The FBI released a FLASH report detailing indicators of compromise related to the Funnull infrastructure used in cryptocurrency investment fraud between October 2023 and April 2025. Analysis revealed over 277,000 related domains, including more than 101,000 new typosquatting domains, with significant global DNS activity and patterns tied to specific geographic locations and registrars. #Funnull #Typosquatting #FBI_FLASH_Report
Keypoints
- The FBI identified 176,656 root domains linked to the Funnull infrastructure from two IoC lists, comprising 549 CNAMEs and over 332,000 URLs.
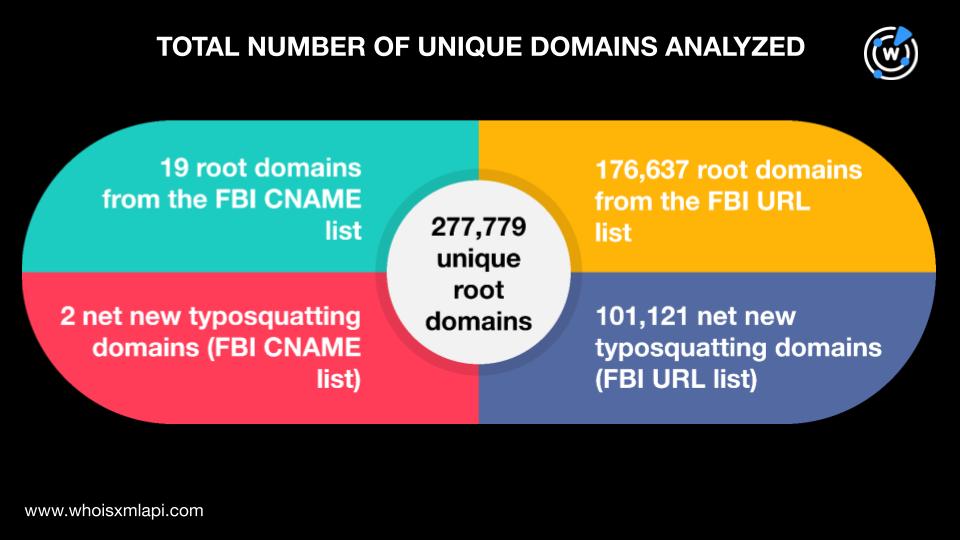
- Analysis uncovered 101,123 new typosquatting domains related to the FBI-identified domains, expanding the dataset to 277,779 domains.
- Over 82,000 domains were flagged as likely to become malicious immediately after registration between January 2024 and June 2025.
- DNS traffic data from May to June 2025 showed 22,772 unique client IPs querying 1,062 distinct domains with nearly 190,000 DNS requests.
- Hong Kong was the top geolocation for resolving IP addresses, while the U.S. was the leading registrant country for the combined domains.
- The top ISPs for domain resolutions included Cloudflare, Amazon, Dimension Network, and others, with a 70% overlap between FBI and typosquatting domain ISPs.
- The majority of domains had .com gTLDs, with many others registered under gTLDs such as .vip, .cc, .top, and ccTLD .cn, created mainly between 2021 and 2025.
MITRE Techniques
- [T1587] Develop Capabilities – Threat actors created large numbers of typosquatting domains to support infrastructure for fraud scams (“…net new typosquatting domains uncovered…bringing the total number of domains to analyze to 277,779”).
- [T1590] Gather Victim Network Information – Analysis of DNS traffic data (“…22,772 unique client IP addresses querying 1,062 distinct domains…”) helped identify active infrastructure and victim engagement.
- [T1583] Acquire Infrastructure – Use of domain registration and clustering techniques to expand malicious domain sets (“…using domain clustering techniques to identify multiple groups of similar-looking domains…”).
Indicators of Compromise
- [Domain Names] Over 176,656 root domains extracted from FBI IoC lists, plus 101,123 net new typosquatting domains identified.
- [URLs] 332,696 URLs related to the Funnull infrastructure formed part of the FBI’s data sets.
- [IP Addresses] 22,772 unique client IP addresses queried the domains during May-June 2025, with top geolocations including Hong Kong and the U.S.
- [Registrant Countries] Domains registered across 70 countries, prominently the U.S., China, and the Philippines.
- [Registrar IANA IDs] Top IANA IDs included 146, 472, and 1923 among a total of 185 unique IDs.
Read more: https://circleid.com/posts/down-the-dns-funnel-and-into-the-funnull-infrastructure