AsyncRAT, an open-source remote access trojan, has evolved through numerous forks, significantly impacting malware landscapes with variants like DcRat and VenomRAT. These forks extend functionality with unique plugins and advanced evasion techniques, highlighting the growing sophistication of open-source malware threats. #AsyncRAT #DcRat #VenomRAT #NonEuclidRAT #JasonRAT
Keypoints
- AsyncRAT was released as an open-source RAT in 2019 and has given rise to many variants and forks, expanding its reach and capabilities.
- DcRat and VenomRAT are among the most widely deployed AsyncRAT forks, incorporating features such as MessagePack data serialization and AMSI/ETW bypass.
- NonEuclid RAT is a lesser-known variant that introduces unique plugins like WormUsb.dll for malware spreading and cliper.dll for clipboard hijacking.
- JasonRAT features obfuscation via modified Morse code and country targeting, showing continued development in AsyncRAT derivatives.
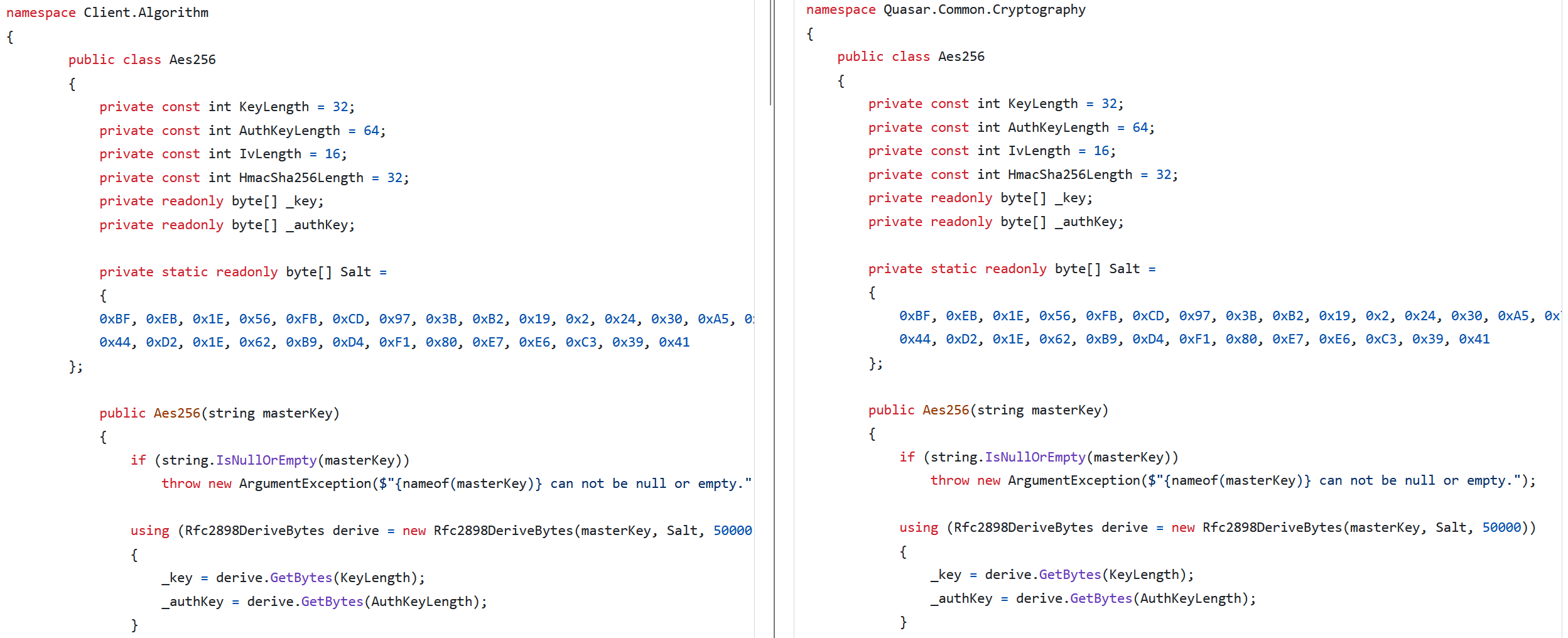
- Identification of AsyncRAT forks is often possible through encrypted configuration fields like the ‘Version’ and custom cryptographic salts.
