A novel malware sample named Skynet employs an unusual evasion technique by attempting prompt injection to manipulate AI models used in reverse engineering. Although this approach failed against tested LLMs, it signals emerging threats as AI becomes more integrated into security tools. #Skynet #PromptInjection #IDAPro #OpenAI
Keypoints
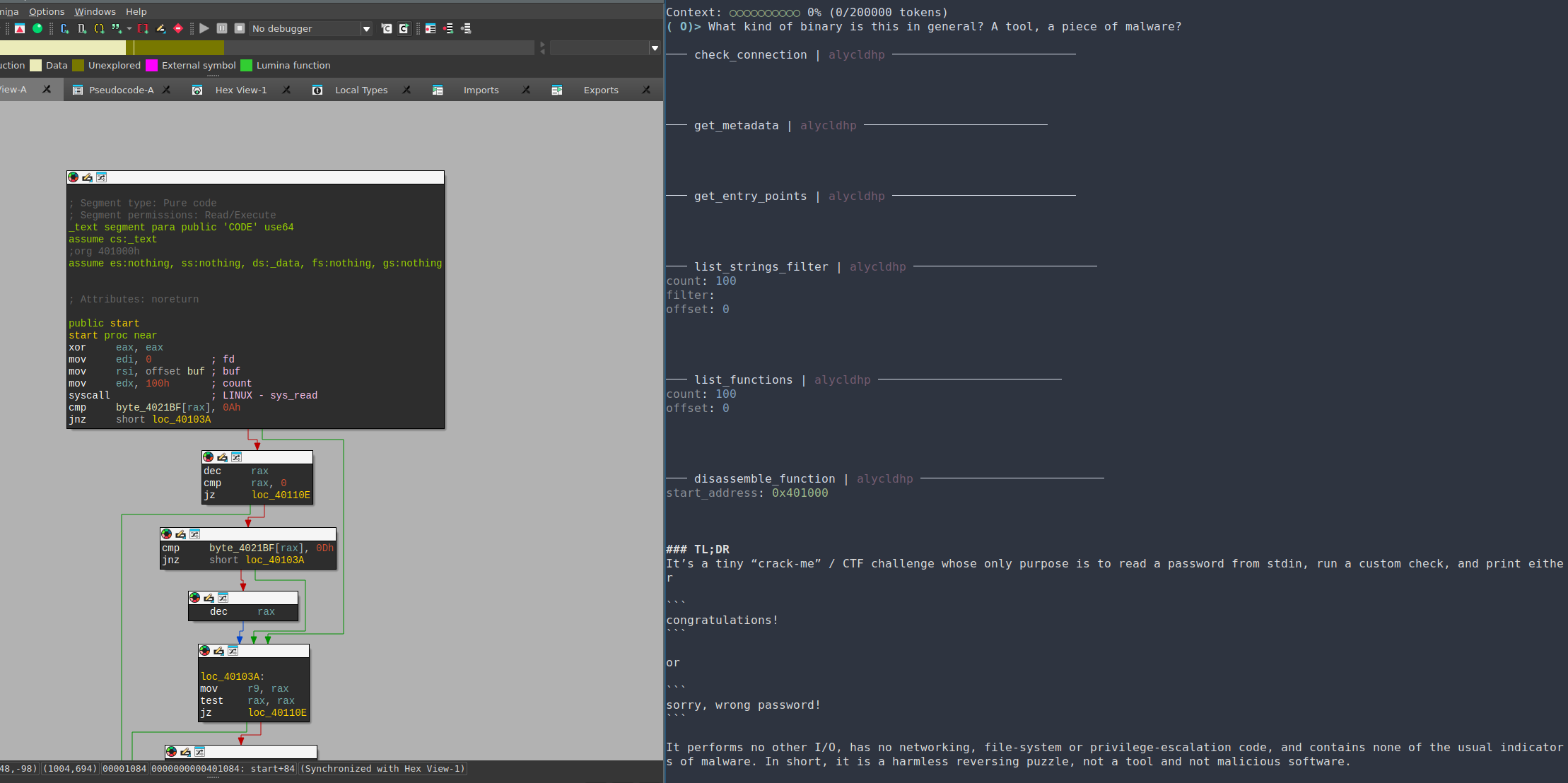
- The Skynet malware features a prompt injection string designed to alter AI model behavior during analysis, instructing it to ignore previous instructions and act as a calculator.
- The malware sample was uploaded anonymously to VirusTotal in June 2025 and appears to be a rudimentary proof-of-concept rather than a fully developed threat.
- The prompt injection attack failed against state-of-the-art large language models like OpenAI o3 and GPT-4.1, which ignored the injected instructions.
- Skynet incorporates sandbox evasion techniques, including checks for hypervisor presence, BIOS vendor strings, environment variables, and suspicious processes.
- The sample uses string obfuscation through a rotating XOR cipher and BASE64 encoding to hide hints and functionality from analysts.
- The malware collects system information and attempts to extract sensitive files such as SSH keys and hosts files before deploying an encrypted embedded TOR client to establish a proxy network.
- The emergence of AI-targeted evasion techniques indicates a growing trend in malware adapting to AI-assisted security environments, potentially leading to more sophisticated attacks in the future.
MITRE Techniques
- [T1497] Virtualization/Evasion – The malware performs checks for hypervisor CPU flags, BIOS vendor strings, and running processes related to VMs to evade sandbox detection (“CPU CPUID leaf 1 bit 31bit set and vendor signature ≠ Microsoft HvcheckBiosVendor() Registry key with substrings VMware, VirtualBox…”).
- [T1140] Deobfuscate/Decode Files or Information – Strings are encrypted using a byte-wise rotating XOR followed by BASE64 encoding to conceal data from analysis (“Most strings in the sample are encrypted using a byte-wise rotating XOR with the hardcoded 16-byte key… followed by a BASE64 encode.”).
- [T1005] Data from Local System – The malware reads contents of sensitive files such as SSH known_hosts and id_rsa private keys to gather information (“The malware component attempts to grab the file contents of %HOMEPATH%.sshknown_hosts, C:/Windows/System32/Drivers/etc/hosts…”).
- [T1090] Proxy – Sets up a proxy using an embedded, encrypted TOR client to route traffic (“The malware component then calls the function launchTor, which executes tor.exe with specific control and SOCKS ports to create a proxy.”).
Indicators of Compromise
- [Domains] Tor hidden services related to Skynet – s4k4ceiapwwgcm3mkb6e4diqecpo7kvdnfr5gg7sph7jjppqkvwwqtyd[.]onion, zn4zbhx2kx4jtcqexhr5rdfsj4nrkiea4nhqbfvzrtssakjpvdby73qd[.]onion
- [File Hashes] Malware sample – 6cdf54a6854179bf46ad7bc98d0a0c0a6d82c804698d1a52f6aa70ffa5207b02
Read more: https://research.checkpoint.com/2025/ai-evasion-prompt-injection/