The Proxy Trickster group has been active since 2024, targeting hundreds of global IT infrastructures for financial gain through proxyjacking and cryptocurrency mining. They employ advanced evasion techniques like utility masquerading and automate attacks via complex script chains, leveraging tools such as gs-netcat for remote control. #ProxyTrickster #gs-netcat #XMRig
Keypoints
- Proxy Trickster exploits public service vulnerabilities globally, compromising over 874 systems in 58 countries through proxyjacking and cryptocurrency mining.
- Their stealth techniques include replacing legitimate system utilities (ps, pstree, pkill) with custom scripts to hide malware processes.
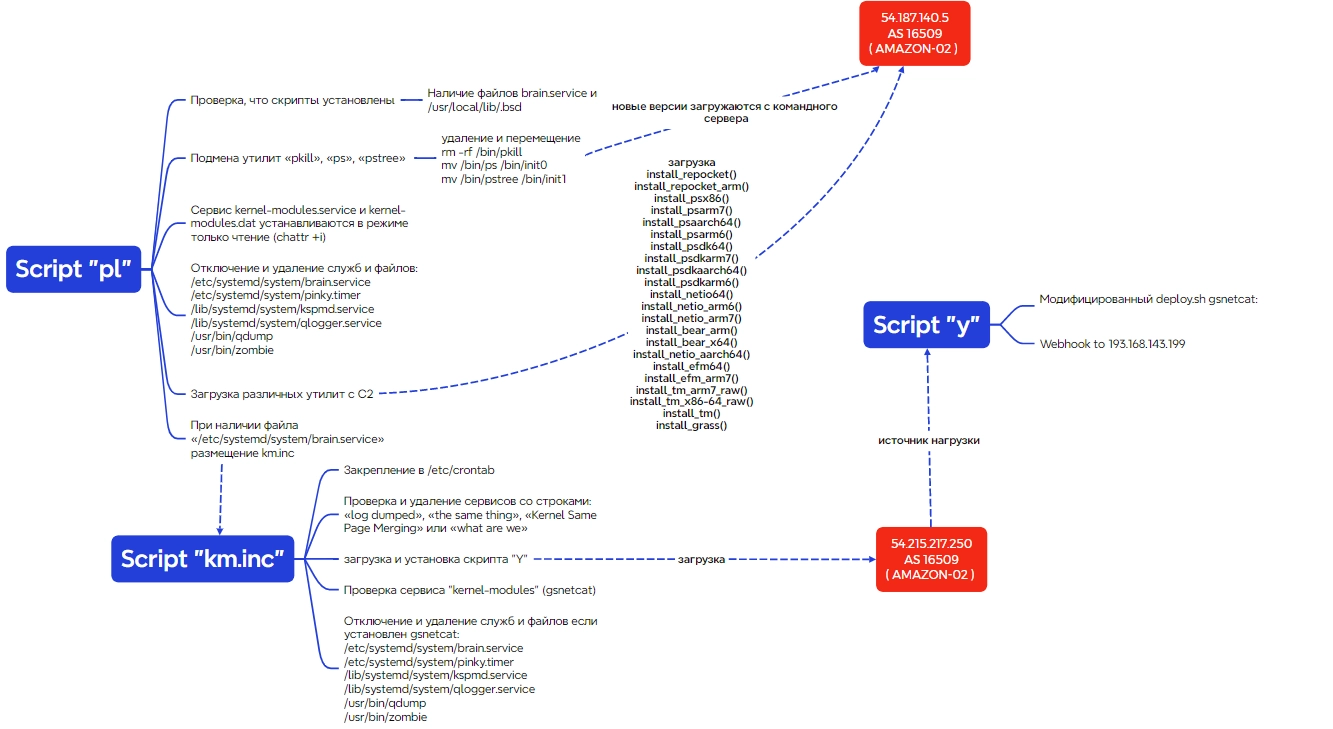
- They use a multi-stage automation chain of scripts (pl → km.inc → Y) to deploy and maintain their malware, including a modified deploy.sh with webhook telemetry.
