In July 2025, eSentire’s Threat Response Unit (TRU) identified the use of SocGholish malware combined with a new python-based password stealer targeting Chrome and Edge browsers, linked to ex-affiliates of the RansomHub group now called ShadowCoil. The TRU provided a detailed unpacking process, detection Yara rule, and mitigation recommendations to enhance defense against this evolving threat. #SocGholish #ShadowCoil #RansomHub
Keypoints
- In late July 2025, eSentire TRU detected SocGholish malware distributing a python-based password stealer targeting Google Chrome and Microsoft Edge.
- The python stealer is linked with medium confidence to ShadowCoil, an ex-affiliate group of the RansomHub Ransomware-as-a-Service operation.
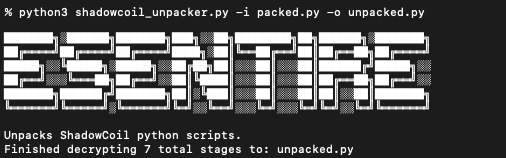
- The malware uses a complex recursive unpacking process involving Base85, AES-256 GCM, AES-128 CTR, ChaCha20, HKDF/Blake3/XOR, and ZLIB inflation.
- The tool extracts and decrypts encrypted browser master keys and passwords stored in browser data files using Windows DPAPI.
- eSentire provided a custom Yara rule to detect the packed python scripts associated with ShadowCoil’s tools.
- Recommended mitigations include redirecting suspicious script file executions to notepad, disabling wscript.exe, disabling browser password managers, and implementing MLA and endpoint detection technologies.
- eSentire’s 24/7 SOC team rapidly contained infected hosts and assisted customers with remediation.
MITRE Techniques
- [T1056] Input Capture – The malware captures saved passwords from Google Chrome and Microsoft Edge by decrypting browser login data files (“…enumerating directories matching ‘User Data’ for Google Chrome and Microsoft Edge…decrypt stored usernames, passwords, and associated URLs…”).
- [T1555] Credentials from Password Stores – The tool extracts and decrypts the encrypted master key from browser Local State files using DPAPI CryptUnprotectData (“…parse each browser’s Local State file…calling the DPAPI CryptUnprotectData to decrypt it…”).
- [T1140] Deobfuscate/Decode Files or Information – Recursive unpacking stages using Base85 decoding, AES-256 GCM, AES-128 CTR, ChaCha20, HKDF/Blake3/XOR, and ZLIB decompression (“…Each stage in the recursive unpacking process first converts the string passed to pc_start() to decode from Base85… uses AES-256 GCM, ChaCha20, AES-128 CTR decryption followed by ZLIB Inflation…”).
- [T1071] Application Layer Protocol – SocGholish is used for initial access distribution via JScript files (“…JScript files continue to be leveraged by SocGholish campaigns for Initial Access.”).
- [T1027] Obfuscated Files or Information – Malware uses sophisticated packing and obfuscation to avoid detection (“…packed python scripts that leverage the packer shown in Figure 2…”).
Indicators of Compromise
- [File Hashes] Python password stealer – hash samples available via VirusTotal link (exact hashes not listed, refer to TRU report).
- [Yara Rule] Detection of packed Python scripts – ShadowCoil_Packed_Python Yara rule signature with strings “exec(pc_start(“, “get_hw_key():”, “TracerPid:” targeting RansomHub ex-affiliate tools.
- [File Names & Extensions] Suspicious script file extensions targeted for mitigation – js, jse, vbs, vbe, wsf, hta, and wsh used by SocGholish campaigns.