An ISO image targeting Chinese-speaking users utilizes a malicious DLL sideloaded by a legitimate Alibaba executable to deploy a Cobalt Strike Beacon with a decoy PDF. The threat leverages an LNK file named after the Zhengzhou Commodity Exchange to initiate execution, disguising malicious traffic as Bilibili video sharing platform communications. #CobaltStrike #SLOWTEMPEST #ZhengzhouCommodityExchange
Keypoints
- The ISO image contains a deceptive LNK file that executes a legitimate Alibaba executable (config.exe) used for DLL sideloading.
- The malicious DLL loader (arphadump64.dll) includes anti-analysis techniques and checks for a minimum of 6GB RAM before executing payloads.
- The payload is encrypted in base.dll and decrypted via a rolling XOR key before being executed in memory as a Cobalt Strike Beacon.
- The Cobalt Strike Beacon communicates with a command and control server (m.123huodong.com.cloud.cdntip.com.s2-web.dogedns[.]com) disguised as Bilibili traffic.
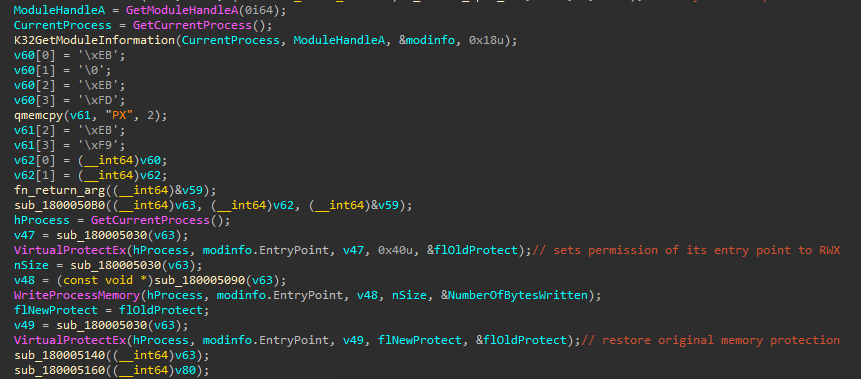
- The loader implements an infinite loop patch on config.exe to maintain persistence and avoid crashes during malicious execution.
- This activity shows overlaps with the previously reported SLOW#TEMPEST campaign targeting Chinese users, including folder structure and watermark similarities.
- Palo Alto Unit42 reported a related loader sideloaded by DingTalk.exe that also checks for system memory before payload execution.
MITRE Techniques
- [T1566] Phishing – Use of a malicious ISO image containing a deceptive LNK file named after Zhengzhou Commodity Exchange to lure victims (‘The LNK file… triggers the infection chain’).
- [T1055] Process Injection – Execution of decrypted payload in memory using CreateThread and memory allocation with PAGE_EXECUTE_READWRITE (‘payload is copied into newly-allocated memory with PAGE_EXECUTE_READWRITE permissions, and a new thread is created’).
- [T1070] Indicator Removal on Host – Implementation of an infinite loop patch to prevent normal execution and detection of config.exe (‘loader implements an infinite loop patch in the entry point of the loading executable’).
- [T1027] Obfuscated Files or Information – Use of junk code and XOR encryption to confuse analysis and protect payload (‘arphadump64.dll is a malicious loader with significant amount of junk code… Payload read from base.dll is XOR decrypted’).
- [T1047] Windows Management Instrumentation – The loader calls GlobalMemoryStatusEx API to check system memory before proceeding (‘The loader calls the GlobalMemoryStatusEx API to retrieve the amount of RAM memory… to check if the system has 6GB or more’).
- [T1105] Ingress Tool Transfer – The initial access gains persistence by sideloading a malicious DLL through a legitimate Alibaba executable (‘DLL sideloading of Cobalt Strike beacons executed from an LNK file’).
Indicators of Compromise
- [File Hash] ISO image – 6573136f9b804ddc637f6be3a4536ed0013da7a5592b2f3a3cd37c0c71926365
- [File Hash] LNK file (Malicious shortcut) – c28bd1a57e80861fce2597b1f5155a687bef434b0001632c8a53243718f5f287
- [File Hash] Malicious DLL (arphadump64.dll) – a41c06ad948f3a21496e4d1f6b622ca84a365dd2087b710ed3e7f057e7a2a3f8
- [File Hash] Legitimate executable (config.exe) – 1cb0560f614cc850422171ffe6b0b9f6b9ceaec4fe3516bc8493f253076470ab4
- [Domain] C2 Server – m.123huodong.com.cloud.cdntip.com.s2-web.dogedns[.]com (used by Cobalt Strike Beacon)
- [File Hash] base.dll (contains encrypted payload) – 5efbd54a3a51d96fbc8e65815df2f0d95af21a34b99b8dc9a38590fb6d2094f8