In September 2024, Netskope Threat Labs disclosed the discovery of XWorm malware version 6.0, which introduces enhanced persistence, anti-analysis techniques, and AMSI bypass capabilities. This latest variant marks its process as critical to prevent termination and continues to execute primarily in memory, posing ongoing threats to targeted systems. #XWorm #AMSIbypass #ProcessProtection
Keypoints
- A new XWorm 6.0 variant was identified, demonstrating active malware development with new persistence and evasion features.
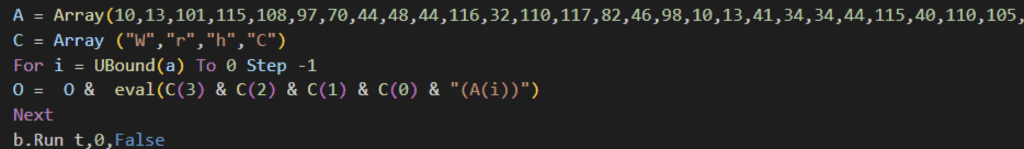
- The infection chain begins with a VBScript dropper leveraging obfuscated code and social engineering techniques.
- XWorm 6.0 achieves persistence by adding copies of update.vbs to TEMP and APPDATA folders and registering them in the Run registry key.
- The malware bypasses Antimalware Scan Interface (AMSI) by patching CLR.DLL in memory to disable AMSI scanning functionality.
- It marks its process as critical to prevent termination, requiring administrator privileges and causing system crashes if forcefully stopped.
- New anti-analysis techniques include self-termination on Windows XP systems and detection of data center IP addresses to avoid sandbox environments.
- Netskope Threat Protection products detect and provide coverage against XWorm using specific detection signatures and sandboxing solutions.
MITRE Techniques
- [T1059.005] Command and Scripting Interpreter: VBScript – Used in the initial infection chain to execute obfuscated VBScript payloads. (“The VBScript embeds and reconstructs another obfuscated VBScript payload at runtime… execute it using the eval function.”)
- [T1175] Browser Extensions – Persistence via Run registry key modification. (“Adds persistence on the victim’s device by adding the update.vbs…to the Run registry key.”)
- [T1140] Deobfuscate/Decode Files or Information – The malware reconstructs VBScript from character arrays and base64 decoding for configuration retrieval. (“The application begins by retrieving its configuration from a base-64 encoded string.”)
- [T1562.001] Impair Defenses: Disable or Modify Tools – Bypass of AMSI by patching CLR.DLL in memory. (“It searches for CLR.DLL… replaces the string ‘AmsiScanBuffer’ with null bytes.”)
- [T1543.003] Create or Modify System Process: Windows Service – XWorm marks itself as a critical process to prevent termination. (“It invokes EnterDebugMode to enable SeDebugPrivilege… flag the XWorm process as critical.”)
- [T1497.001] Virtualization/Sandbox Evasion: System Checks – Terminates itself when detecting Windows XP or datacenter IP addresses to evade analysis environments. (“XWorm now terminates itself when it detects execution on Windows XP… uses the IP-API service to check if the device’s IP belongs to data centers.”)
Indicators of Compromise
- [File Name] VBScript and PowerShell files used in infection – update.vbs, wolf-8372-4236-2751-hunter-978-ghost-9314.ps1
- [File Name] XWorm binary – Microsoft.exe (version 6.0 sample)
- [Registry Key] Persistence via Registry Run key – entries for update.vbs in TEMP and APPDATA folders
- [Domain] Command and Control server – hardcoded C2 server address (specific domain not provided)
Read more: https://www.netskope.com/blog/xworm-v6-0-enhanced-malware-protection-and-stealthy-delivery