- Monetization is mainly via proxyjacking tools associated with platforms like Packetshare.io, Pawns.app, Traffmonetizer, Earn.fm, Honeygain, and Repocket.
- Gs-netcat utility is heavily used for remote access and control, disguised as system files and services, including a Windows variant that runs hidden with PowerShell scripts.
- Persistence mechanisms include systemd services on Linux and scheduled tasks on Windows for continued operation of malware components.
- Advanced containerization and the use of Docker are utilized to increase automation and concealment of proxyjacking utilities.
MITRE Techniques
- [T1059.004] Command and Scripting Interpreter: Unix Shell – Execution of shell commands in attack chains.
- [T1059.001] Command and Scripting Interpreter: PowerShell – Usage of PowerShell scripts to launch malware components on Windows.
- [T1610] Deploy Container – Use of Docker containers to deploy and run proxyjacking utilities.
- [T1543.002] Create or Modify System Process: Systemd Service – Creation of systemd services to maintain persistence of gs-netcat and proxy tools.
- [T1053.003] Scheduled Task/Job: Cron – Scheduling of bash scripts via cron to maintain malware operations.
- [T1053.005] Scheduled Task/Job: Scheduled Task – Use of Windows Task Scheduler to persistently run malware components.
- [T1098.004] Account Manipulation: SSH Authorized Keys – Addition of attackers’ SSH keys for persistence using authorized_keys files.
- [T1554] Compromise Host Software Binary – Replacement of legitimate binaries (ps, pstree, pkill) with malicious scripts.
- [T1070.004] Indicator Removal: File Deletion – Deletion of older malware versions to evade detection.
- [T1070.009] Indicator Removal: Clear Persistence – Removal of old persistence files to maintain stealth.
- [T1222.002] File and Directory Permissions Modification – Setting immutable attributes to protect malicious files from deletion.
- [T1027.013] Obfuscated Files or Information: Encrypted/Encoded File – Base64 encoding used to obfuscate bash scripts.
- [T1036.01] Masquerading: Overwrite Process Arguments – Malware processes disguise themselves with legitimate process names using exec -a.
- [T1095] Non-Application Layer Protocol – Gs-netcat provides a covert channel for remote access.
- [T1021.004] Remote Services: SSH – Lateral movement using SSH with known credentials.
- [T1105] Ingress Tool Transfer – Downloading archives and utilities from attacker-controlled servers.
- [T1573.001] Encrypted Channel: Symmetric Cryptography – Encrypted communication via gs-netcat.
- [T1496.001] Resource Hijacking: Compute Hijacking – Use of cryptocurrency miners on infected hosts.
- [T1496.002] Resource Hijacking: Bandwidth Hijacking – Use of proxyjacking tools to monetize network traffic.
Indicators of Compromise
- [File Hashes] Various malware and script hashes involved in proxyjacking and mining — e.g., MD5 8f633ade35df4f992eb28a2c5bc37cef (XMRIG miner), a643960d177cac8dd51fd9b60bcacc10 (pl script), a0814428275cea453343d98d3e9655f5 (deploy.sh variant), and 63858243fb224a8e29ea5dd98112b579 (helper.exe).
- [IP Addresses] Command and control infrastructure including 54.187.140[.]5, 54.215.217[.]250, 193.168.143[.]199, and 67.165.216[.]118.
- [Domains] Miner pool address ghostrider.mine.zergpool[.]com used for XMR mining.
- [File Names/Paths] Malicious utilities and scripts such as /usr/bin/defunct (gs-netcat), /usr/lib/systemd/system/kernel-modules.service, /dev/shm/gr (pl script storage), and C:ProgramDataMSOrundll32.exe (Windows gs-netcat).
Read more: https://rt-solar.ru/solar-4rays/blog/5714/