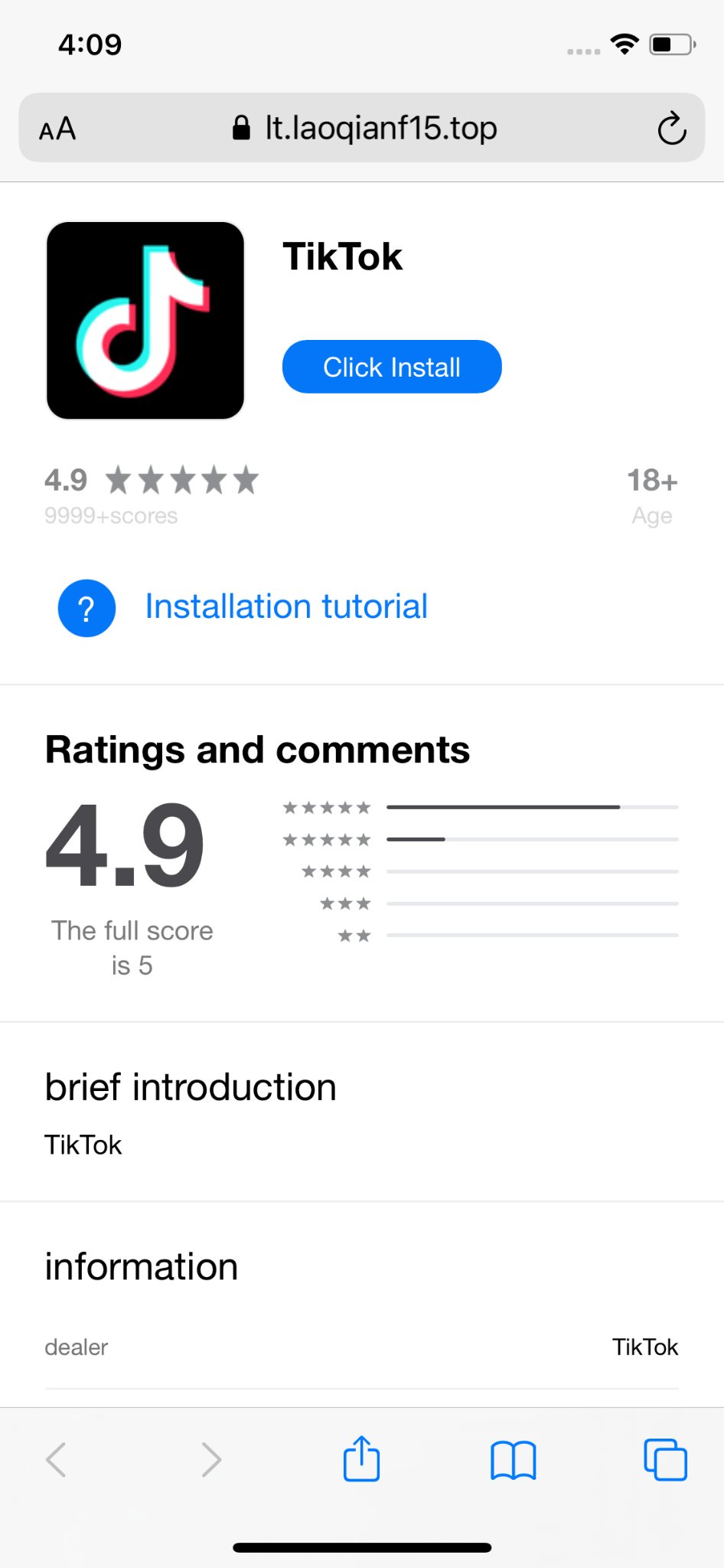
- Attackers utilize social media ads and scam platforms to distribute these trojans and PWAs, mainly targeting users in Southeast Asia and China.
- The campaign is linked to the earlier SparkCat spyware through shared infrastructure, code artifacts, and targeted app families.
MITRE Techniques
- [T1552] Unsecured Credentials – Malware retrieves Base64-encoded and AES-256 encrypted configuration data including C2 URLs from its Info.plist or UserDefaults. (‘It retrieves the Base64-encoded value of the ccc key from the framework’s Info.plist file…The decrypted value is a list of URLs from which the malware fetches additional payloads’)
- [T1071.001] Application Layer Protocol: Web Protocols – Malware sends GET and PUT requests to C2 servers to check authorization and exfiltrate stolen images. (‘The malware sends a GET request to the /api/getImageStatus endpoint…Data transmission is performed…by making a PUT request to the /api/putImages endpoint’)
- [T1547.001] Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder / Objective-C +load Selector – The malicious AFNetworking framework exploits Objective-C’s load selector (+[AFImageDownloader load]) to run payload at app load time. (‘…they took advantage of a feature in Objective-C that allows classes to define a special load selector, which is automatically called when the app is loading’)
- [T1189] Drive-by Compromise – iOS users are tricked into installing provisioning profiles to run malicious apps through fake App Store mimics. (‘visiting the website on an iPhone triggers…prompts them to download an app…using Enterprise profiles’)
- [T1005] Data from Local System – Spyware accesses user photo galleries on iOS and Android to collect images. (‘The malware requests access to the user’s photo gallery and registers a callback function to monitor any changes within the gallery’)
- [T1110] Brute Force – The malware tries multiple C2 servers by measuring response times and selects the fastest for communication. (‘Among the decrypted C2 addresses… It does this by sending a request to each server sequentially…The shortest time then determines which C2 server is used’)
- [T1059.001] Command and Scripting Interpreter: PowerShell – Usage of Frida script for dynamic analysis of malicious libraries was noted, showing the technique used to analyze malware behavior. (‘Using Frida, we can execute any piece of code as a function…’)
Indicators of Compromise
- [File Hash – Android infected apps] examples include b4489cb4fac743246f29abf7f605dd15e8b60bf5af2d5cc5c501b87d04b8a6c2aa… and others.
- [File Hash – iOS infected apps] examples include 21ef7a14fee3f64576f5780a637c57d16d39cd8421591fbb0cc2a0bce4d0357dc6a… and others.
- [File Hash – malicious iOS frameworks] example 8c9a93e829cba8c4607a7265e6988646b3085cd623b57fd6561e964d6fd734134 …
- [File Hash – obfuscated malicious iOS libraries] examples include 0b7891114d3b322ee863e4eef94d85230d09c4f956bb734586cee85887ed54072a …
- [Domain Names] Distribution and C2: hxxps://lt.laoqianf14[.]top/KJnn, hxxps://accgngrid[.]com, hxxps://byteepic[.]vip
- [IP Addresses] Command and Control servers include 23.249.28[.]88, 120.79.8[.]107, 47.119.171[.]161
- [URLs] Configuration and C2 endpoints: hxxp://120.78.239[.]17:10011/req.txt, hxxps://data-sdk2.oss-accelerate.aliyuncs[.]com/file/SGTMnH951121, hxxps://1111333[.]cn-bj.ufileos[.]com/file/SGTMnH951121
- [File Paths] Android device file storing device ID: /sdcard/aray/cache/devices/.DEVICES
Read more: https://securelist.com/sparkkitty-ios-android-malware/116793/