The JSCEAL campaign employs compiled JavaScript malware delivered via malicious advertisements impersonating popular cryptocurrency trading apps, targeting millions of users predominantly in the EU. This sophisticated campaign uses multi-layered infection chains, anti-analysis techniques, and Node.js to execute stealthy information stealing and remote access operations. #JSCEAL #CompiledJavaScript #CryptoMalware #NodeJS
Keypoints
- JSCEAL is a large-scale malware campaign active since March 2024, targeting users of nearly 50 cryptocurrency trading apps via fake installers promoted in over 35,000 malicious ads in early 2025.
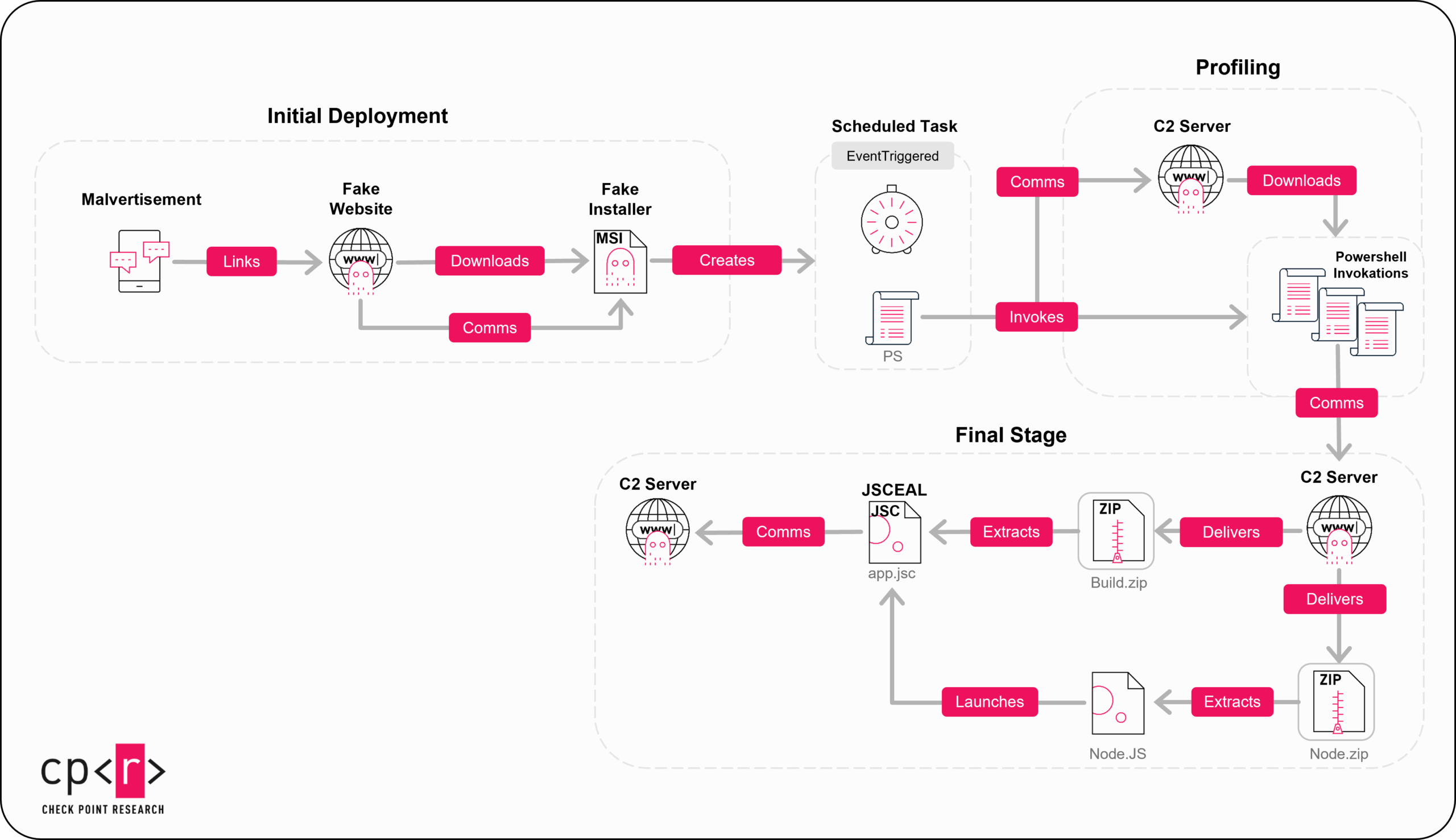
- The infection chain involves multi-layered deployment: initial malicious MSI installers, profiling scripts, and a final compiled JavaScript (JSC) payload executed via Node.js.
