The article details the distribution of Lumma Stealer malware via cracked versions of popular software, followed by the deployment of Rsockstun malware for post-infection activities. It highlights infection methods, associated files, command and control traffic, and persistence mechanisms involving a pen test tool configured as malware. #LummaStealer #Rsockstun #TurnitinCrackMalware
Keypoints
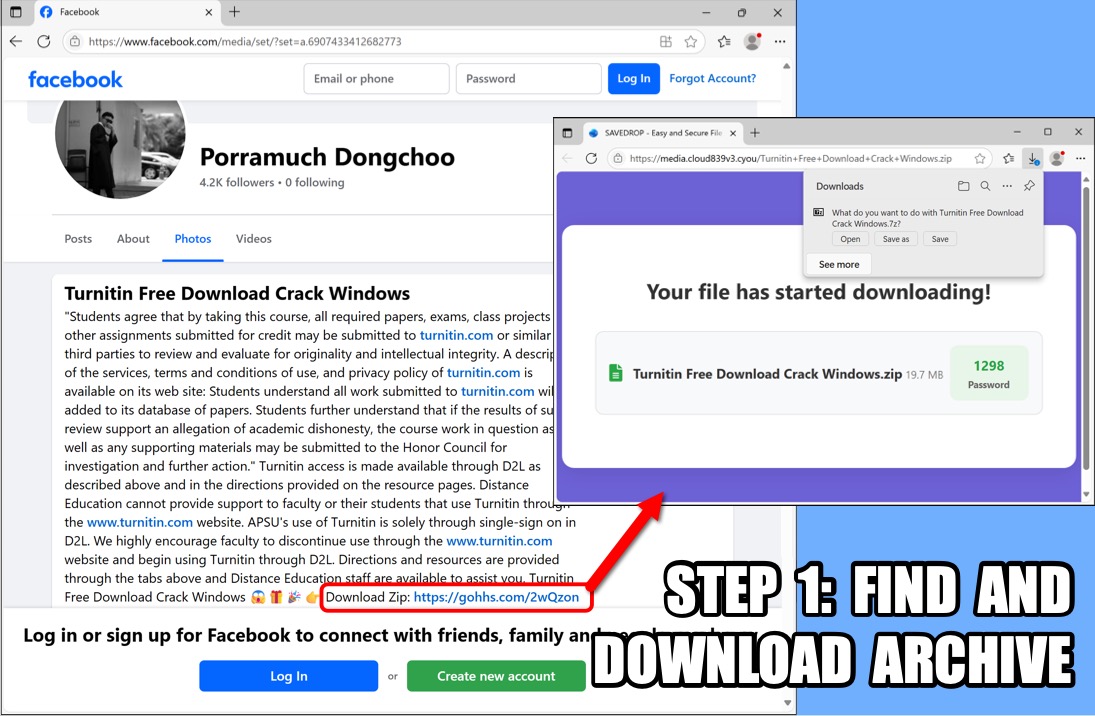
- Lumma Stealer malware is distributed disguised as cracked versions of Turnitin software via several URLs.
- The initial download is a password-protected 7-Zip archive containing the malware installer.
- Malware installer files include inflated executables and dropped components such as cabinet (.cab) and batch (.bat) files used to execute the infection.
- After infection, a loader downloads and executes a pen test tool configured as Rsockstun malware for follow-up C2 communication.
- Persistence is achieved through a Windows shortcut in the Startup directory launching the malicious pen test tool with specific connection parameters.
- Command and Control traffic includes TLSv1.3 encrypted communications to domains such as genhqq[.]xyz, metallurgify[.]com, and uses Telegram API for communication.
- File hashes and infection paths are documented for detection and analysis.
MITRE Techniques
- [T1071] Application Layer Protocol – The malware uses HTTPS and TLSv1.3 traffic for command and control communication, as seen in “…TLSv1.3 HTTPS traffic to 144.172.115[.]212:443 and genhqq[.]xyz…”.
- [T1036] Masquerading – Lumma Stealer is disguised as cracked versions of legitimate software such as Turnitin, indicated by “…distributed as cracked versions of popular software…”.
- [T1112] Modify Registry – Persistence is created via a Windows shortcut placed in the Startup directory, shown by “…Windows shortcut (.lnk file) in the Start Menu’s Startup directory…”.
- [T1204] User Execution – Infection initiates by user downloading and executing password-protected archives from URLs, “…password-protected 7-Zip archive…”.
- [T1105] Ingress Tool Transfer – The Rsockstun malware (pen test tool) is downloaded from GitHub URLs during post-infection, referenced in “…retrieved by the above loader from GitHub…”.
Indicators of Compromise
- [File Hash] Lumma Stealer initial download – 06f1f7a336e1cd394e9599b10c6aa4e81baa9dc55de1dbb38e024fb25567a3c8 (7z archive), 5743fac858ce41d0f507d82517358c69652459283c133a3cdb70231792caa066 (installer EXE).
- [File Hash] Rsockstun malware – cdfa264eeb65a8b3ea2e49b248c7cb689899d3f9da2483d293365fdf1912313e (pen test tool configured as malware).
- [URL] Infection sources – hxxps[:]//media.cloud839v3[.]cyou/Turnitin+Free+Download+Crack+Windows.zip, hxxps[:]//arch.kot3jsd[.]my/bridge/u/Y27r2P1ouMf2u5AztNgPxot5/Turnitin%20Free%20Download%20Crack%20Windows.zip.
- [Domain] Command and Control – genhqq[.]xyz, metallurgify[.]com.
- [IP Address] C2 traffic endpoints – 144.172.115[.]212:443, 144.172.112[.]32:16443.
Read more: https://www.malware-traffic-analysis.net/2025/06/26/index.html