CloudSEK’s TRIAD discovered a Clickfix-themed malware delivery site linked to the Epsilon Red ransomware that uses ActiveX to silently execute shell commands and download payloads. The threat actors employ social engineering with fake verification codes and impersonate popular services like Discord Captcha Bot and Twitch to increase victim engagement. #EpsilonRed #Clickfix #DiscordCaptchaBot
Keypoints
- A Clickfix-themed malware delivery site was uncovered in active development, linked to Epsilon Red ransomware campaigns.
- This variant uses ActiveXObject to silently execute shell commands that download and run payloads from attacker-controlled IPs.
- Social engineering tactics involve fake verification codes and prompts to visit secondary pages, differing from previous clipboard-based attacks.
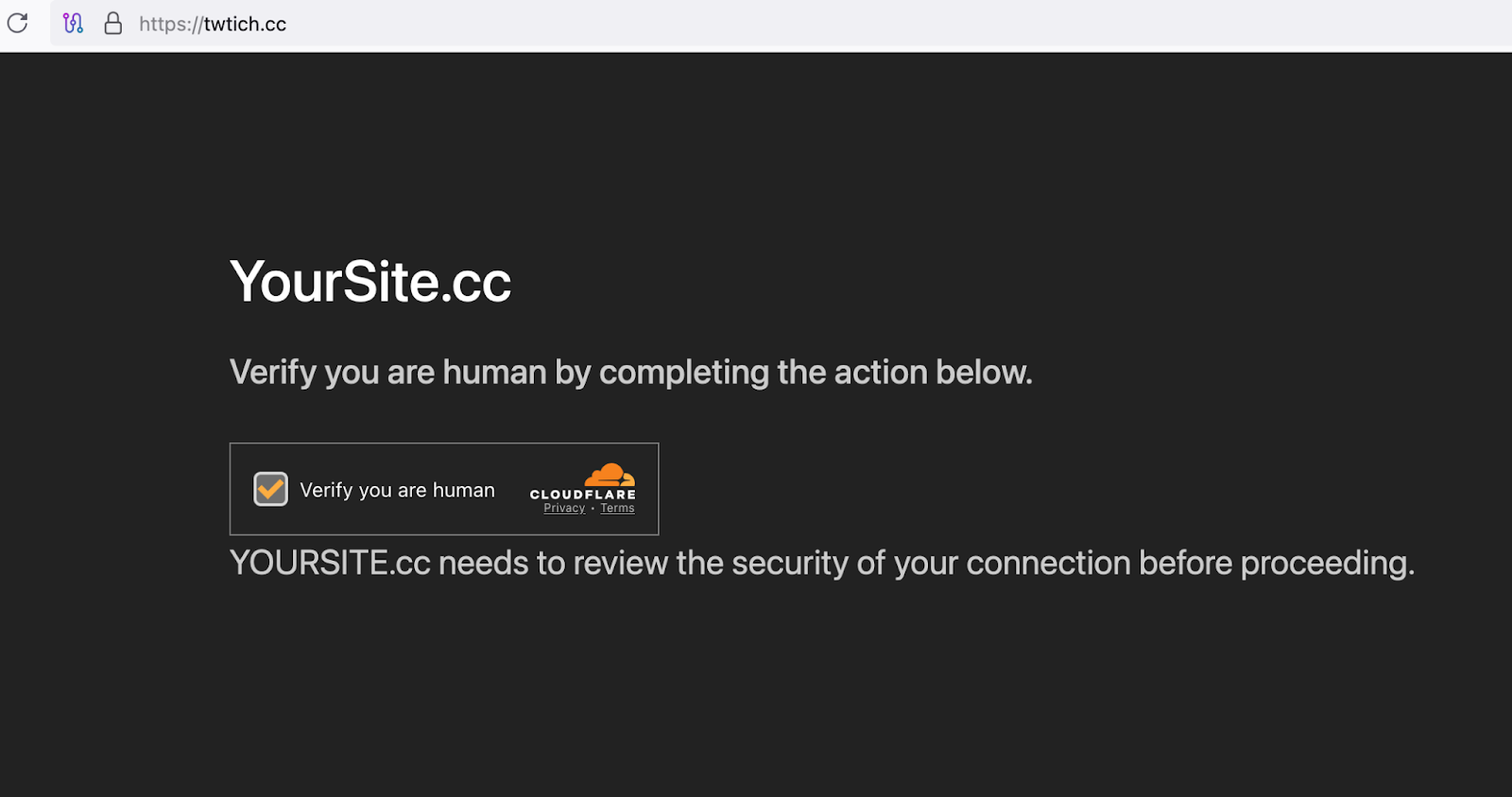
- Threat actors impersonate services such as Discord Captcha Bot, Kick, Twitch, and OnlyFans to lure victims.
- Epsilon Red ransomware was first observed in 2021 and has ransom note styling inspired by REvil but with distinct tactics and infrastructure.
- Indicators of compromise include specific IP addresses, domains, and file hashes related to payload delivery and command-and-control servers.
- Mitigation strategies recommend disabling ActiveX and Windows Script Host, threat intel integration, endpoint behavior analytics, and security awareness training.
MITRE Techniques
- [T1189] Phishing: Drive-by Compromise – Victims are lured to themed fake verification websites where malicious scripts execute without user interaction (‘themed websites (e.g., fake verification pages) where malicious scripts execute without user interaction’).
- [T1059.003] Command and Scripting Interpreter: Windows Command Shell – Uses cmd.exe to silently execute downloaded binaries and display social engineering messages (‘Uses cmd.exe to execute downloaded binaries and display social engineering messages’).
- [T1059.005] Command and Scripting Interpreter: JavaScript/VBScript – Malicious JavaScript using ActiveXObject(“WScript.Shell”) embedded in web pages executes commands on the host (‘Malicious JavaScript (ActiveXObject(“WScript.Shell”)) embedded in web pages executes commands on the host’).
- [T1204.001] User Execution: Malicious Link – Victims are socially engineered to click malicious links and follow staged instructions (‘Victims are socially engineered into clicking a malicious link and following staged instructions’).
- [T1027] Defense Evasion: Obfuscated Files or Information – Payload download and execution is performed silently with minimal visibility (‘The payload is delivered with minimal visibility (curl -s) and executed silently (Run(…, 0))’).
- [T1036] Defense Evasion: Masquerading – Use of fake verification codes and benign themes to mislead users and evade detection (‘Use of fake verification codes and benign themes (e.g., captcha verification) to mislead users and security analysts’).
- [T1053.005] Persistence: Scheduled Task/Job – Epsilon Red uses scheduled tasks to maintain persistence after execution (‘Epsilon Red campaigns have historically used scheduled tasks for persistence post-execution’).
- [T1071.001] Command and Control: Application Layer Protocol – Web Protocols – Uses HTTP via curl to download payloads and possibly for C2 communication (‘Uses HTTP (via curl) for payload download and possibly for follow-up C2 traffic’).
- [T1486] Impact: Data Encrypted for Impact – Final-stage ransomware encrypts victim files following infection (‘Final-stage ransomware (Epsilon Red) encrypts victim files after initial infection’).
Indicators of Compromise
- [md5] Epsilon Red ransomware payload – 98107c01ecd8b7802582d404e007e493
- [md5] Quasar RAT malware – 2db32339fa151276d5a40781bc8d5eaa
- [Domain] Clickfix delivery domains – twitch[.]cc, capchabot[.]cc
- [IP:Port] Command and Control servers – 155.94.155[.]227:2269, 213.209.150[.]188:8112