- The campaign leverages unique anti-evasion techniques including requiring parallel execution of the fake website and installer to complicate detection and analysis.
- Malicious advertisements use stolen or fake social media accounts with a redirection infrastructure consisting of specially structured domain names to deliver fake landing pages or decoys.
- The final JSCEAL payload acts as an info-stealer and RAT, capable of man-in-the-browser and man-in-the-middle attacks, stealing credentials, crypto wallets, Telegram accounts, screenshots, and keylogging data.
- JSCEAL uses extensive obfuscation and a low detection rate due to compiling JavaScript into bytecode, making static analysis difficult but can be decompiled using tools like VIEW8.
- The campaign’s infrastructure includes numerous C2 domains, redirection domains, signed MSI installers with legitimate certificates, and a Node.js runtime alongside complex PowerShell profiling scripts.
MITRE Techniques
- [T1041] Exfiltration Over C2 Channel – JSCEAL exfiltrates collected machine and user data to command and control servers over encrypted channels. (‘extracts the MachineGuid value and compiles information sent to operators’).
- [T1086] PowerShell – Scheduled tasks run encoded PowerShell scripts that disable Windows Defender exclusions and maintain persistent backdoor functionality. (‘Add-MpPreference -ExclusionProcess … -Force’).
- [T1059.007] Command and Scripting Interpreter: JavaScript – Malicious compiled JavaScript payload executed via Node.js, evading detection through obfuscation and compiled bytecode. (‘JSCEAL executes the final payload using Node.exe and app.jsc’).
- [T1204.002] User Execution: Malicious File – Victims are tricked into executing MSI installers from fake websites promoted by malicious social media advertisements. (‘malicious MSI installer files downloaded from attacker-controlled sites’).
- [T1176] Browser Extensions – JSCEAL manipulates crypto-related browser extensions to steal sensitive data. (‘Manipulates crypto-related web extensions’).
- [T1098] Account Manipulation – Actors use stolen or fake social media accounts for propagation of malicious advertisements. (‘The actors use either stolen accounts or newly created ones to write malicious posts’).
- [T1036] Masquerading – Fake apps impersonate nearly 50 legitimate cryptocurrency trading platforms to lure victims. (‘Impersonate almost 50 common cryptocurrency trading apps’).
- [T1071.001] Application Layer Protocol: Web Protocols – Communication with C2 servers uses HTTPS, including DNS over HTTPS to Cloudflare DNS 1.1.1.1. (‘starts communicating with Cloudflare DNS 1.1.1.1 over HTTPS’).
- [T1543.003] Create or Modify System Process: Windows Service – The campaign creates scheduled tasks that trigger infection stages and maintain persistence. (‘creates scheduled task to launch PowerShell infection chain’).
Indicators of Compromise
- [Domains] JSCEAL C2 and infrastructure – vertical-scaling[.]com, ggr-lach[.]com, llm-0014[.]com, hat-kett[.]com, 7777-202[.]com.
- [Domains] Intermediate C2 and delivery – resolve-ns[.]pages[.]dev, hasv[.]pages[.]dev, r2[.]ohyoulookstupid[.]win, test-ex-1[.]pages[.]dev, 87-899[.]help.
- [Domains] Malicious redirection domains with structured names – app-pc-windows[.]com, app-windows[.]com, download-apps-windows[.]com, downloads-desktop-windows[.]com, desktop-app-pc[.]com, pc-download-desktop[.]com.
- [File hashes] MSI installers – examples include a696d03aeb1bde633b674bdd640a1a313cae7da711d99cfba3fd06f02d3864de, e881682b59640c05cd540696955a849610260415e576f79b62383108c1aa3354.
- [File hashes] Build.zip payload archive – b90e3aaae14e7787e5ea4a6d4beee672049bd5eb05427f2c80b64f605860d2b8, f6c670e65765d10a5ca0205a6ece3a3e6c7c730b0a8534c5adef4a3cbf06eb9c.
- [File hashes] JSCEAL final payload example hashes – 62ba626bce09db5f8750938edced3768b401084a7d6584cd6ff9d53d2517781d, 95b39a0bad021f33e08df042b02d3267faee7bbc3e3080dda295c35b464dd607.
Read more: https://research.checkpoint.com/2025/jsceal-targets-crypto-apps/