- Lesser-known variants include specialized plugins for audio playback, geolocation, brute forcing, clipboard monitoring, and ransomware capabilities.
- The proliferation of these forks demonstrates the risks associated with open-source malware frameworks, enabling rapid adaptation and misuse by threat actors.
MITRE Techniques
- [T1562.001] Impair Defenses: Disable or Modify Tools – DcRat terminates security tools such as Taskmgr.exe and MsMpEng.exe to evade detection (‘DcRat terminates security tools such as Taskmgr.exe and MsMpEng.exe’).
- [T1562.004] Impair Defenses: Disable or Modify System Firewall – DcRat leverages AMSI and ETW bypass techniques to prevent script scanning and event tracing (‘DcRat leverages AMSI and ETW bypass techniques to evade detection’).
- [T1027.013] Obfuscated Files or Information: Encrypted/Encoded File – JasonRAT uses modified Morse code and obscure variable names to hinder malware analysis (‘JasonRAT employs modified Morse code and obscure variable names to hinder analysis’).
- [T1539] Steal Web Session Cookie – DcRat includes a plugin to steal Discord tokens from infected devices (‘DcRat leverages a plugin to steal Discord tokens from compromised machines’).
- [T1555.003] Credentials from Password Stores: Credentials from Web Browsers – XieBroRAT uses BrowserGhost.dll to harvest browser credentials (‘XieBroRAT uses a plugin to collect browser credentials’).
- [T1110.003] Brute Force: Password Spraying – NonEuclid RAT employs a plugin to brute force SSH and FTP credentials (‘NonEuclid uses a plugin to brute force SSH and FTP credentials’).
- [T1614.001] System Location Discovery: System Language Discovery – NonEuclid RAT collects geolocation data from victims (‘NonEuclid uses a plugin that collects geolocation data from compromised systems’).
- [T1123] Audio Capture – DcRat’s microphone plugin enables recording audio from infected systems (‘DcRat has a microphone plugin that enables audio capture from the victim’s device’).
- [T1125] Video Capture – DcRat supports webcam access through its plugins (‘DcRat includes a webcam plugin that allows remote access to the victim’s camera’).
- [T1115] Clipboard Data – NonEuclid RAT monitors and replaces clipboard cryptocurrency addresses (‘NonEuclid uses a plugin that monitors the clipboard to intercept and replace cryptocurrency wallet addresses’).
- [T1486] Data Encrypted for Impact – DcRat’s ransomware plugin uses AES-256 to encrypt victim files (‘DcRat features a ransomware plugin capable of encrypting files on the victim’s system’).
Indicators of Compromise
- [File Hashes] Samples of NonEuclid RAT plugins – F8E31B338123E38757F8B7099797119A038A3538 (Screamer.dll), 2FA98D088486BAC57FF60E072E28FEE5830E7B28 (WormUsb.dll), and others.
- [File Hashes] DcRat and VenomRAT clients – B8AB93E958E0DE4BE2766B2537832EDB37030429 (DcRat Client.exe), 68B58483D0E4E7CC2478D6B4FC00064ADE3D7DB3 (VenomRAT Microsoft_Edge_Driver.exe).
- [File Hashes] JasonRAT client – FF4592A8BCB58F5CF6BD70B882E886EC6906EECD (Servant.exe).
- [File Hashes] Other AsyncRAT forks – 4F69E0CE283D273B724CE107DF89F11C556A7A4E (BoratRAT Client.exe), 3124F58428184FDF75E21B1E5A58CADF9DD2BA03 (PhoenixRAT Stub.exe), and more.
Read more: https://www.welivesecurity.com/en/eset-research/unmasking-asyncrat-navigating-labyrinth-forks/