This article analyzes phishing campaigns abusing the DHL brand to target its partners, demonstrating how ANY.RUN’s tools can detect, investigate, and gather indicators of compromise from such attacks. It highlights the rise of supply chain attacks exploiting third-party relationships and shows practical methods to mitigate associated risks using sandboxing, YARA rules, and threat intelligence lookups. #DHLPhishing #SupplyChainAttack #SubmitFormCom
Keypoints
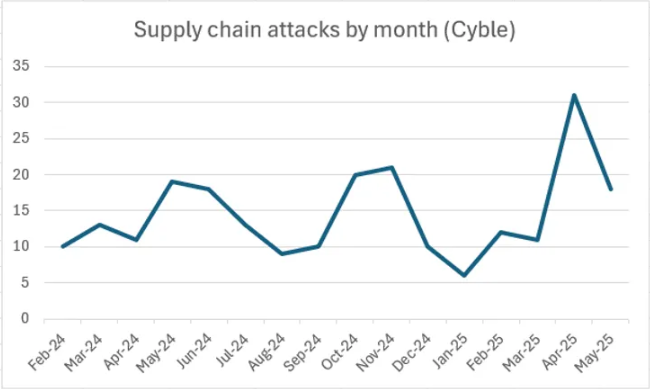
- Supply chain attacks are increasing, with attackers exploiting third-party relationships to infiltrate target organizations.
- Phishing campaigns impersonating DHL target partner organizations like Meralco using fake domains and deceptive attachments with uncommon file extensions for filter bypass.
- Credential theft is facilitated through a third-party form service (submit-form.com) collecting plaintext passwords submitted via phishing pages.
- Image hash analysis revealed multiple phishing campaigns using the same DHL-themed visual lure, indicating widespread brand abuse.
- ANY.RUN’s Threat Intelligence Lookup identified 39 phishing domains and over 300 malware samples with DHL-themed filenames, showing common obfuscation patterns.
- YARA rules can be employed effectively to scan emails mentioning DHL, helping to detect malicious correspondence in corporate infrastructures.
- Interactive sandboxing with HTTPS MITM enables in-depth analysis of encrypted network traffic from phishing attacks for credential theft detection.
MITRE Techniques
- [T1566] Phishing – Attackers send phishing emails impersonating DHL to steal credentials using deceptive attachments and fake domains (‘phishing emails disguised as official correspondence from DHL’).
- [T1556] Phishing for Information – Credential theft via a web form hosted on submit-form.com where victims submit passwords (‘a password submission form … used to collect credentials’).
- [T1204] User Execution – Victims are tricked into opening malicious .shtm attachments which bypass filters (‘HTML attachment bypasses filters: lesser-known file extensions are used’).
- [T1598] Phishing: Spearphishing Attachment – Use of .eml files with DHL branding to distribute phishing content targeting partners (‘YARA rule to find .eml files mentioning DHL’).
- [T1041] Exfiltration Over C2 Channel – Data exfiltration is done via HTTPS POST requests to submit-form.com (‘POST request containing plaintext credentials sent to a unique endpoint’).
Indicators of Compromise
- [Phishing Domains] DHL impersonation domains – Examples include patterns such as dhlshipment*, –dhl., and dhldocument* used in at least 39 identified phishing domains.
- [File Names] Malicious files with DHL-themed names – Examples include dhlreceipt*.pdf and dhldelivery* filenames, with over 300 samples analyzed.
- [File Hashes] SHA256 hash of DHL-themed phishing images – Used for reverse image search to identify related campaigns (5+ identical image hashes found).
- [Email Addresses] Spoofed senders – Example sender Haalasolamagic@cirrcor[.]com impersonating DHL in phishing emails.
- [Network Domains] submit-form.com – Third-party service domain used for credential collection in phishing campaigns (over 200 public analyses linked to this domain).
Read more: https://any.run/cybersecurity-blog/cybersecurity-blog/supply-chain-attacks-analysis/